So, you’ve been thinking about obtaining a Penetration Check performed on your Amazon Web Services (AWS) surroundings. Great! What really should that include precisely?
There are a lot of possibilities available, and recognizing what you require will assistance you make your normally confined security spending budget go as significantly as achievable. Broadly, the essential aim spots for most penetration tests involving AWS:
- Your externally obtainable cloud infrastructure
- Any application(s) you happen to be creating or hosting
- Your inner cloud infrastructure
- Your AWS configuration by itself
- Tricks management
We will appear at each individual a single, setting up with the most crucial:

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
External Infrastructure
The very good news listed here is that, by default, AWS does its very best to help you stay secure. For case in point, the default security teams will not allow your EC2 circumstances acquire communication from the outside the house entire world unless you actively specify it by incorporating more principles.
That claimed, AWS even now makes it possible for you lots of rope to hold your self with if you are not mindful. Common faults like engineering teams altering security groups to allow all inbound accessibility are nevertheless a trouble, and the nature of DevOps implies providers can be coming up and down often, not generally with the awareness of group administrators.
Nevertheless, there is no easier way for a hacker to compromise you than locating a uncomplicated security weak point missed in your internet-struggling with infrastructure, whether or not that is an uncovered databases or computer software with recognized vulnerabilities. Attackers have the most payoff for the minimum effort, so the chance of this going on is the maximum — as a result should really be your very first port of simply call to fix.
It can be challenging to remain on prime of cloud vulnerability administration owing to the dynamic mother nature of these units and continual improvements to your environment, with new vulnerabilities currently being released day by day. On the other hand, modern day vulnerability scanning alternatives, these types of as Intruder, are customised to your cloud ecosystem. You should take into account using a person of these applications in advance of functioning a penetration exam, as they enable constantly handle vulnerabilities in your infrastructure with computerized scans.
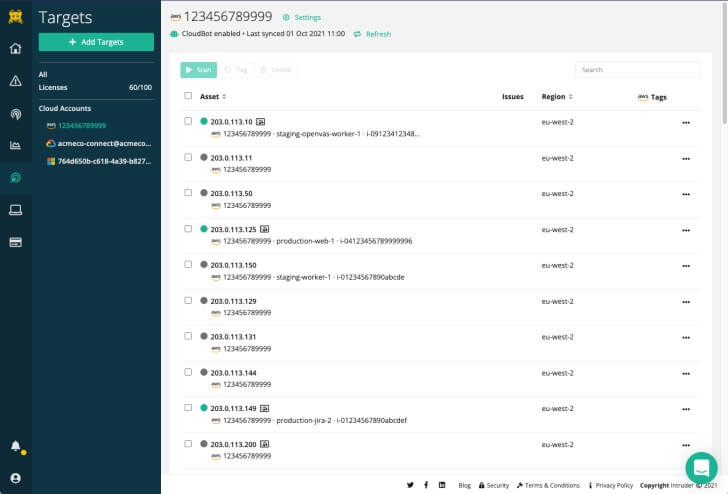 Intruder can sync targets from significant cloud companies, and hold your targets sync’d when new devices are included to your cloud accounts employing the CloudBot operation. This ensures new units are integrated in foreseeable future vulnerability scans.
Intruder can sync targets from significant cloud companies, and hold your targets sync’d when new devices are included to your cloud accounts employing the CloudBot operation. This ensures new units are integrated in foreseeable future vulnerability scans.
As it is your most uncovered attack surface area, you likely wouldn’t want to remove your exterior infrastructure from the scope of any pen-test. And, continue to, you shouldn’t assign a massive proportion of your spending plan to it if probable, and don’t be expecting to see quite a few results further than what you’ve got appear to count on from your vulnerability scanning equipment.
Web Software
Several firms use AWS to host web software(s) for consumers, employees, or companions. Sad to say, web applications, designed to be exposed by their nature, present attackers with the second least complicated way into your methods – if they’re not made securely. This tends to make them the next most vital attack surface area following your exterior infrastructure.
