A danger actor with suspected ties to Pakistan has been striking authorities and strength companies in the South and Central Asia areas to deploy a distant entry trojan on compromised Windows techniques, according to new investigation.
“Most of the organizations that exhibited indicators of compromise were in India, and a tiny variety ended up in Afghanistan,” Lumen’s Black Lotus Labs claimed in a Tuesday evaluation. “The potentially compromised victims aligned with the federal government and ability utility verticals.”
Some of the victims consist of a overseas federal government corporation, a power transmission organization, and a energy era and transmission business. The covert operation is said to have begun at the very least in January 2021.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

The intrusions are notable for a selection of explanations, not least for the reason that in addition to its remarkably-specific character, the techniques, strategies, and treatments (TTPs) adopted by the adversary count on repurposed open up-supply code and the use of compromised domains in the same nation as the focused entity to host their destructive files.
At the exact time, the team has been thorough to hide their action by modifying the registry keys, granting them the potential to preserve persistence on the target machine without attracting attention surreptitiously.
Explaining the multi-phase an infection chain, Lumen famous the marketing campaign “resulted in the sufferer downloading two agents just one resided in-memory, whilst the 2nd was aspect-loaded, granting menace actor persistence on the contaminated workstations.”
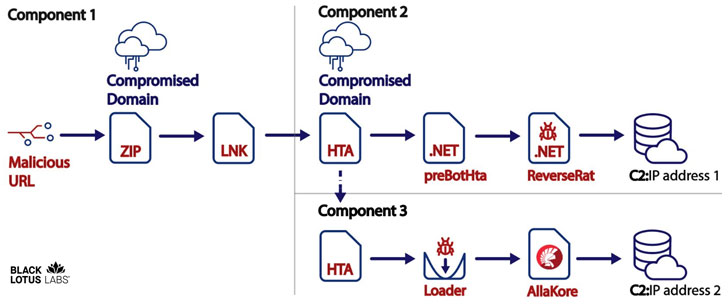
The attack commences with a malicious connection despatched through phishing e-mails or messages that, when clicked, downloads a ZIP archive file containing a Microsoft shortcut file (.lnk) and a decoy PDF file from a compromised domain.
The shortcut file, moreover exhibiting the benign doc to the unsuspecting receiver, also can take care of stealthily fetching and operating an HTA (HTML software) file from the very same compromised website.
The entice documents mainly describe gatherings catering to India, disguising as a user guide for registering and booking an appointment for COVID-19 vaccine by means of the CoWIN on line portal, whilst a number of some others masquerade as the Bombay Sappers, a regiment of the Corps of Engineers of the Indian Army.

Irrespective of the PDF doc shown to the sufferer, the HTA file — alone a JavaScript code primarily based on a GitHub undertaking called CactusTorch — is leveraged to inject a 32-bit shellcode into a functioning system to eventually set up a .NET backdoor known as ReverseRat that runs the common spy ware gamut, with capabilities to seize screenshots, terminate processes, execute arbitrary executables, conduct file functions, and upload facts to a remote server.
The customized-produced framework also comes with a 3rd element in which a next HTA file is downloaded from the identical domain to deploy the open-supply AllaKore distant agent, most likely in an substitute attempt to sustain accessibility to the compromised network.
“Though this menace actor’s targets have as a result considerably remained within just the South and Central Asian areas, they have confirmed helpful at getting access to networks of curiosity,” the researchers claimed. “Irrespective of previously relying upon open-supply frameworks such as AllaKore, the actor was ready to stay efficient and extend its abilities with the progress of the Svchostt agent and other factors of the ReverseRat venture.”
Uncovered this posting exciting? Comply with THN on Facebook, Twitter and LinkedIn to browse a lot more distinctive written content we article.
Some pieces of this short article are sourced from:
thehackernews.com


 EU Proposes Joint Cyber Unit Amid Rising Attacks
EU Proposes Joint Cyber Unit Amid Rising Attacks