Cybersecurity scientists currently took the wraps off an on-going cyber fraud procedure led by hackers in Gaza, West Financial institution, and Egypt to compromise VoIP servers of far more than 1,200 companies across 60 countries around the previous 12 months.
In accordance to findings printed by Look at Issue Analysis, the threat actors — believed to be found in the Palestinian Gaza Strip — have specific Sangoma PBX, an open up-sourced consumer interface which is utilised to take care of and management Asterisk VoIP phone programs, significantly the Session Initiation Protocol (SIP) servers.
“Hacking SIP servers and attaining management will allow hackers to abuse them in many approaches,” the cybersecurity organization mentioned in its analysis. “Just one of the additional complicated and attention-grabbing ways is abusing the servers to make outgoing phone calls, which are also applied to make profits. Creating calls is a legitimate aspect, therefore it really is challenging to detect when a server has been exploited.”

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
By marketing phone numbers, call plans, and stay entry to compromised VoIP solutions from qualified companies to the optimum bidders, the operators of the marketing campaign have created hundreds of 1000’s of dollars in financial gain, along with equipping them with capabilities to eavesdrop on genuine calls.
Exploiting a Distant Admin Authentication Bypass Flaw
PBX, small for private department exchange, is a switching program that’s employed to establish and control telephone calls amongst telecommunication endpoints, this sort of as customary phone sets, destinations on the general public switched phone network (PSTN), and equipment or providers on voice in excess of Internet Protocol (VoIP) networks.
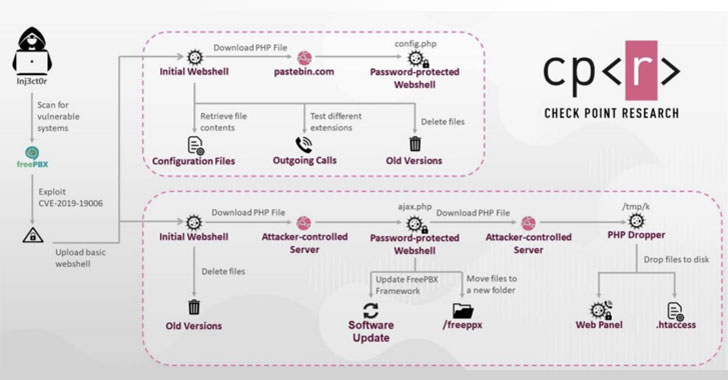
Examine Point’s research observed that the attack exploits CVE-2019-19006 (CVSS score 9.8), a critical vulnerability impacting the administrator web interface of FreePBX and PBXact, likely permitting unauthorized people to acquire admin accessibility to the process by sending specially crafted packets to the afflicted server.
The distant admin authentication bypass flaw has an effect on FreePBX versions 15..16.26 and beneath, 14..13.11 and underneath, and 13..197.13 and beneath and was patched by Sangoma in November 2019.
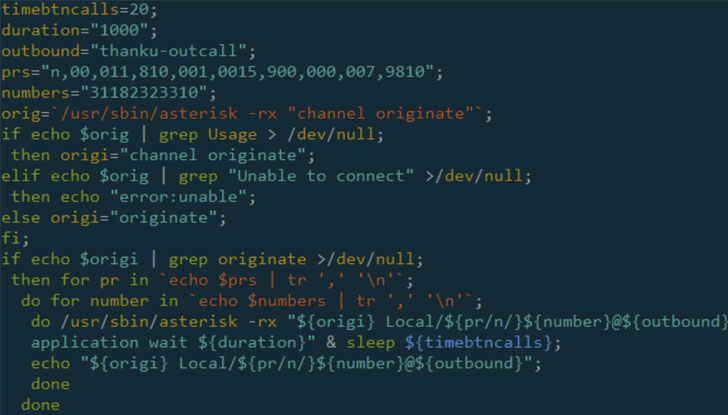
“The attack begins with SIPVicious, a well known instrument suite for auditing SIP-centered VoIP systems,” the scientists mentioned. “The attacker works by using the ‘svmapmodule’ to scan the internet for SIP systems jogging susceptible FreePBX variations. As soon as located, the attacker exploits CVE-2019-19006, gaining admin accessibility to the program.”