Illustrations of these kinds of attacks consist of the Kaseya incident in 2021, where attackers successfully compromised Kaseya and distributed ransomware to its shoppers in a source-chain attack. The suitable-wing social media web-site Gab was also compromised early in 2021 and experienced 70GB of delicate person facts leaked due to the fact of a SQL injection vulnerability. Heading even more again, the famous TalkTalk hack, a 17-yr-old customer managed to find his way into their buyer database and extract millions of information.
Normally take into consideration the effects and probability of an attack at this layer. Irrespective of whether your software is fully obtainable to the general public or a limited set of prospects only should factor into your final decision building. For instance, applications with “no cost trials” would let an attacker to indicator up and start out having a go. B2B solutions for paying out buyers/companions may possibly have a decreased threat profile, though nonetheless not negligible, and employees’ apps are however reduced. On the other hand, some apps incorporate these kinds of delicate info that the influence may possibly very seriously outweigh the probability.
So, dependent on the risk profile of your application, you may well locate that if you can only afford to pay for penetration testers to do a couple of days do the job, this is highly probable where you ought to be searching to expend their time. Even though automated tools exist for this sort of tests and can be handy to deal with the hole involving penetration checks, absolutely nothing on the current market nowadays can change the good quality of a human tester who will comprehend the organization logic of your application and appear for methods to effects it.
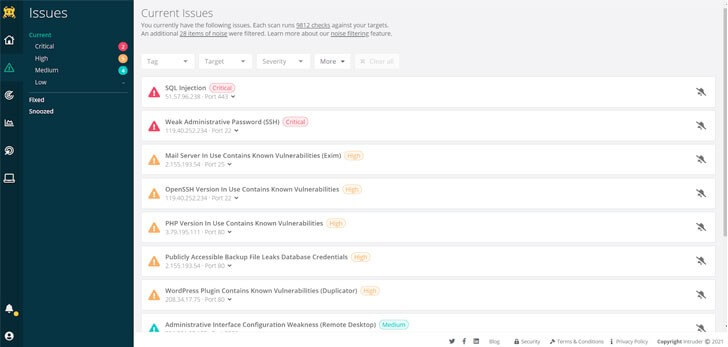 Intruder works by using a special algorithm to prioritise issues that go away your programs exposed, earning it significantly simple to locate out what offers the best risk.
Intruder works by using a special algorithm to prioritise issues that go away your programs exposed, earning it significantly simple to locate out what offers the best risk.
Inner Infrastructure
The future layer of attack is the infrastructure where your software is built. Having included off the exterior infrastructure, the inner aspect is only available if an attacker already has breached your defences by some means. So, the threat profile below is secondary to the past two.
Previous-school penetration assessments of details centres or corporate networks frequently revolve around getting a foothold, then “pivoting” from one particular process to yet another, eventually leading to full-blown compromise of administrator accounts or critical devices. Below is exactly where AWS environments can differ from common penetration tests, though, as AWS networks’ program-defined mother nature typically implies tighter controls are taken care of in between networks, and lateral motion is a challenge. For instance, as soon as once again, the default “start-wizard-#” security groups really don’t let your EC2 scenarios talk to every other except if you actively specify it by incorporating them to a VPC or by introducing further procedures. Nonetheless, all but the most straightforward of AWS accounts get away with this kind of easy configurations. In addition, as proven in the Cash A person breach in 2019, attackers can compromise IAM part qualifications and use these to entry means.
Moreover, the baked-in accessibility and security controls in AWS mean that you might be far less probably to have established compromised ecosystem-huge “administrator” accounts by way of any of your EC2 scenarios. As an alternative, it’s a lot more probably that you are employing privileged AWS accounts to do this, and so an AWS Config Critique can incorporate significantly additional price than an “interior” infrastructure examination.
