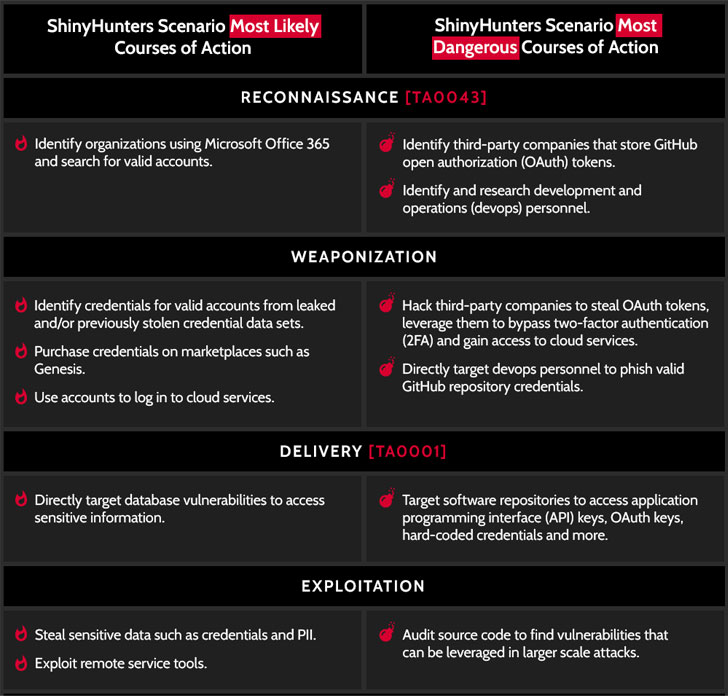
ShinyHunters, a notorious cybercriminal underground team that is been on a info breach spree since final year, has been observed browsing companies’ GitHub repository supply code for vulnerabilities that can be abused to phase larger scale attacks, an analysis of the hackers’ modus operandi has disclosed.
“Largely working on Raid Community forums, the collective’s moniker and drive can partly be derived from their avatar on social media and other community forums: a shiny Umbreon Pokémon,” Intel 471 scientists stated in a report shared with The Hacker News. “As Pokémon gamers hunt and collect “shiny” figures in the game, ShinyHunters collects and resells person data.”
The revelation will come as the typical cost of a data breach rose from $3.86 million to $4.24 million, building it the greatest average price in 17 years, with compromised credentials responsible for 20% of the breaches documented by about 500 businesses.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Since growing to prominence in April 2020, ShinyHunters has claimed obligation for a string of data breaches, which include Tokopedia, Wattpad, Pixlr, Bonobos, BigBasket, Mathway, Unacademy, MeetMindful, and Microsoft’s GitHub account, amid some others.
An assessment by Risk Dependent Security located that the menace actor has exposed a whole of far more than 1.12 million exclusive email addresses belonging to S&P 100 organizations, instruction, government and army entities as of late 2020.
Past 7 days, the group commenced offering a databases purportedly that contains the personalized data of 70 million AT&T prospects for a beginning selling price of $200,000, whilst the U.S. telecom service provider has denied struggling a breach of its programs.
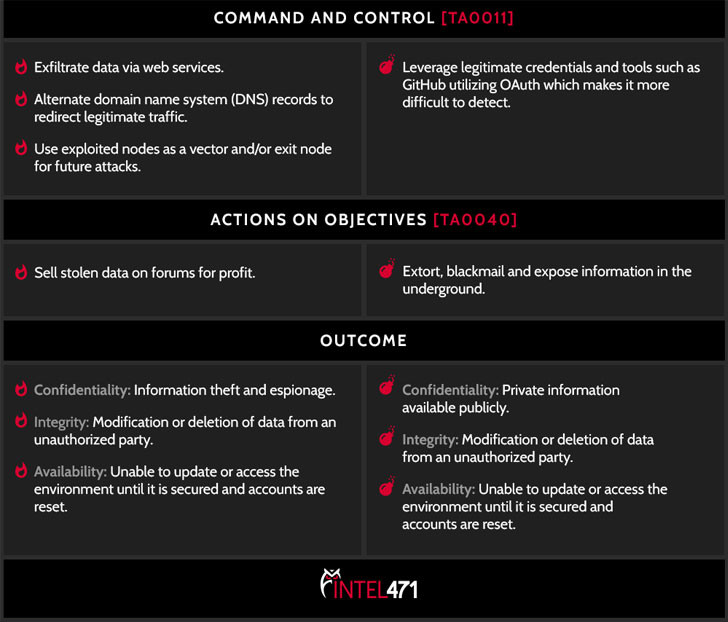
ShinyHunters has a checkered history of compromising internet sites and developer repositories to steal credentials or API keys to a company’s cloud providers, which are subsequently abused to get accessibility to databases and collect delicate facts to be resold for gain or printed for no cost on hacker discussion boards.

The adversary has also been noticed targeting DevOps personnel or GitHub repositories in get to steal legitimate OAuth tokens, leveraging them to breach cloud infrastructure and bypass any two-factor authentication mechanisms.
“ShinyHunters may well not have as considerably notoriety as the ransomware teams that are currently producing havoc for enterprises all more than the world. Nonetheless, tracking actors like this are essential to avoiding your company from currently being strike with this kind of an attack,” the researchers said.
“The facts ShinyHunters gathers is usually turned all-around and offered on the similar underground marketplaces exactly where ransomware actors use it to start their very own attacks. If enterprises can transfer to detect exercise like ShinyHunters, they in switch can cease ransomware attacks just before they are at any time launched.”
Observed this short article fascinating? Adhere to THN on Fb, Twitter and LinkedIn to read through additional distinctive content material we publish.
Some parts of this report are sourced from:
thehackernews.com


 State Department reportedly suffers a cyber attack
State Department reportedly suffers a cyber attack