Cybersecurity scientists on Monday disclosed a established of nine vulnerabilities recognized as “PwnedPiper” that remaining a widely-utilised pneumatic tube program (PTS) susceptible to critical attacks, including a probability of total takeover.
The security weaknesses, disclosed by American cybersecurity firm Armis, impact the Translogic PTS procedure by Swisslog Healthcare, which is installed in about 80% of all key hospitals in North America and in no fewer than 3,000 hospitals globally.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“These vulnerabilities can empower an unauthenticated attacker to acquire about Translogic PTS stations and essentially attain finish control in excess of the PTS network of a target clinic,” Armis researchers Ben Seri and Barak Hadad stated. “This form of regulate could enable complex and worrisome ransomware attacks, as nicely as allow attackers to leak delicate medical center info.”
Pneumatic tube programs are internal logistics and transportation solutions that are applied to transportation blood samples in healthcare facility settings to diagnostic laboratories securely.
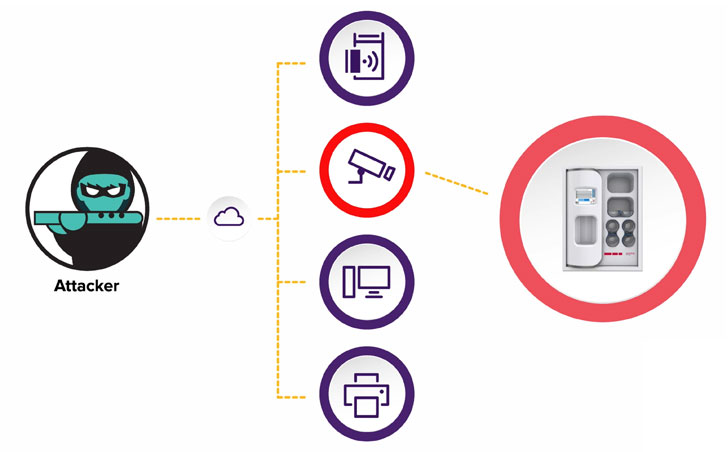
Effective exploitation of the issues, hence, could outcome in leakage of delicate information, allow an adversary to manipulate facts, and even compromise the PTS network to carry out a man-in-the-middle (MitM) attack and deploy ransomware, thereby proficiently halting the functions of the medical center.
The information about the nine PwndPiper vulnerabilities are mentioned as follows –
- CVE-2021-37161 – Underflow in udpRXThread
- CVE-2021-37162 – Overflow in sccProcessMsg
- CVE-2021-37163 – Two hardcoded passwords available by the Telnet server
- CVE-2021-37164 – Off-by-a few stack overflow in tcpTxThread
- CVE-2021-37165 – Overflow in hmiProcessMsg
- CVE-2021-37166 – GUI socket Denial Of Company
- CVE-2021-37167 – Consumer script operate by root can be utilised for PE
- CVE-2021-37160 – Unauthenticated, unencrypted, unsigned firmware update
In a nutshell, the flaws — which problem privilege escalation, memory corruption, and denial-of-support — could be abused to gain root accessibility, accomplish distant-code-execution or denial-of-company, and worse, allow an attacker to keep persistence on compromised PTS stations by means of an insecure firmware up grade method, main to unauthenticated distant-code-execution. It is also value noting that a patch for CVE-2021-37160 is anticipated to be transported at a future day.

“The possible for pneumatic tube stations (in which the firmware is deployed) to be compromised is dependent on a terrible actor who has access to the facility’s information technology network and who could bring about additional harm by leveraging these exploits,” Swisslog Health care mentioned in an impartial advisory released nowadays.
Translogic PTS program shoppers are highly advisable to update to the newest firmware (Nexus Regulate Panel version 7.2.5.7) to mitigate any opportunity risk that could occur out of actual-entire world exploitation of the shortcomings.
“This investigation sheds mild on techniques that are concealed in basic sight but are nevertheless a essential constructing block to fashionable-day health care,” Seri and Hadad stated. “Knowledge that individual care depends not only on healthcare devices, but also on the operational infrastructure of a hospital is an important milestone to securing healthcare environments.”
Located this report fascinating? Comply with THN on Facebook, Twitter and LinkedIn to browse more exceptional content we article.
Some areas of this post are sourced from:
thehackernews.com


 New APT Hacking Group Targets Microsoft IIS Servers with ASP.NET Exploits
New APT Hacking Group Targets Microsoft IIS Servers with ASP.NET Exploits