A newly disclosed vulnerability affecting Intel processors could be abused by an adversary to gain access to sensitive data saved inside enclaves and even operate arbitrary code on vulnerable units.
The vulnerability (CVE-2021-0186, CVSS score: 8.2) was found by a group of lecturers from ETH Zurich, the Nationwide College of Singapore, and the Chinese Countrywide College of Defense Technology in early May perhaps 2021, who utilized it to phase a private info disclosure attack known as “SmashEx” that can corrupt personal knowledge housed in the enclave and crack its integrity.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Introduced with Intel’s Skylake processors, SGX (shorter for Software program Guard eXtensions) lets developers to operate selected application modules in a completely isolated safe compartment of memory, known as an enclave or a Reliable Execution Atmosphere (TEE), which is built to be secured from processes running at bigger privilege amounts like the working system. SGX ensures that knowledge is protected even if a computer’s running method has been tampered with or is less than attack.
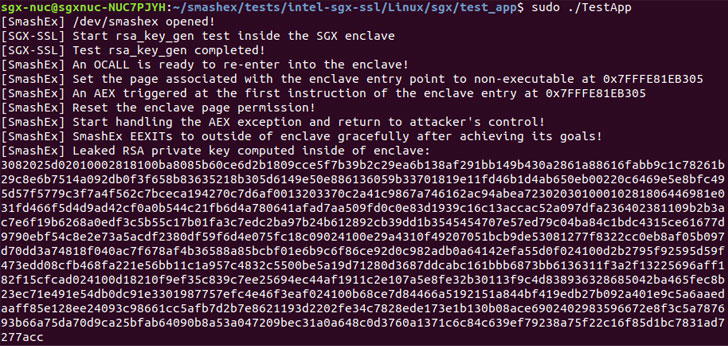
“For usual functioning, the SGX design and style makes it possible for the OS to interrupt the enclave execution by configurable hardware exceptions at any stage,” the scientists outlined. “This function allows enclave runtimes (e.g., Intel SGX SDK and Microsoft Open up Enclave) to aid in-enclave exception or signal dealing with, but it also opens up enclaves to re-entrancy bugs. SmashEx is an attack which exploits enclave SDKs which do not diligently manage re-entrancy in their excellent handling safely and securely.”
It is really really worth noting that an enclave may perhaps also have Exterior Calls, or OCALLS, which permit enclave functions to simply call out to the untrusted software and then return to the enclave. But when the enclave is also dealing with in-enclave exceptions (e.g., timer interrupt or division-by-zero), the vulnerability offers a brief window for a nearby attacker to hijack the control flow of execution by injecting an asynchronous exception straight away just after the enclave is entered.
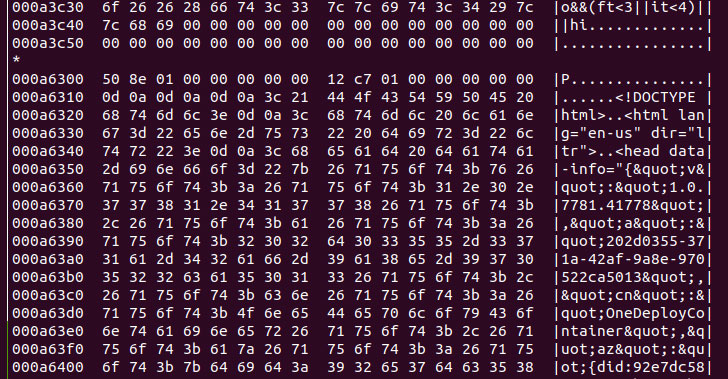
Armed with this functionality, the adversary can then corrupt the in-enclave memory to leak sensitive info these types of as RSA private keys or execute malicious code.
Since SmashEx impacts runtimes that assistance in-enclave exception dealing with, the scientists pointed out that “these OCALL return move and the exception handling move should be written with treatment to make certain that they interleave properly,” and that “when the OCALL return movement is interrupted, the enclave should really be in a constant state for the exception handling move to progress properly, and when the exception handling move completes, the enclave condition must also be ready for the enclave to resume.”
Intel has due to the fact produced software package updates to mitigate this vulnerability with SGX SDK variations 2.13 and 2.14 for Windows and Linux respectively. Microsoft, for its component, tackled the issue (CVE-2021-33767) in its July 2021 Patch Tuesday updates with Open up Enclave edition .17.1 of the SDK. The exploration team’s findings are anticipated to be introduced next month at the ACM Conference on Laptop and Communications Security.
“Asynchronous exception handling is a commodity performance for authentic-earth apps these days, which are ever more using enclaves,” the scientists said, incorporating the investigation highlights “the great importance of providing atomicity ensures at the OS-enclave interface for this sort of exceptions.”
Discovered this post attention-grabbing? Follow THN on Facebook, Twitter and LinkedIn to study extra exclusive articles we put up.
Some parts of this short article are sourced from:
thehackernews.com


 Employees Make Best Frontline Phishing Defense
Employees Make Best Frontline Phishing Defense