An “intense” financially enthusiastic menace actor has been discovered as linked to a string of RYUK ransomware attacks considering that Oct 2018, although maintaining near partnerships with TrickBot-affiliated risk actors and employing a publicly offered arsenal of applications these as Cobalt Strike Beacon payloads to interact with target networks.
Cybersecurity agency Mandiant attributed the intrusions to a Russian-speaking hacker group codenamed FIN12, and beforehand tracked as UNC1878, with a disproportionate aim on health care companies with extra than $300 million in revenue, amid other individuals, like education, economic, manufacturing, and technology sectors, located in North The us, Europe, and the Asia Pacific.
“FIN12 depends on partners to acquire initial access to target environments,” Mandiant scientists explained. “Notably, instead of conducting multifaceted extortion, a tactic widely adopted by other ransomware threat actors, FIN12 seems to prioritize speed and better revenue victims.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

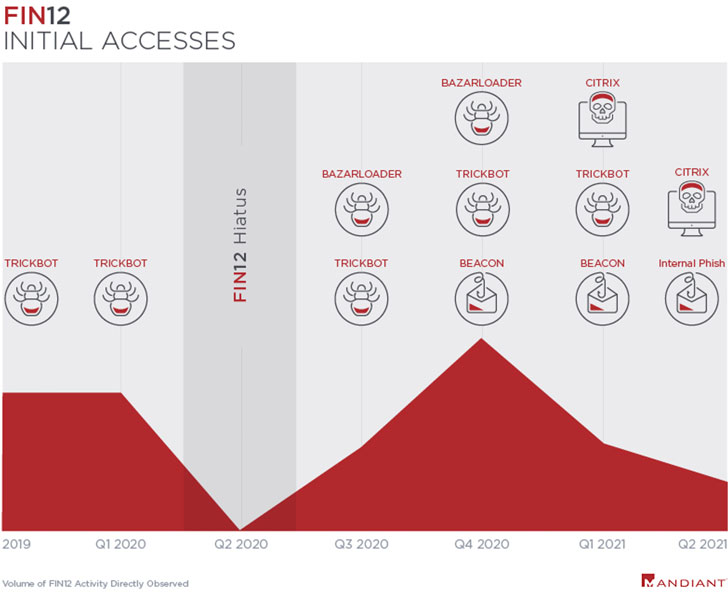
The use of original accessibility brokers to aid ransomware deployments isn’t new. In June 2021, results from enterprise security organization Proofpoint disclosed that ransomware actors are ever more shifting from applying email messages as an intrusion route to getting entry from cybercriminal enterprises that have now infiltrated important entities, with Ryuk infections generally leveraging accesses obtained by way of malware family members like TrickBot and BazaLoader.
FIN12’s targeting of the healthcare sector suggests that its original access brokers “solid a wider net and allow for FIN12 actors to opt for from a list of victims just after accesses are now obtained.”
Mandiant also pointed out that it noticed, in May possibly 2021, risk actors getting a foothold in the network by means of phishing email campaigns distributed internally from compromised consumer accounts, just before top to the deployment of Cobalt Strike Beacon and WEIRDLOOP payloads. Attacks mounted involving mid-February and mid-April of 2021 are claimed to also have taken benefit of distant logins by obtaining maintain of qualifications to victims’ Citrix environments.
While FIN12’s practices in late 2019 involved using TrickBot as a means to manage a foothold in the network and have out latter-phase duties, such as reconnaissance, offering malware droppers, and deploying the ransomware, the team has since persistently banked on Cobalt Strike Beacon payloads for doing article-exploitation routines.

FIN12 also distinguishes by itself from other intrusion risk actors in that it doesn’t engage in data theft extortion — a tactic that’s utilized to leak exfiltrated details when victims refuse to shell out up — which Mandiant says stems from the danger actor’s desire to transfer speedily and strike targets that are keen to settle with small negotiation.
“The common time to ransom (TTR) throughout our FIN12 engagements involving info theft was 12.4 times (12 times, 9 several hours, 44 minutes) in contrast to 2.48 times (2 times, 11 hrs, 37 minutes) where details theft was not observed,” the scientists explained. “FIN12’s obvious achievement with out the require to integrate further extortion solutions very likely reinforces this idea.”
“[FIN12 is the] first FIN actor that we are advertising and marketing who specializes in a precise stage of the attack lifecycle — ransomware deployment — although relying on other menace actors for attaining preliminary accessibility to victims,” Mandiant observed. “This specialization reflects the present-day ransomware ecosystem, which is comprised of a variety of loosely affiliated actors partnering jointly, but not exclusively with one yet another.”
Found this write-up attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to study far more distinctive information we publish.
Some parts of this write-up are sourced from:
thehackernews.com


 BrewDog app flaw exposed data on 200,000 shareholders and customers, researchers claim
BrewDog app flaw exposed data on 200,000 shareholders and customers, researchers claim