Cybersecurity researchers have disclosed two new attack approaches on licensed PDF documents that could potentially empower an attacker to alter a document’s noticeable articles by exhibiting destructive written content above the certified material without invalidating its signature.
“The attack concept exploits the adaptability of PDF certification, which will allow signing or including annotations to certified paperwork underneath distinctive permission levels,” mentioned scientists from Ruhr-College Bochum, who have systematically analyzed the security of the PDF specification in excess of the many years.
The conclusions were offered at the 42nd IEEE Symposium on Security and Privacy (IEEE S&P 2021) held this week.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The two attacks — dubbed Evil Annotation and Sneaky Signature attacks — hinge on manipulating the PDF certification course of action by exploiting flaws in the specification that governs the implementation of electronic signatures (aka approval signature) and its much more flexible variant identified as certification signatures.

Certification signatures also allow for distinct subsets of modifications on the PDF document based on the permission amount established by the certifier, such as the skill to write textual content to distinct form fields, provide annotations, or even insert many signatures.
The Evil Annotation Attack (EAA) is effective by modifying a certified doc that’s provisioned to insert annotations to include an annotation made up of destructive code, which is then despatched to the victim. On the other hand, the strategy behind the Sneaky Signature attack (SSA) is to manipulate the appearance by adding overlaying signature aspects to a doc that permits filling out sort fields.
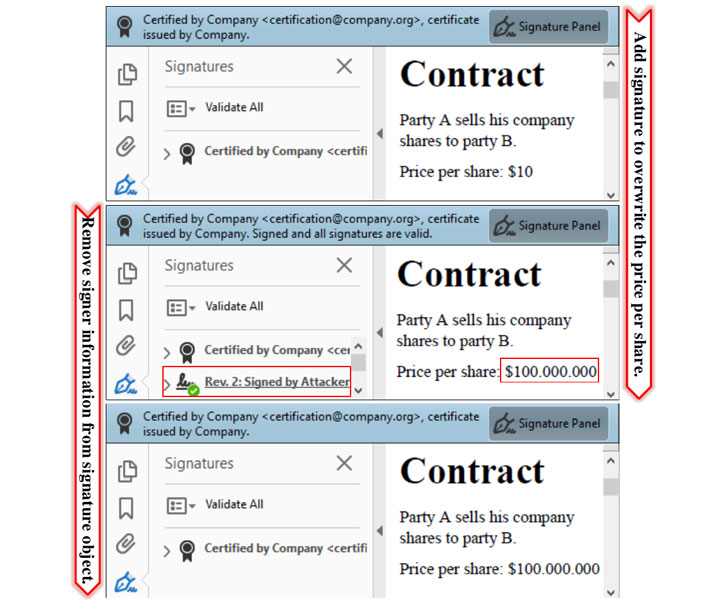
“By inserting a signature subject, the signer can outline the exact situation of the field, and moreover its physical appearance and articles, the scientists explained. “This adaptability is vital considering the fact that just about every new signature could incorporate the signer’s info. The facts can be a graphic, a text, or a blend of both of those. Yet, the attacker can misuse the flexibility to stealthily manipulate the doc and insert new material.”
In a hypothetical attack situation in depth by the academics, a certifier generates a accredited deal with delicate facts while enabling the possibility to increase more signatures to the PDF agreement. By using gain of these permissions, an attacker can modify the contents of the document, say, to show an Worldwide Financial institution Account Quantity (IBAN) below their regulate and fraudulently transfer money, as the sufferer, unable to detect the manipulation, accepts the tampered deal.
15 of 26 PDF purposes evaluated by the researchers, counting Adobe Acrobat Reader (CVE-2021-28545 and CVE-2021-28546), Foxit Reader (CVE-2020-35931), and Nitro Pro, have been observed susceptible to the EAA attack, enabling an attacker to transform the visible articles in the doc. Soda PDF Desktop, PDF Architect, and six other apps have been determined as vulnerable to SSA attacks.
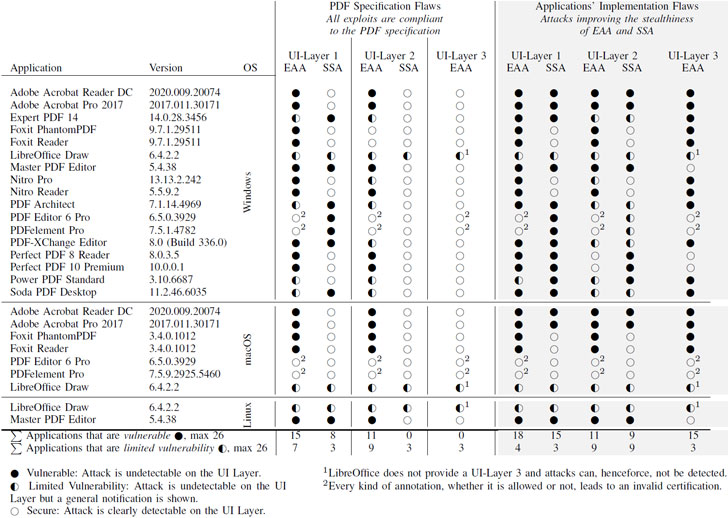
Extra troublingly, the review unveiled that it can be attainable to execute superior-privileged JavaScript code — e.g., redirect the consumer to a destructive web-site — in Adobe Acrobat Pro and Reader by sneaking these code by using EAA and SSA as an incremental update to the certified document. The weakness (CVE-2020-24432) was dealt with by Adobe as component of its Patch Tuesday update for November 2020.
To fend off this kind of attacks, the researchers advocate prohibiting FreeText, Stamp, and Redact annotations as nicely as making certain that signature fields are established up at described destinations in the PDF document prior to certification, together with penalizing any subsequent addition of signature fields with an invalid certification position. The researchers have also developed a Python-based mostly utility identified as PDF-Detector, which parses licensed documents to spotlight any suspicious factors found in the PDF document.
“Although neither EAA nor SSA can adjust the content material by itself – it generally continues to be in the PDF – annotations and signature fields can be made use of as an overlay to insert new content,” the researchers stated. “Victims opening the PDF are not able to distinguish these additions from common content. And even even worse: annotations can embed large privileged JavaScript code that is allowed to be added to specified licensed documents.”
Uncovered this post attention-grabbing? Stick to THN on Fb, Twitter and LinkedIn to read through more exceptional information we write-up.
Some components of this write-up are sourced from:
thehackernews.com


 ‘OMG it’s a bug!’ Beware the bells and whistles around vulnerability disclosures
‘OMG it’s a bug!’ Beware the bells and whistles around vulnerability disclosures