A new zero-day vulnerability has been disclosed in Palo Alto Networks GlobalProtect VPN that could be abused by an unauthenticated network-primarily based attacker to execute arbitrary code on affected gadgets with root person privileges.
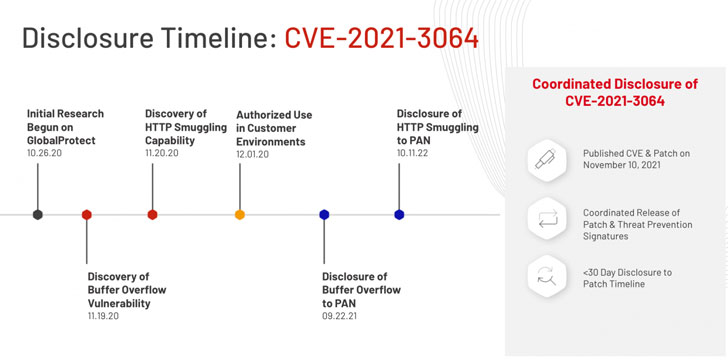
Tracked as CVE-2021-3064 (CVSS score: 9.8), the security weakness impacts PAN-OS 8.1 variations before than PAN-OS 8.1.17. Massachusetts-primarily based cybersecurity business Randori has been credited with getting and reporting the issue.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
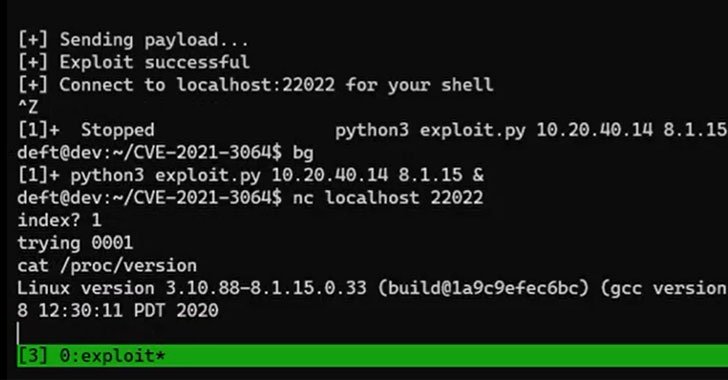
“The vulnerability chain is made up of a strategy for bypassing validations made by an external web server (HTTP smuggling) and a stack-primarily based buffer overflow,” Randori scientists reported. “Exploitation of the vulnerability chain has been demonstrated and permits for distant code execution on both equally actual physical and digital firewall products.”
Complex aspects relevant to CVE-2021-3064 have been withheld for 30 days to prevent menace actors from abusing the vulnerability to stage genuine-planet attacks.
The security bug stems from a buffer overflow that happens though parsing person-provided enter. Thriving exploitation of the flaw necessitates that the attacker strings it with a system recognized as HTTP smuggling to attain remote code execution on the VPN installations, not to mention have network accessibility to the machine on the GlobalProtect support default port 443.

“A memory corruption vulnerability exists in Palo Alto Networks GlobalProtect portal and gateway interfaces that permits an unauthenticated network-centered attacker to disrupt process procedures and possibly execute arbitrary code with root privileges,” Palo Alto Networks reported in an impartial advisory. “The attacker will have to have network access to the GlobalProtect interface to exploit this issue.”
In light of the truth that VPN devices are worthwhile targets for destructive actors, it’s remarkably advisable that people transfer swiftly to patch the vulnerability. As a workaround, Palo Alto Networks is advising affected corporations to allow risk signatures for identifiers 91820 and 91855 on targeted traffic destined for GlobalProtect portal and gateway interfaces to avert any opportunity attacks against CVE-2021-3064.
Located this short article exciting? Abide by THN on Fb, Twitter and LinkedIn to read through extra special content material we submit.
Some components of this write-up are sourced from:
thehackernews.com

 Dallas Police Surveillance Footage Leaked
Dallas Police Surveillance Footage Leaked