In what seems to be a contemporary twist in Android malware, people of Gigaset cell devices are encountering unwelcome applications that are remaining downloaded and set up as a result of a pre-put in method update app.
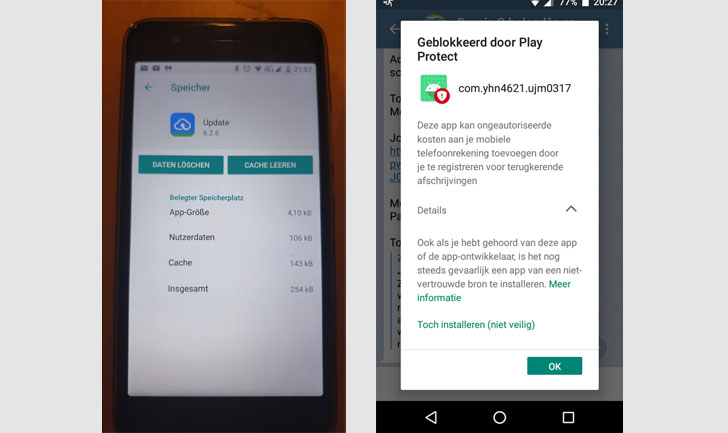
“The perpetrator putting in these malware apps is the Update application, deal title com.redstone.ota.ui, which is a pre-put in technique application,” Malwarebytes researcher Nathan Collier reported. “This application is not only the cellular device’s process updater, but also an vehicle installer acknowledged as Android/PUP.Riskware.Autoins.Redstone.”
The progress was initial noted by German creator and blogger Günter Born last week.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
When the issue seems to be generally affecting Gigaset phones, equipment from a handful of other manufacturers seem to be impacted as well. The entire listing of units that come with the pre-installed vehicle-installer consists of Gigaset GS270, Gigaset GS160, Siemens GS270, Siemens GS160, Alps P40pro, and Alps S20pro+.
According to Malwarebytes, the Update app installs 3 diverse versions of a trojan (“Trojan.Downloader.Agent.WAGD”) that’s capable of sending SMS and WhatsApp messages, redirecting consumers to destructive recreation sites, and downloading extra malware-laced applications.
“The malicious WhatsApp messages are most very likely in order to even further spread the infection to other cell units,” Collier pointed out.
Buyers have also documented suffering from a second trojan referred to as “Trojan.SMS.Agent.YHN4” on their mobile products right after landing on gaming internet websites redirected by the aforementioned WAGD trojan, which mirrors the latter’s SMS and WhatsApp messaging functionality to propagate the malware.
Not like 3rd-party applications downloaded from the Google Participate in Retailer, technique apps cannot be effortlessly eradicated from cell devices with no resorting to tools like Android Debug Bridge (ADB).
For its element, Gigaset verified the malware attack, stating that an update server employed by Gigaset units to fetch software program updates was compromised and that only gadgets that relied on that particular update server ended up afflicted. The business has considering the fact that set the issue and is expected to push an update to remove the malware from contaminated telephones, according to Born.
The advancement will come a 7 days after cybersecurity researchers uncovered a new Android malware that was identified to pilfer users’ shots, video clips, and GPS destinations by sending a fraudulent notification posing as a “Procedure Update” that is “Searching for update.”
Observed this write-up attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to browse more exclusive written content we write-up.
Some parts of this short article are sourced from:
thehackernews.com


 Experts uncover a new Banking Trojan targeting Latin American users
Experts uncover a new Banking Trojan targeting Latin American users