No fewer than 1,220 Person-in-the-Center (MitM) phishing sites have been found out as concentrating on well known on-line expert services like Instagram, Google, PayPal, Apple, Twitter, and LinkedIn with the purpose of hijacking users’ qualifications and carrying out even more follow-on attacks.
The findings come from a new study undertaken by a team of scientists from Stony Brook University and Palo Alto Networks, who have demonstrated a new fingerprinting procedure that helps make it feasible to detect MitM phishing kits in the wild by leveraging their intrinsic network-stage attributes, properly automating the discovery and analysis of phishing websites.
Dubbed “PHOCA” — named just after the Latin phrase for “seals” — the resource not only facilitates the discovery of beforehand unseen MitM phishing toolkits, but also be utilized to detect and isolate malicious requests coming from such servers.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Phishing toolkits aim to automate and streamline the work required by attackers to perform credential-thieving campaigns. They are packaged ZIP data files that occur with ready-to-use email phishing templates and static copies of web internet pages from legit internet websites, allowing for risk actors to impersonate the specific entities in a bid to trick unsuspecting victims into disclosing non-public information.
But the increasing adoption of two-factor authentication (2FA) by on the net solutions in current decades intended that these conventional phishing toolkits can no extended be an productive technique to split into accounts shielded by the extra layer of security. Enter MitM phishing toolkits, which go a move more by entirely obviating the want for protecting “real looking” web internet pages.
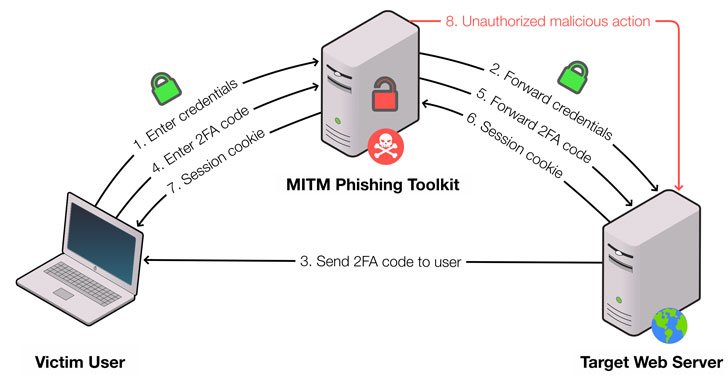
A MitM phishing kit permits fraudsters to sit in between a sufferer and an on line provider. Relatively than environment up a bogus web-site which is distributed through spam e-mails, the attackers deploy a fraudulent site that mirrors the are living information of the goal web-site and functions as a conduit to forward requests and responses amongst the two get-togethers in authentic-time, hence allowing the extraction of credentials and session cookies from 2FA-authenticated accounts.
“They purpose as reverse proxy servers, brokering interaction amongst target buyers and target web servers, all whilst harvesting sensitive info from the network details in transit,” Stony Brook University researchers Brian Kondracki, Babak Amin Azad, Oleksii Starov, and Nick Nikiforakis mentioned in an accompanying paper.
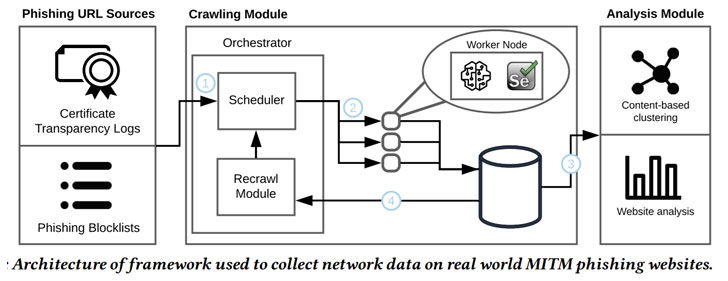
The technique devised by the researchers involves a equipment understanding classifier that makes use of network-degree features this kind of as TLS fingerprints and network timing discrepancies to classify phishing web-sites hosted by MitM phishing toolkits on reverse proxy servers. It also involves a knowledge-selection framework that screens and crawls suspicious URLs from open-resource phishing databases like OpenPhish and PhishTank, amongst some others.

The core thought is to measure the round-trip time (RTT) delays that occur out of putting a MitM phishing package, which, in flip, increases the length from when the sufferer browser sends a ask for to when it receives a response from the goal server owing to the fact that the reverse proxy mediates the communication sessions.
“As two distinctive HTTPS classes must be maintained to broker interaction concerning the victim user and focus on web server, the ratio of various packet RTTs, such as a TCP SYN/ACK ask for and HTTP GET ask for, will be a great deal bigger when communicating with a reverse proxy server than with an origin web server instantly,” the scientists defined. “This ratio is further more magnified when the reverse proxy server intercepts TLS requests, which retains legitimate for MitM phishing toolkits.”
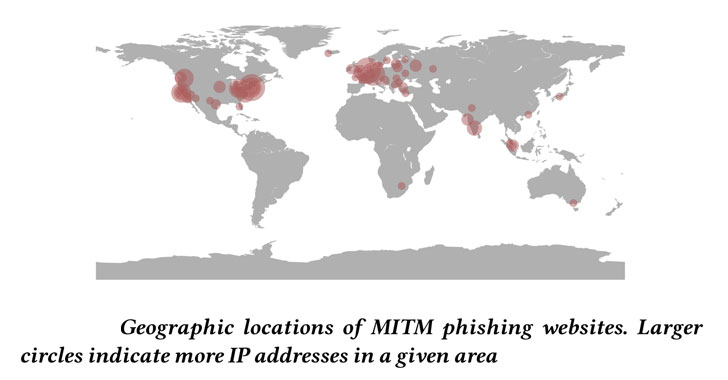
In an experimental evaluation that lasted 365 days amongst March 25, 2020 and March 25, 2021, the examine uncovered a whole of 1,220 sites as operated working with MitM phishing kits that ended up scattered mainly throughout the U.S. and Europe, and relied on hosting companies from Amazon, DigitalOcean, Microsoft, and Google. Some of the brands that were being most targeted by such kits include Instagram, Google, Fb, Microsoft Outlook, PayPal, Apple, Twitter, Coinbase, Yahoo, and LinkedIn.
“PHOCA can be specifically built-in into present web infrastructure these types of as phishing blocklist services to expand their coverage on MitM phishing toolkits, as perfectly as popular internet sites to detect ma- licious requests originating from MitM phishing toolkits,” the researchers reported, incorporating that uniquely figuring out MitM phishing toolkits can “greatly enhance the ability of web-provider vendors to pinpoint malicious login requests and flag them before authentication is accomplished.”
Found this short article appealing? Follow THN on Fb, Twitter and LinkedIn to go through a lot more exceptional content we post.
Some areas of this posting are sourced from:
thehackernews.com

 HMRC issues scam warning ahead of Self Assessment deadline
HMRC issues scam warning ahead of Self Assessment deadline