Similarly, though unpatched software program and insecure services on interior methods can be an issue, it depends to what extent you’ve got established non-public networks in your AWS surroundings and what methods can obtain many others. It truly is also worthy of comprehension if you have a position-to-point VPN involving your on-premises network and your cloud environments. If you do, an inside penetration examination may be suitable to obtain out what an attacker can bridge the hole concerning these two networks.
The additional complexity you have, the extra an inside penetration check could include worth. For example, suppose you are managing a handful of EC2’s every single with their security team, or you happen to be making use of some of AWS’s shared/managed providers like lambda functions – you could want to skip a standard “interior” penetration check and look at a config review as an alternative.
AWS Config
As described, out of the box AWS does a great deal for you in conditions of security, but an AWS config evaluation can tell you if you have established things up in a strong way.
Vintage illustrations of poor AWS config are the uncovered S3 buckets you typically listen to of or a deficiency of multi-factor authentication to access the AWS console. But, it can also incorporate factors like admin accounts with as well a lot of consumers getting in a position to accessibility them or more sophisticated IAM policies like how a read through-only obtain policy might enable an attacker to gain supplemental privileges in your setting.
Once once again, this can typically descend into spending a person to notify you what you previously know (or could conveniently have observed out). Right before you commission a penetration check, test out some no cost applications (a fast google throws up a range of options). The methodology is probable the identical, and you could have the answers to your questions now.
If you happen to be not self-assured in the security stakes or will need a 3rd-party audit for compliance motives, it is worthwhile to link with a cyber-security specialist, like Intruder, to uncover how they can enable.
Techniques Management
Secrets and techniques administration is how secrets and techniques, like accessibility tokens, are stored and used by your persons and apps. It is at the bottom of our listing, but it impacts all the previous areas and deserves some thought. The AWS configuration evaluation need to consist of, and notify you of, how your consumers and solutions obtain and interact with your AWS atmosphere, which includes permissions assigned to all those end users and expert services. Nonetheless, this configuration critique will probable only be able to evaluate the configuration in your AWS account, which means in the procedure secrets and techniques management may be ignored.
Do your teams use continuous integration or ongoing deployment (CI/CD)? If they do, then it truly is probable that the pipeline used for the duration of the CI/CD process will have a amount of integration into your AWS environments. For illustration, they may have to begin new EC2 circumstances or deploy new Lambdas. How are your interior applications or providers which combine with your environment storing secrets? How are your administrators keeping tricks?
If an attacker can get obtain to these strategies, they will be able to accessibility your AWS atmosphere and be able to escalate privileges or preserve entry to the cloud natural environment as soon as they’ve been cleared off your inside network.
So, when you’re looking at a penetration examination of your AWS atmosphere, you may possibly be interested in together with the configuration of other integration units in the scope of the take a look at. Alternatively, you can split the approach across multiple resources/assessments to concentrate on personal risk regions. An AWS configuration overview will give you an knowledge of how lots of factors are connecting to your AWS environment utilizing accessibility keys and the AWS API.
Summary
Penetration testing in AWS need to be addressed cautiously, as it would be simple to spend time and income in the mistaken places. AWS is a wide ecosystem, and it really is difficult to deal with all the at any time-increasing variety of products and services in just a single position-in-time assessment, specially if you have a major AWS presence. Wise use of automation really should usually come before expensive consultancy hours, and when people are essential, they must constantly be employed most cost-effectively. You may come across that the most charge-effective way is a hybrid strategy you supply obtain to your AWS configuration, which can inform and manual a guide critique of your finish AWS estate.
The Intruder Vulnerability Scanner
Intruder is a cloud-primarily based vulnerability scanning platform utilised to check out for acknowledged vulnerabilities in your AWS natural environment to reduce your attack area.
Intruder provides a 30-working day free of charge trial of their system. Click on right here to consider nowadays.
Uncovered this posting intriguing? Stick to THN on Fb, Twitter and LinkedIn to examine much more exclusive material we publish.
Some parts of this article are sourced from:
thehackernews.com


 Police Crack Multimillion-Dollar Real Estate Fraud Gang
Police Crack Multimillion-Dollar Real Estate Fraud Gang