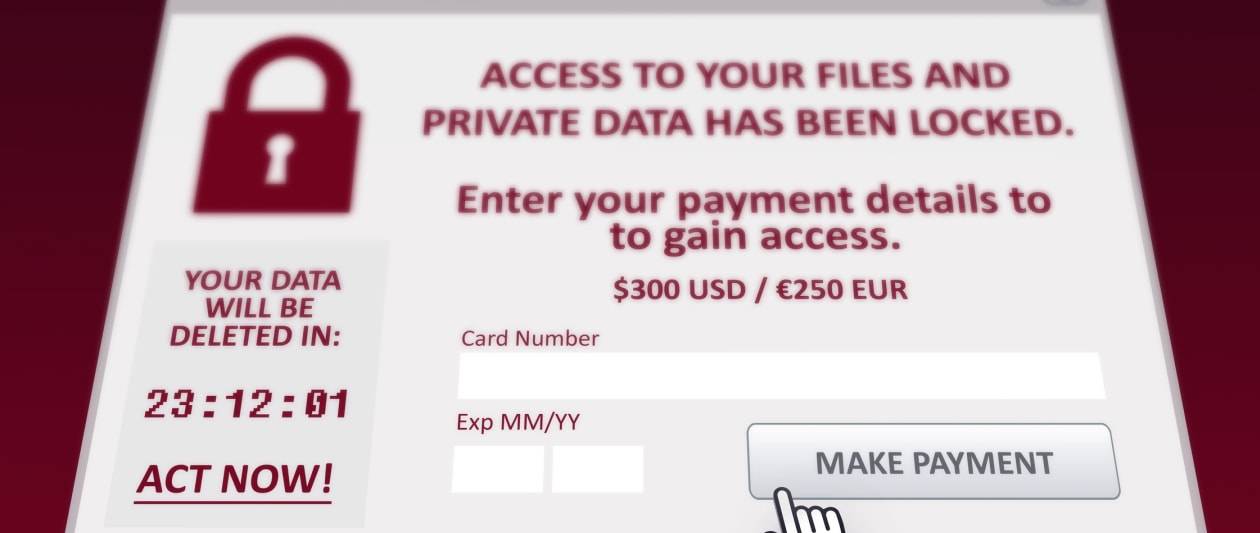
Modest organizations are becoming warned to get ready for a prospective surge in ransomware attacks in 2022 as cyber criminals turn to strategies that are considerably less very likely to attract coordinated action from legislation enforcement.
Cyber criminals are stated to be adapting to enhanced force from law enforcement businesses that have released a quantity of profitable operations to dismantle felony networks, in accordance to an evaluation by menace intelligence firm Analyst1, revealed nowadays.
“As an alternative of likely following the superior-profile attacks, given that the activity brings undesired attention from the federal governing administration, they will probable concentrate on lesser providers that will allow them to remain beneath the radar,” explained Chris Fiormonti, previous intelligence community danger analyst and researcher with the firm.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
In a critique of big-ticket ransomware actions for the calendar year, Fiormonti noted greater scrutiny and efforts by western law enforcement to quash the extra egregious teams.
This features warnings from CISA and the FBI, which includes very last month’s advisories that ransomware attacks were being possible to maximize for the duration of the holiday getaway season.
The US Treasury, which now treats ransomware with the very same severity as terrorism, offered a $10m reward for data primary to the arrest of the BlackMatter team. Federal organizations also issued a joint inform that it experienced specific critical infrastructure teams.
Law enforcement has scored some significant wins, Fiormonti additional, pointing to the disappearance of the BlackMatter team in November, and the disappearance of the REvil group in July, and once again in Oct, following a multi-point out energy. Europol also captured many REvil users past month.
Citing a paper by the firm’s main security strategist, Fiormonti mentioned quite a few immediate backlinks in between ransomware groups and the Russian authorities, together with the Enterprise Club, Evilcorp, Silverfish, and Wizard Spider groups. Though these teams largely attack for financial gain, a adjust in targets from preceding several years matches Russian governing administration targets, he reported. A latest New York Occasions report reported that some teams function out of Moscow’s Federation Tower East, a prestigious company handle, with obvious impunity.
Even though the attacks might improve route, there is no indicator that they will cease, Fiormonti extra.
“Ransomware attacks will go on as extensive as they are successful or until the core team of folks that get protected haven in Russia are taken down or disrupted,” he stated.
Some pieces of this short article are sourced from:
www.itpro.co.uk

 Facebook to Pay Hackers for Reporting Data Scraping Bugs and Scraped Datasets
Facebook to Pay Hackers for Reporting Data Scraping Bugs and Scraped Datasets