The operators of the rising cross-platform BianLian ransomware have elevated their command-and-handle (C2) infrastructure this month, a progress that alludes to an improve in the group’s operational tempo.
BianLian, penned in the Go programming language, was very first identified in mid-July 2022 and has claimed 15 target corporations as of September 1, cybersecurity business [redacted] said in a report shared with The Hacker News.
It’s truly worth noting that the double extortion ransomware family has no link to an Android banking trojan of the exact same identify, which targets cellular banking and cryptocurrency applications to siphon sensitive data.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

First obtain to sufferer networks is reached by way of prosperous exploitation of the ProxyShell Microsoft Trade Server flaws, leveraging it to possibly fall a web shell or an ngrok payload for observe-on actions.
“BianLian has also focused SonicWall VPN units for exploitation, an additional popular focus on for ransomware teams,” [redacted] researchers Ben Armstrong, Lauren Pearce, Brad Pittack, and Danny Quist said.
Unlike a different new Golang malware identified as Agenda, the BianLian actors exhibit dwell instances of up to 6 weeks from the time of preliminary access and the true encryption function, a period that’s properly over the median intruder dwell time of 15 times reported in 2021.
Moreover leveraging residing-off-the-land (LotL) strategies for network profiling and lateral motion, the team is also acknowledged to deploy a custom implant as an alternative implies for protecting persistent obtain to the network.
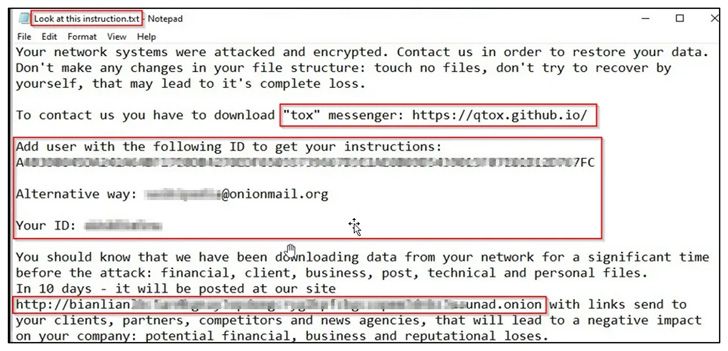
The most important target of the backdoor, for each [redacted], is to retrieve arbitrary payloads from a distant server, load it into memory, and then execute them.
BianLian, identical to Agenda, is able of booting servers in Windows secure mode to execute its file-encrypting malware while simultaneously remaining undetected by security alternatives installed on the system.

Other techniques taken to defeat security limitations contain deleting shadow copies, purging backups, and managing its Golang encryptor module by way of Windows Remote Administration (WinRM) and PowerShell scripts.
The earliest recognised C2 server related with BianLian is claimed to have appeared online in December 2021. But the infrastructure has since witnessed a “troubling explosion” to surpass 30 active IP addresses.
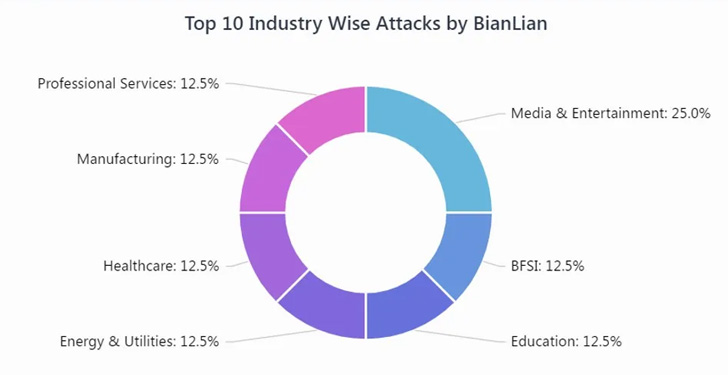
In accordance to Cyble, which detailed the modus operandi of the ransomware previously this month, qualified providers span a number of industry sectors these as media, banking, strength, manufacturing, education and learning, health care, and skilled services. A greater part of the firms are centered in North The united states, the U.K., and Australia.
BianLian is still yet another indication of cybercriminals’ focused efforts to go on hopping techniques so as to avoid detection. It also provides to a increasing selection of threats utilizing Go as the foundational language, enabling adversaries to make swift modifications in a one codebase that can then be compiled for a number of platforms.
“BianLian have demonstrated themselves to be adept with the Living of the Land (LOL) methodology to move laterally, altering their operations based mostly on the capabilities and defenses they encountered in the network,” the scientists claimed.
Identified this post interesting? Adhere to THN on Facebook, Twitter and LinkedIn to read through far more exceptional content we put up.
Some parts of this short article are sourced from:
thehackernews.com


 US imposes sanctions on Nvidia’s chip sales in China
US imposes sanctions on Nvidia’s chip sales in China