A full of 108.9 million accounts ended up breached in the third quarter of 2022, a 70% enhance in comparison to the earlier quarter. The major 5 nations and locations most affected by data breaches …
Apple Fixes Actively Exploited iOS and iPadOS Zero-Day Vulnerability
Apple produced new updates on Monday to patch a zero-day vulnerability in iOS and iPadOS products that has reportedly been actively exploited in the wild. The out-of-bounds publish issue in the …
Apple Fixes Actively Exploited iOS and iPadOS Zero-Day VulnerabilityRead More
POS Malware Used to Steal Details of Over 167,000 Credit Cards
Two point-of-sale (POS) malware resources have been deployed by a risk actor to steal the information and facts of over 167,000 credit score cards from payment terminals. The findings come from …
POS Malware Used to Steal Details of Over 167,000 Credit CardsRead More
A strategic guide for controlling and securing your data
A strategic guideline for managing and securing your data Some elements of this article are sourced from: www.itpro.co.uk …
A strategic guide for controlling and securing your dataRead More
22-Year-Old Vulnerability Reported in Widely Used SQLite Database Library
A high-severity vulnerability has been disclosed in the SQLite databases library, which was introduced as part of a code modify dating all the way back again to Oct 2000 and could allow attackers to …
22-Year-Old Vulnerability Reported in Widely Used SQLite Database LibraryRead More
Database and big data security
Databases and massive details stability Some areas of this report are sourced from: www.itpro.co.uk …
Hive Ransomware Hackers Begin Leaking Data Stolen from Tata Power Energy Company
The Hive ransomware-as-a-service (RaaS) team has claimed duty for a cyber attack versus Tata Energy that was disclosed by the organization less than two months ago. The incident is said to have …
Hive Ransomware Hackers Begin Leaking Data Stolen from Tata Power Energy CompanyRead More
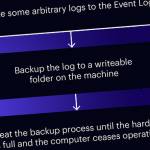
Researchers Detail Windows Event Log Vulnerabilities: LogCrusher and OverLog
Cybersecurity researchers have disclosed particulars about a pair of vulnerabilities in Microsoft Windows, one particular of which could be exploited to result in a denial-of-assistance (DoS). The …
Researchers Detail Windows Event Log Vulnerabilities: LogCrusher and OverLogRead More
FTC orders Uber-owned Drizly to improve “lax” data protection approach following 2020 breach
Getty PhotosThe Federal Trade Commission (FTC) has ordered Uber-owned delivery corporation Drizly to revamp its information-managing practises following a big 2020 facts breach.Drizly, an Uber …
How the Software Supply Chain Security is Threatened by Hackers
Introduction In several ways, the software source chain is similar to that of made products, which we all know has been mainly impacted by a international pandemic and shortages of raw supplies. Even …
How the Software Supply Chain Security is Threatened by HackersRead More
Cybercriminals Used Two PoS Malware to Steal Details of Over 167,000 Credit Cards
Two stage-of-sale (PoS) malware variants have been set to use by a threat actor to steal facts linked to more than 167,000 credit score cards from payment terminals. According to …
Cybercriminals Used Two PoS Malware to Steal Details of Over 167,000 Credit CardsRead More
2022 Strategic roadmap for data security platform convergence
2022 Strategic roadmap for knowledge security system convergence Some elements of this report are sourced from: www.itpro.co.uk …
2022 Strategic roadmap for data security platform convergenceRead More
Apple patches actively exploited iPhone, iPad zero-day and 18 other security flaws
ShutterstockApple has introduced an update offering a variety of patches for iOS and iPadOS, which include just one zero-day that “may have been actively exploited".Tracked as CVE-2022-42827, the …
Apple patches actively exploited iPhone, iPad zero-day and 18 other security flawsRead More
Ukraine Warns of Cuba Ransomware Campaign
The Ukrainian authorities have posted data warning of a new ransomware marketing campaign in opposition to companies in the war-torn region. In a brief observe, the Ukrainian CERT mentioned it had …
Five common data security pitfalls
Five prevalent facts security pitfalls Some areas of this write-up are sourced from: www.itpro.co.uk …
Hive ransomware group claims cyber attack on India’s Tata Power
Getty VisualsThe Hive ransomware team has claimed an attack on Tata Power, a primary Indian electrical power firm, and encrypted its units with ransomware.Hive claimed to have encrypted the systems of …
Hive ransomware group claims cyber attack on India’s Tata PowerRead More
ExtraHop partners with Splunk SOAR to offer visibility into encrypted network traffic
ShutterstockExtraHop and Splunk SOAR have announced a new partnership that aims to present greater visibility into encrypted targeted visitors for security gurus. The collaboration focuses on a new …
ExtraHop partners with Splunk SOAR to offer visibility into encrypted network trafficRead More
Iranian Atomic Energy Agency Admits Email Hack
The Atomic Electrical power Firm of Iran (AEOI) has blamed an unnamed “foreign country” for thieving and leaking sensitive internal email messages – an procedure which an Iranian hacktivist team …
US Charges Two Chinese Agents in Huawei Obstruction Case
The US has introduced a different blockbuster set of prices in opposition to Chinese nationals in a few instances, such as a person in which two brokers are reported to have compensated bribes for …
US Charges Two Chinese Agents in Huawei Obstruction CaseRead More
The ultimate guide to deleting yourself from social media
ShutterstockPrivate facts has in no way been a lot more available. Your social media profile and posts can give away all sorts of particulars to individuals you know, and folks you really don't – from …
The ultimate guide to deleting yourself from social mediaRead More