At minimum 17 malware-laced packages have been found on the NPM package deal Registry, incorporating to a new barrage of destructive software program hosted and shipped by means of open-supply software package repositories these kinds of as PyPi and RubyGems.
DevOps business JFrog claimed the libraries, now taken down, were being designed to grab Discord access tokens and ecosystem variables from users’ pcs as properly as achieve complete handle around a victim’s process.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
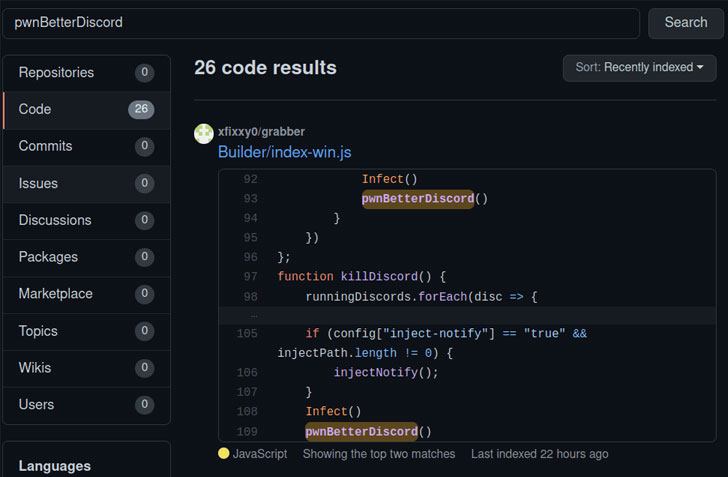
“The packages’ payloads are various, ranging from infostealers up to total distant accessibility backdoors,” researchers Andrey Polkovnychenko and Shachar Menashe explained in a report released Wednesday. “Furthermore, the deals have various infection methods, like typosquatting, dependency confusion and trojan performance.”
The checklist of packages is underneath –
- prerequests-xcode (model 1..4)
- discord-selfbot-v14 (variation 12..3)
- discord-lofy (model 11.5.1)
- discordsystem (edition 11.5.1)
- discord-vilao (edition 1..)
- fix-error (edition 1..)
- wafer-bind (version 1.1.2)
- wafer-autocomplete (model 1.25.)
- wafer-beacon (model 1.3.3)
- wafer-caas (edition 1.14.20)
- wafer-toggle (model 1.15.4)
- wafer-geolocation (model 1.2.10)
- wafer-image (edition 1.2.2)
- wafer-kind (edition 1.30.1)
- wafer-lightbox (model 1.5.4)
- octavius-community (variation 1.836.609)
- mrg-information-broker (edition 9998.987.376)
As prior study has recognized, collaboration and communication applications like Discord and Slack have turn out to be helpful mechanisms for cybercriminals, with Discord servers built-in into the attack chains for remotely managing the infected devices and even to exfiltrate data from the victims.
“Cyber criminals are making use of Discord CDN to host destructive data files as properly as for command-and-manage (C&C) interaction,” cybersecurity agency Zscaler famous in an analysis earlier this February. “Due to the static content material distribution provider, it is really well-liked among the danger actors to host malicious attachments that stay publicly obtainable even just after getting rid of precise documents from Discord.”

In light of these disclosures, it really is no shock that the theft of Discord entry tokens could empower danger actors to use the system as a covert knowledge exfiltration channel, distribute malware to other Discord consumers, and even market Discord Nitro top quality accounts to other third-parties, who can then use them for their very own campaigns.
Even additional troublingly, the deal “prerequests-xcode” functioned as a full-fledged remote access trojan, a Node.JS port of DiscordRAT, that is equipped to capture screenshots, obtain clipboard knowledge, execute arbitrary VBScript and PowerShell code, steal passwords, and obtain destructive information, properly granting the adversary the capability to get in excess of the developer’s technique.
If something, the development provides to an significantly “disturbing trend” of applying rogue deals as a stealthy compromise vector to aid an array of malicious actions, which include source-chain attacks.
“General public repositories have develop into a helpful instrument for malware distribution: the repository’s server is a trustworthy resource, and interaction with it does not raise the suspicion of any antivirus or firewall,” the scientists mentioned. “In addition, the simplicity of installation through automation resources these types of as the NPM shopper, gives a ripe attack vector.”
Discovered this report interesting? Follow THN on Facebook, Twitter and LinkedIn to browse additional exceptional content material we write-up.
Some pieces of this write-up are sourced from:
thehackernews.com


 SonicWall Urges Customers to Immediately Patch Critical SMA 100 Flaws
SonicWall Urges Customers to Immediately Patch Critical SMA 100 Flaws