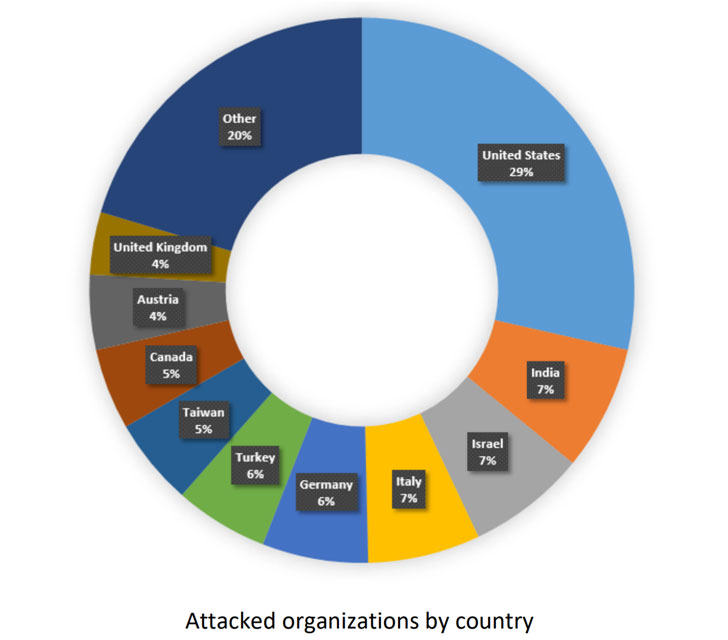
A infamous banking trojan aimed at stealing financial institution account qualifications and other fiscal facts has now come back again with new tricks up its sleeve to goal authorities, army, and production sectors in the US and Europe, in accordance to new investigate.
In an analysis released by Test Point Investigate today, the most recent wave of Qbot action seems to have dovetailed with the return of Emotet — one more email-primarily based malware at the rear of numerous botnet-driven spam campaigns and ransomware assaults — previous month, with the new sample able of covertly accumulating all email threads from a victim’s Outlook client and applying them for later on malspam strategies.
“These times Qbot is much much more perilous than it was formerly — it has an lively malspam marketing campaign which infects organizations, and it manages to use a ‘third-party’ infection infrastructure like Emotet’s to spread the risk even even further,” the cybersecurity business explained.
Working with Hijacked Email Threads as Lures
Initial documented in 2008, Qbot (aka QuakBot, QakBot, or Pinkslipbot) has advanced about the many years from an data stealer to a “Swiss Army knife” adept in delivering other sorts of malware, which includes Prolock ransomware, and even remotely hook up to a target’s Windows technique to have out banking transactions from the victim’s IP tackle.
Attackers generally infect victims working with phishing approaches to lure victims to web sites that use exploits to inject Qbot via a dropper.
A malspam offensive observed by F5 Labs in June located the malware to be equipped with detection and analysis-evasion strategies with the objective of evading forensic evaluation. Then past 7 days, Morphisec unpacked a Qbot sample that arrived with two new strategies designed to bypass Written content Disarm and Reconstruction (CDR) and Endpoint Detection and Response (EDR) methods.
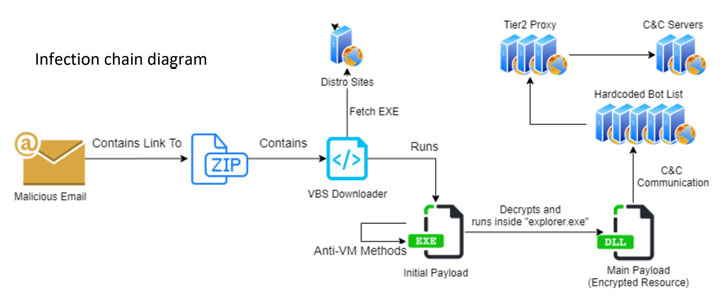
The an infection chain thorough by Look at Level follows a related sample.
The 1st stage begins with a specially crafted phishing email made up of an hooked up ZIP file or a url to a ZIP file that incorporates a destructive Visual Primary Script (VBS), which then proceeds to down load additional payloads responsible for keeping a suitable communication channel with an attacker-managed server and executing the commands gained.
Notably, the phishing e-mails sent to the qualified companies, which consider the type of COVID-19 lures, tax payment reminders, and task recruitments, not only consists of the malicious material but is also inserted with archived email threads in between the two get-togethers to lend an air of trustworthiness.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
To realize this, the discussions are collected beforehand applying an email collector module that extracts all email threads from the victim’s Outlook customer and uploads them to a hardcoded remote server.
Aside from packing components for grabbing passwords, browser cookies, and injecting JavaScript code on banking web-sites, the Qbot operators unveiled as quite a few as 15 versions of the malware considering the fact that the start of the yr, with the previous recognized edition released on August 7.
What’s more, Qbot arrives with an hVNC Plugin that will make it attainable to control the victim machine by way of a distant VNC relationship.
“An external operator can execute financial institution transactions without having the user’s awareness, even whilst he is logged into his personal computer,” Verify Position pointed out. “The module shares a higher percentage of code with similar modules like TrickBot’s hVNC.”
From an Contaminated Device to a Manage Server
That’s not all. Qbot is also equipped with a different mechanism to recruit the compromised devices into a botnet by creating use of a proxy module that permits the infected device to be applied as a handle server.
With Qbot hijacking authentic email threads to distribute the malware, it can be critical that users check their emails for phishing assaults, even in circumstances they appear to occur from a reliable supply.
“Our study exhibits how even more mature sorts of malware can be updated with new attributes to make them a hazardous and persistent menace,” Check Issue Research’s Yaniv Balmas reported. “The threat actors powering Qbot are investing intensely in its advancement to allow info theft on a enormous scale from businesses and men and women.”
“We have observed active malspam campaigns distributing Qbot specifically, as perfectly as the use of third-party infection infrastructures like Emotet’s to unfold the menace even additional,” Balmas added.
Located this post appealing? Stick to THN on Facebook, Twitter and LinkedIn to read through a lot more exclusive information we write-up.


 Dracula Network Pushes Out Pro-China Twitter Spam
Dracula Network Pushes Out Pro-China Twitter Spam