Enterprise apps employed to are living securely in facts centers and business office employees connected to internal networks working with corporation-managed laptops or desktops. And info was encircled by a walled perimeter to preserve every thing harmless.
All that altered in the previous 18 months. Businesses and personnel experienced to adapt quickly to cloud technology and distant work. The cloud gave businesses the agility to respond faster to transform and the scale to accommodate rapid progress. Distant function boosted productiveness by permitting employees access cloud facts from anywhere on any system.
This is not business enterprise as regular. The knowledge middle and the perimeter security are no for a longer time the centre of the universe. Now distant personnel, individual cellular units, purposes, and data are in the center.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Whilst staff members, apps, and details have still left the developing, IT security teams even now shoulder the obligation for preserving confidential details and ensuring compliance with rigorous privacy restrictions. The risk of not undertaking so can be expensive.
Sign-up for this forthcoming webinar to discover how to reduce risk with built-in endpoint-to-cloud security.
Details security and entry turned upside down
It truly is not possible to see risk when you will not know what you happen to be up in opposition to. Workers now obtain information in your cloud from everywhere utilizing individual units and community Wi-Fi networks you can’t see or handle. What ever visibility you had is long gone. Left unresolved, minimal – if just about anything – is beneath your manage.
Presently, security from endpoints to the cloud consists of several standalone applications that solve distinct problems. But beware: Occasionally, juggling dozens of security instruments –each unaware that the other exists – boosts the risk of publicity.
Some organizations count on digital personal networks (VPNs for distant workforce accessibility. Though they link staff members to cloud programs and knowledge from wherever, VPNs can presume every consumer and machine is reliable (they are not). So, use caution with VPNs. They can leave your infrastructure and every thing linked to it particularly susceptible.
Mired in the momentum of mediocrity, the classic security solution only features a portion of what is wanted to ensure endpoint-to-cloud security. It does not give you visibility or perception into the security posture of your users and endpoints or cloud programs. And it won’t be able to enforce zero trust, a staple of modern-day security.
Limit company risk
With data likely the place it really is needed, corporations can lower risk by regaining the exact same visibility, insights, and access controls they experienced with a perimeter. To do so, you will need a cloud-shipped resolution that presents strong details and privacy protections from endpoints to the cloud.
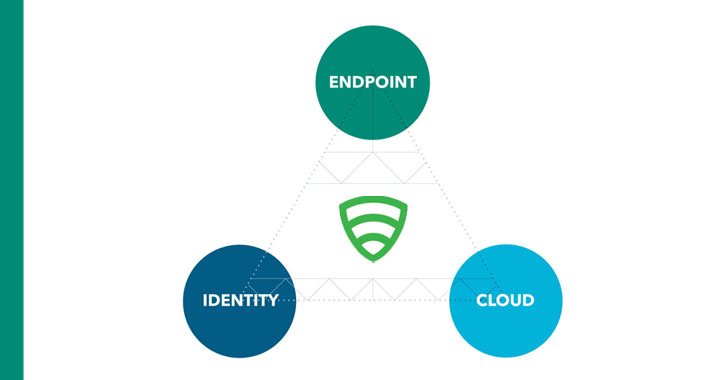
Lookout suggests considering these 3 things to lessen risk:
Data defense from endpoint to cloud
To realize endpoint-to-cloud visibility, insights, and access regulate, organizations involve perimeter-like security abilities delivered from the cloud. In 2019, Gartner released the Secure Access Services Edge (SASE), a framework that addresses these troubles and calls for rolling several security alternatives into a single unified architecture.
Given that then, throngs of sellers have integrated a variety of security resources into their SASE products. Some give cloud security but no endpoint security or ongoing risk evaluation. Some others have standard access controls but really don’t analyze user behaviors, detect malware on the fly or determine compliance gaps. And lots of do not incorporate advanced knowledge protections that encrypt confidential facts, emails, or documents and implement rigid details-sharing rules.
Every single vendor’s interpretation of SASE should be thoroughly vetted to make certain that they combine and adequately handle just about every critical factor of how your firm now operates with remote or hybrid do the job completely in position. This modern day security strategy, with SASE and Zero Rely on as cornerstones, will secure knowledge from endpoints to the cloud by supplying all-important visibility into gadgets, end users, networks, accessibility privileges, and cloud apps.
Sign up for this forthcoming webinar to find out how Lookout delivers complete endpoint-to-cloud security from just one unified platform.
Found this report appealing? Follow THN on Facebook, Twitter and LinkedIn to browse additional unique content material we article.
Some areas of this short article are sourced from:
thehackernews.com

 One-Click Exploit Could Have Let Attackers Hijack Any Atlassian Account
One-Click Exploit Could Have Let Attackers Hijack Any Atlassian Account