In 1 attack flow, it was found that an original PHP web shell was utilized to get maintain of the FreePBX system’s database and passwords for various SIP extensions, granting the attackers unrestricted obtain to the whole process and the means to make phone calls out of every extension.
In the next variation of the attack, the first web shell was utilized to down load a base64-encoded PHP file, which is then decoded to start a web panel that lets the adversary area calls employing the compromised procedure with both of those FreePBX and Elastix guidance, as effectively as operate arbitrary and challenging-coded instructions.
The campaign’s reliance on Pastebin to download password-guarded web shells has tied the attack to an uploader by the title of “INJ3CTOR3,” whose identify is linked to an old SIP Remote Code Execution vulnerability (CVE-2014-7235) in addition to a number of personal Fb groups that are utilised to share SIP server exploits.
A Scenario of Intercontinental Earnings Share Fraud
Check Level researchers posited that the hacked VoIP servers could be utilized by the attackers to make calls to Intercontinental Top quality Amount Figures (IPRN) under their handle. IPRNs are specialized quantities utilised by enterprises to offer you phone-primarily based buys and other services — like placing callers on maintain — for a greater rate.
This cost is commonly handed on to shoppers who make the calls to these quality figures, generating it a system ripe for abuse. Consequently, the extra calls the operator of an IPRN receives and the for a longer period shoppers hold out in the line to finish the transaction, the more funds it can demand telecom vendors and buyers.
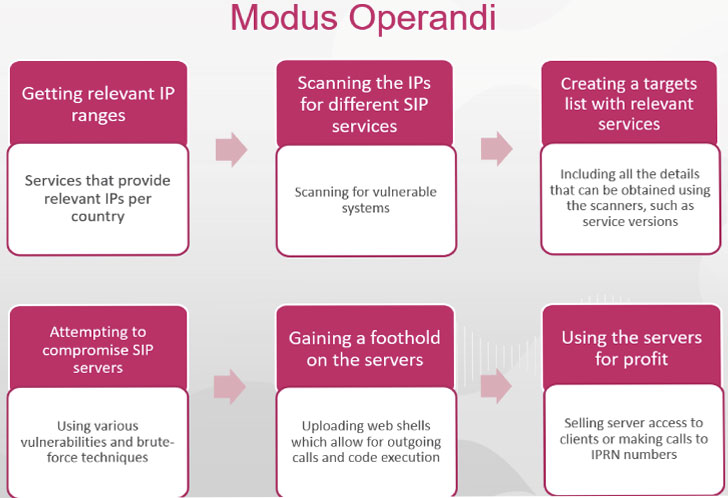
“Applying IPRN packages not only makes it possible for the hacker to make phone calls but also abuse the SIP servers to generate profits,” the researchers explained. “The more servers exploited, the additional calls to the IPRN can be built.”
This is not the to start with time switching methods have been exploited for Intercontinental Income Share Fraud (IRSF) — the observe of illegally gaining access to an operator’s network in order to inflate targeted visitors to phone quantities acquired from an IPRN provider.
Again in September, ESET researchers uncovered Linux malware dubbed “CDRThief” that targets VoIP softswitches in an endeavor to steal phone connect with metadata and carry out IRSF strategies.
“Our analysis reveals how hackers in Gaza and the West Lender are making their funds, supplied the dire socio-financial ailments in the Palestinian territories,” reported Adi Ikan, head of network cybersecurity research at Look at Position.
“Their cyber fraud procedure is a quick way to make massive sums of cash, fast. Additional broadly, we’re seeing a common phenomenon of hackers working with social media to scale the hacking and monetization of VoIP units this 12 months.”
“The attack on Asterisk servers is also abnormal in that the threat actors’ goal is to not only offer obtain to compromised techniques, but also use the systems’ infrastructure to produce profit. The thought of IPRN will allow a direct hyperlink concerning earning phone calls and making income.”
Uncovered this short article appealing? Abide by THN on Facebook, Twitter and LinkedIn to go through far more distinctive information we article.
Some pieces of this posting are sourced from:
thehackernews.com

 Gaming Giant Capcom Suffers Security Breach
Gaming Giant Capcom Suffers Security Breach