A company cyber-espionage hacker team has resurfaced right after a seven-thirty day period hiatus with new intrusions targeting four firms this yr, which include a single of the largest wholesale stores in Russia, while at the same time creating tactical advancements to its toolset in an endeavor to thwart investigation.
“In each individual attack, the menace actor demonstrates intensive red teaming skills and the capacity to bypass traditional antivirus detection using their have custom made malware,” Team-IB’s Ivan Pisarev claimed.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Active given that at minimum November 2018, the Russian-talking RedCurl hacking group has been connected to 30 attacks to date with the intention of company cyber espionage and doc theft aimed at 14 companies spanning design, finance, consulting, retail, insurance coverage, and legal sectors and positioned in the U.K., Germany, Canada, Norway, Russia, and Ukraine.
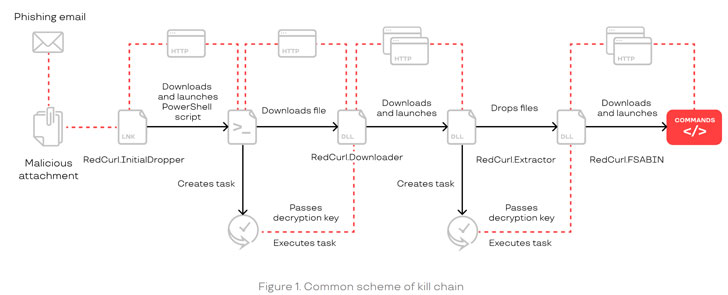
The risk actor utilizes an array of founded hacking equipment to infiltrate its targets and steal internal company documentation, such as employees documents, court and legal files, and enterprise email heritage, with the collective paying wherever from two to 6 months involving original an infection to the time information will get truly stolen.
RedCurl’s modus operandi marks a departure from other adversaries, not the very least due to the fact it doesn’t deploy backdoors nor depend on submit-exploitation tools like CobaltStrike and Meterpreter, both equally of which are witnessed as common solutions to remotely handle compromised devices. What is actually more, even with protecting entrenched obtain, the group hasn’t been noticed conducting attacks that are motivated by economical attain and involve encrypting target infrastructure, or demanding ransoms for stolen info.

Rather, the emphasis seems to be to obtain important details as covertly as possible employing a mix of self-produced and publicly out there programs to gain first accessibility utilizing social engineering implies, accomplish reconnaissance, realize persistence, go laterally, and exfiltrate sensitive documentation.
“Espionage in cyberspace is a hallmark of condition-sponsored sophisticated persistent threats,” the researchers said. “In most circumstances, these attacks concentrate on other states or state-owned companies. Corporate cyber espionage is nevertheless a comparatively exceptional and, in several means, one of a kind occurrence. Nevertheless, it is doable that the group’s success could direct to a new development in cybercrime.”
Found this posting fascinating? Stick to THN on Facebook, Twitter and LinkedIn to read far more exceptional information we publish.
Some components of this short article are sourced from:
thehackernews.com


 North Korean Hackers Found Behind a Range of Credential Theft Campaigns
North Korean Hackers Found Behind a Range of Credential Theft Campaigns