A Pakistani risk actor properly socially engineered a variety of ministries in Afghanistan and a shared governing administration personal computer in India to steal sensitive Google, Twitter, and Fb qualifications from its targets and stealthily get obtain to governing administration portals.
Malwarebytes’ most up-to-date results go into depth about the new tactics and equipment adopted by the APT group recognised as SideCopy, which is so-known as for the reason that of its makes an attempt to mimic the infection chains involved with yet another team tracked as SideWinder and mislead attribution.
“The lures used by SideCopy APT are commonly archive information that have embedded 1 of these documents: LNK, Microsoft Publisher or Trojanized Applications,” Malwarebytes researcher Hossein Jazi mentioned, including the embedded data files are tailor-made to concentrate on government and armed service officers primarily based in Afghanistan and India.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The revelation will come near on the heels of disclosures that Meta took measures to block destructive actions carried out by the group on its system by applying passionate lures to compromise individuals with ties to the Afghan authorities, military, and legislation enforcement in Kabul.
Some of the outstanding attacks were being waged versus staff connected with the Administration Business of the President (AOP) of Afghanistan as effectively as the Ministry of International affairs, Ministry of Finance, and the National Procurement Authority, resulting in the theft of social media passwords and password-safeguarded documents. SideCopy also broke into a shared computer in India and harvested qualifications from authorities and training expert services.
In addition, the actor is claimed to have siphoned many Microsoft Workplace paperwork, which includes names, numbers, and email addresses of officials and databases that contains information related to id playing cards, diplomatic visas, and asset registrations from the Afghani authorities websites, all of which are predicted to be utilized as long run decoys or to gasoline even further attacks towards the men and women by themselves.
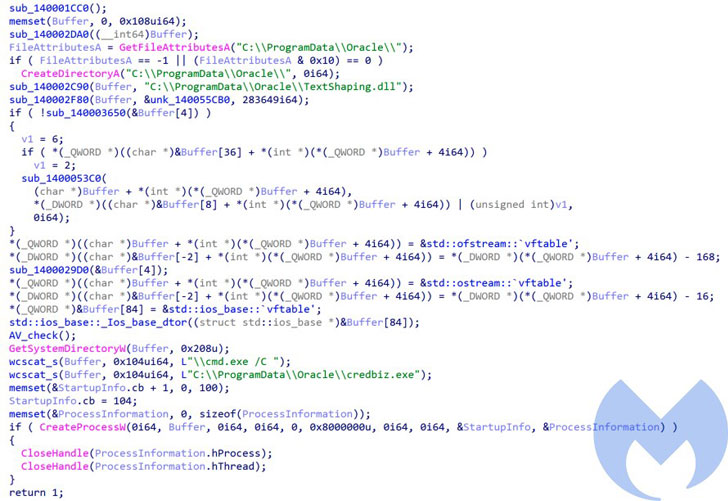
The cyber espionage marketing campaign noticed by Malwarebytes involves the focus on opening the entice doc, primary to the execution of a loader that is used to drop a subsequent-phase remote obtain trojan identified as ActionRAT, which is capable of uploading data files, executing commands received from a server, and even download additional payloads.

Also dropped by the loader is a new details stealer dubbed Automobile Stealer, which is programmed to collect Microsoft Place of work documents, PDF paperwork, textual content documents, database information, and images ahead of exfiltrating the info to its server more than HTTP or TCP.
This is much from the 1st time SideCopy APT’s methods have arrive to mild. In September 2020, cybersecurity organization Quick Mend disclosed particulars about an espionage attack aimed at Indian protection units and armed forces staff at least given that 2019 with an intention to steal delicate details.
Then previously this July, Cisco Talos scientists exposed the hacking group’s myriad infection chains delivering bespoke and commodity remote access trojans such as CetaRAT, Allakore, and njRAT in what they identified as an expansion of malware campaigns targeting entities in India.
Observed this article appealing? Observe THN on Fb, Twitter and LinkedIn to read through a lot more exceptional content material we write-up.
Some sections of this article are sourced from:
thehackernews.com



 Planned Parenthood cyber attack exposes data of 400,000 patients
Planned Parenthood cyber attack exposes data of 400,000 patients