Brave has set a privacy issue in its browser that despatched queries for .onion domains to general public internet DNS resolvers somewhat than routing them through Tor nodes, therefore exposing users’ visits to dark web internet sites.
The bug was resolved in a hotfix launch (V1.20.108) created readily available yesterday.
Brave ships with a built-in element termed “Private Window with Tor” that integrates the Tor anonymity network into the browser, making it possible for customers to accessibility .onion internet websites, which are hosted on the darknet, without the need of revealing the IP handle information and facts to internet support providers (ISPs), Wi-Fi network vendors, and the internet sites by themselves. The attribute was added in June 2018.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

This is accomplished by relaying users’ requests for an onion URL through a network of volunteer-run Tor nodes. At the same time, it can be value noting that the attribute utilizes Tor just as a proxy and does not put into practice most of the privacy protections made available by Tor Browser.
But in accordance to a report 1st disclosed on Ramble, the privacy-defeating bug in the Tor manner of the browser made it probable to leak all the .onion addresses visited by a person to community DNS resolvers.
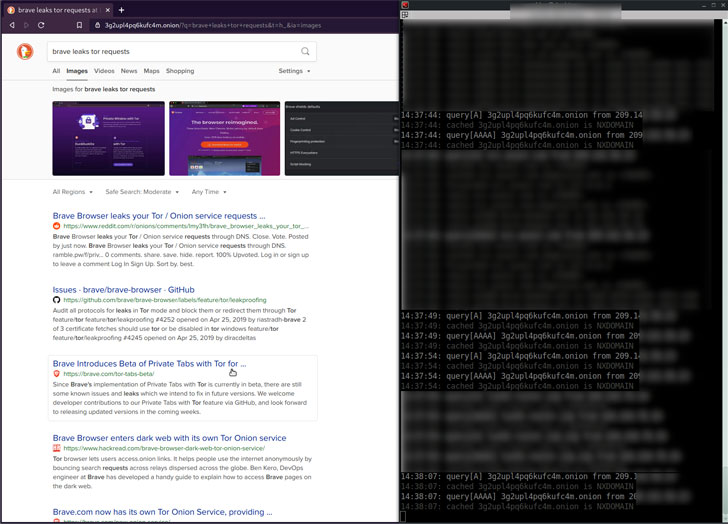
“Your ISP or DNS service provider will know that a ask for made to a certain Tor web-site was manufactured by your IP,” the put up read through.
DNS requests, by design, are unencrypted, meaning that any request to obtain .onion sites in Courageous can be tracked, thereby defeating the quite intent of the privacy attribute.
This issue stems from the browser’s CNAME advertisement-blocking element that blocks third-party tracking scripts that use CNAME DNS information to impersonate the initial-party script when it is not and avoid detection by information blockers. In accomplishing so, a web-site can cloak 3rd-party scripts utilizing sub-domains of the major area, which are then redirected quickly to a monitoring domain.
Courageous, for its component, presently had prior awareness of the issue, for it was documented on the bug bounty platform HackerOne on January 13, pursuing which the security issue was fixed in a Nightly release 15 days back.
It appears that the patch was originally scheduled to roll out in Brave Browser 1.21.x, but in the wake of community disclosure, the corporation explained it’s pushing it to the steady version of the browser released yesterday.
Brave browser buyers can head to Menu on the top suitable > About Courageous to obtain and put in the newest update.
Located this short article intriguing? Observe THN on Facebook, Twitter and LinkedIn to read much more exclusive content material we publish.
Some pieces of this short article are sourced from:
thehackernews.com


 ‘If you wait for government, you’re going to be waiting a long time’: A look at Biden’s cyber funding
‘If you wait for government, you’re going to be waiting a long time’: A look at Biden’s cyber funding