Security incidents happen. It truly is not a make any difference of ‘if’ but of ‘when.’ There are security products and solutions and processes that were being implemented to improve the IR process, so from the ‘security-professional’ angle, points are taken care of.
Nonetheless, a lot of security execs who are accomplishing an fantastic task in handling incidents come across effectively speaking the ongoing process with their administration a significantly far more complicated endeavor.
It truly is a little surprise — managements are commonly not security savvy and don’t really treatment about the bits and bytes in which the security pro masters. Cynet addresses this gap with the IR Reporting for Administration PPT template, furnishing CISOs and CIOs with a obvious and intuitive software to report the two the ongoing IR course of action and its conclusion.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The IR for Administration template permits CISOs and CIOs to communicate with the two important details that management cares about—assurance that the incident is less than regulate and a crystal clear comprehending of implications and root induce.
Manage is a crucial element of IR procedures, in the feeling that at any provided instant, there is complete transparency of what is dealt with, what is known and desires to be remediated, and what further investigation is needed to unveil sections of the attack that are still mysterious.
Management won’t consider in conditions of trojans, exploits, and lateral movement, but somewhat it thinks in terms of company productivity — downtime, gentleman-several hours, loss of sensitive data.
Mapping a large-amount description of the attack route to resulted damage is paramount to get the management’s knowing and involvement, primarily if the IR approach entails further spending.
The Template follows the SANSNIST IR framework and includes the next phases:
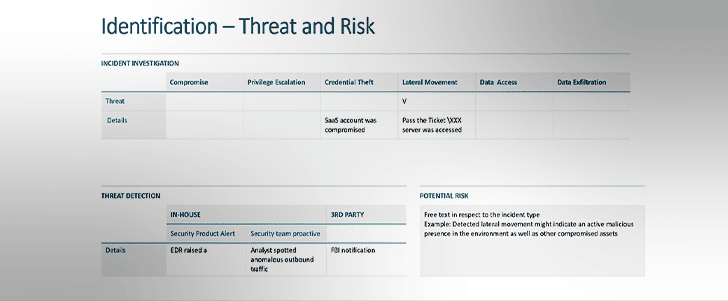
Identification
Attacker existence is detected beyond question. Was the detection manufactured in house or by a 3rd party, how experienced the attack is (in terms of its progress together the eliminate chain), what is the approximated risk, and will the pursuing measures be taken with inner assets or is there a need to interact a company service provider?
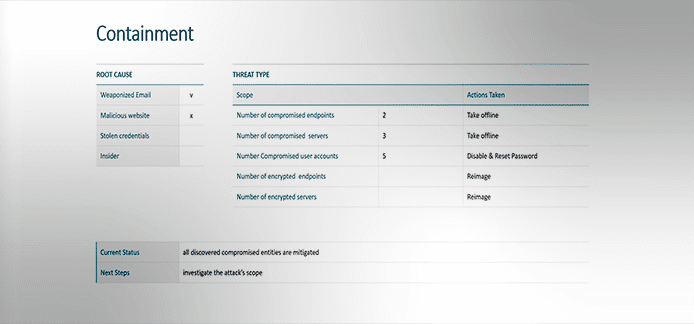
Containment
First assist to quit the quick bleeding just before any even further investigation, the attack root cause, the range of entities taken offline (endpoints, servers, person accounts), existing standing, and onward methods.
Eradication
Whole cleanse up of all malicious infrastructure and activities, a total report on the attack’s route and assumed aims, overall organization impression (person-several hours, dropped information, regulatory implications and other people for each the various context)
Restoration
Recovery charge in phrases of endpoints, servers, programs, cloud workloads, and info.
Lessons Acquired
What were the attack’s enablers (deficiency of ample security technology in area, insecure workforce techniques, and many others.) and how they can be mended, and reflection on the past stages throughout the IR system timeline looking for what to preserve and what to make improvements to.
The natural way, there is no 1-size-suits-all in a security incident. For illustration, there might be cases in which the identification and containment will take position almost instantly together, even though in other events, the containment could just take more time, necessitating numerous shows on its interim status. Which is why the template is modular and can be conveniently adjustable to any variant.
Interaction to management is not a nice-to-have but a critical part of the IR procedure alone. The definitive IR Reporting to Administration PPT template enables all who perform really hard to conduct expert and economical IR procedures in their organizations to make their endeavours and results crystal clear to their administration.
Obtain the Definitive IR Reporting to Management PPT template in this article.
Identified this posting exciting? Follow THN on Fb, Twitter and LinkedIn to read through more exclusive articles we submit.
Some parts of this post are sourced from:
thehackernews.com

 What’s next for the education sector?
What’s next for the education sector?