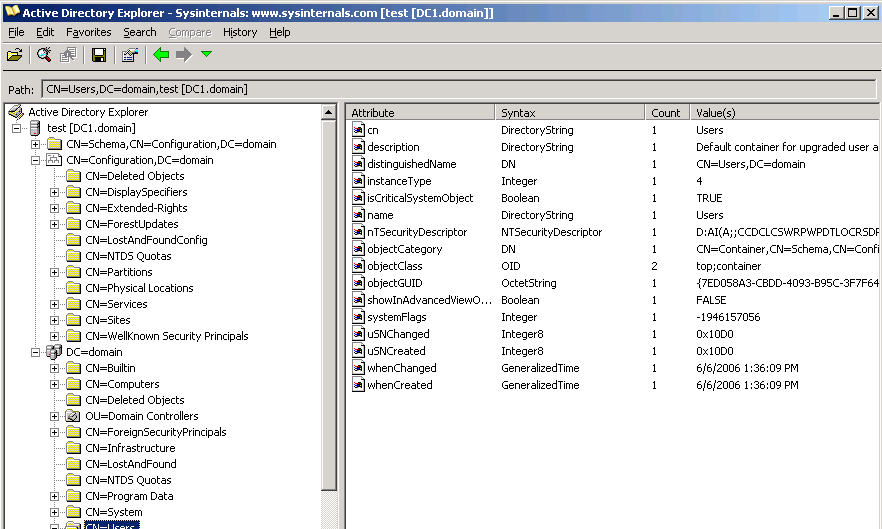
There has been an uptick in subtle ransomware intrusions where by the Active Listing is compromised, according to a new panel discussion. (““Active Directory” by arrayexception is accredited under CC BY-SA 2.)
The cybersecurity group paid out close notice to ransomware actors’ escalation of small business strategies in the previous calendar year, which includes double extortion, forming cartels and calling personal victims specifically.
But a single ought to not overlook some of the more recent resources and technical methods that these adversaries a short while ago included to their repertoires in purchase to hinder and complicate forensic investigations. A panel of IT experts discussed some of these hottest problems in a ransomware session held last 7 days at the 2021 Incident Reaction Forum Masterclass.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
For instance, Aravind Swaminathan, companion at the law agency Orrick, mentioned an uptick in subtle ransomware intrusions in which the Energetic Listing is compromised, which “makes the investigations not only a lot more challenging but also just take a whole lot lengthier time period of time, simply because they have oftentimes been spending… extensive durations in the environment looking at a great deal of diverse many devices.”
And in cases where by the Active Listing and area controller are established up on a virtual equipment, the attackers are holistically encrypting the VM atmosphere, pointed out Bret Padres, team vice president with Crypsis, a Palo Alto company.
This offers the adversaries an higher hand, he added, simply because it further more slows down forensic analysis, which would usually be transpiring even as negotiations with the actors are having area. “This stalls us a minimal bit for the reason that we have to wait around ’til we get the decryption crucial to be in a position to decide what forensic evidence is on that area controller,” he mentioned.
A further problem is malicious’ actors adoption of Rclone, a legitimate, open up-resource, command line-centered file synching software that enterprises generally use to back again up assets to the cloud. “Whereas prior to we noticed a ton of FileZilla, Megaupload and all those varieties of points, Rclone [now] is being employed. And it does make forensics a small bit additional hard,” including looking for and determining indicators of compromise, reported Padres.
 Clockwise from major, still left: John Reed Stark, president, John Reed Stark Consulting, LLC Kari Rollins, spouse, Sheppard Mullin Bret Padres, group VP, Crypsis, a Palo Alto Networks Firm J.J. Jones, senior corporate counsel, Microsoft Aravind Swaminathan, lover, Orrick and Scott Lindlaw, running director at Sard Verbinnen & Co.
Clockwise from major, still left: John Reed Stark, president, John Reed Stark Consulting, LLC Kari Rollins, spouse, Sheppard Mullin Bret Padres, group VP, Crypsis, a Palo Alto Networks Firm J.J. Jones, senior corporate counsel, Microsoft Aravind Swaminathan, lover, Orrick and Scott Lindlaw, running director at Sard Verbinnen & Co.
Specialists at SpearTip past year reported that Rclone was emerging as a new tool for information exfiltration in ransomware attacks. SentinelOne reported that presumed Maze ransomware successor Egregor leverages Rclone as nicely.
The use of Rclone, claimed Swaminathan, would make “understanding what knowledge was truly exfiltrated… even trickier, mostly simply because if you glance at the way Rclone will work and the threading that it that it applies, it’s genuinely tricky to map what knowledge they in fact received accessibility to or acquired… And so that actually has been a big stumbling block in our investigation[s].”
With that said, Padres famous that negotiations with the hackers will typically expose to you what they stole. (It’s just up to the corporation what to feel.) “If you request them, ‘What details did you consider?’ they are sharing listing listings or in some cases they are even earning that info readily available to the victim, to be in a position to say, ‘Okay, here’s a copy of your data you can log in and seem at it if you want,’” Padres claimed.
Kari Rollins, companion at Sheppard Mullin, also mentioned that attackers have been aggregating facts from several resources, making it difficult for investigators to pinpoint specifically which methods, and how many details sources, the perpetrators have been in a position to compromise and obtain. “I think that complicates the elements, and the risk and the choice-building when you have to evaluate whether or not you have an obligation to notify,” she stated.
Some components of this short article are sourced from:
www.scmagazine.com

 1.3M Clubhouse Users’ Data Dumped in Hacker Forum for Free
1.3M Clubhouse Users’ Data Dumped in Hacker Forum for Free