Chinese condition-sponsored cyberattacks pose a increasing risk to US national security, in accordance to a report from consultancy company Booz Allen Hamilton introduced on Oct 12, 2022.
The report, Same Cloak, Far more Dagger: Decoding How the People’s Republic of China (PRC) Utilizes Cyber Attacks, is addressed to CISOs of American businesses and their allies as nicely as menace analysts. It offers a complete analysis of far more than 13 circumstance research of Chinese-sponsored cyberattacks above the past 10 years to comprehend “the disorders that ignite PRC cyber offensives,” which will let companies to “better anticipate when, the place, and how these attacks may possibly occur” and “ensure they are completely ready to protect versus them.”
The situation scientific studies are divided into two groups, each and every sub-divided into two themes:

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
- Threats to domestic passions: ‘Foreign Info Threats’ and ‘The Hong Kong Democracy Movement’
- Threats to international interests: ‘Competing South China Sea Claims’ and ‘Indo-Pacific Competition’
“[Their findings] clearly show that China is developing and deploying cyberattack abilities to progress its countrywide ‘core interests.’ These cyberattacks enhance China’s better known, ever more assertive, and diverse attempts to advance its interests online via lawful, financial, cultural, political, and technological usually means.”
However, Booz Allen additional that the report was solely primarily based on open-supply analysis. “The accurate evaluate of China’s cyberattack capabilities […] most likely simply cannot be absolutely discerned in open up resources. It is attainable China has selected to not deploy its entire abilities or it has carried out so without having general public attribution,” reads the report.
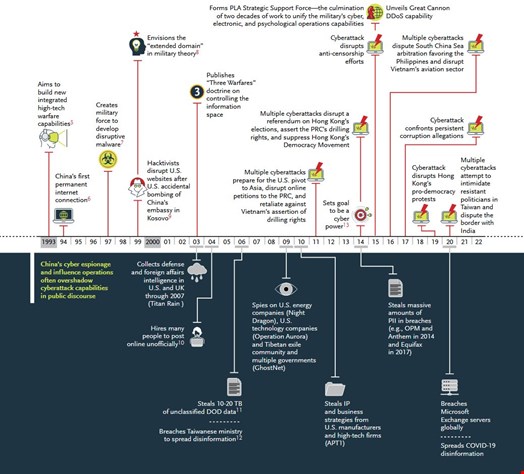
On top of the situation reports, the report provides an overview of Chinese security and intelligence agencies, an evaluation of their motives, a timeline of Chinese cyber action due to the fact 1993, a catalog of threat actors and their popular practices, tactics and strategies (TTPs) as effectively as tips for CISOs and risk analysts.
Some components of this post are sourced from:
www.infosecurity-journal.com


 Mirai Botnet Hits Wynncraft Minecraft Server with 2.5 Tbps DDoS Attack
Mirai Botnet Hits Wynncraft Minecraft Server with 2.5 Tbps DDoS Attack