Microsoft explained it won’t be correcting or is pushing patches to a later on day for a few of the four security flaws uncovered in its Teams company communication platform previously this March.
The disclosure comes from Berlin-based cybersecurity business Constructive Security, which discovered that the implementation of the website link preview attribute was inclined to a quantity of issues that could “make it possible for accessing inner Microsoft products and services, spoofing the hyperlink preview, and, for Android consumers, leaking their IP handle, and DoS’ing their Teams application/channels.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Of the four vulnerabilities, Microsoft is reported to have dealt with only 1 that outcomes in IP tackle leakage from Android products, with the tech large noting that a deal with for the denial-of-service (DoS) flaw will be viewed as in a potential variation of the merchandise. The issues were being responsibly disclosed to the business on March 10, 2021.
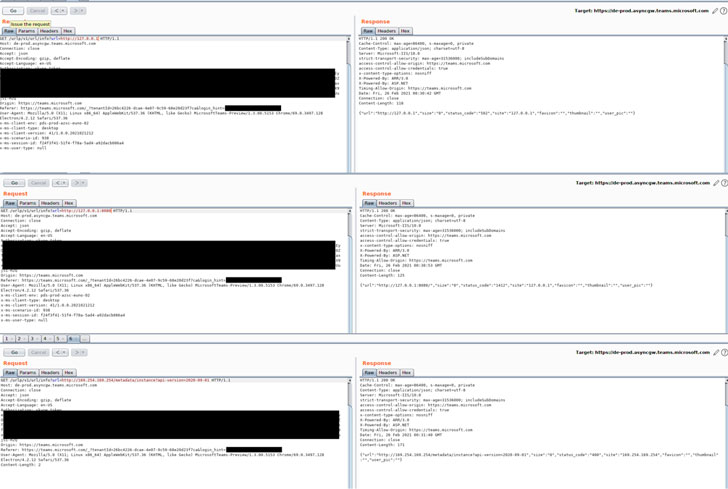
Main amongst the flaws is a server-side ask for forgery (SSRF) vulnerability in the endpoint “/urlp/v1/url/data” that could be exploited to glean facts from Microsoft’s regional network. Also uncovered is a spoofing bug whereby the preview backlink focus on can be altered to level to any malicious URL while holding the primary backlink, preview impression and description intact, letting attackers to disguise malicious one-way links and phase enhanced phishing attacks.
The DoS vulnerability, which impacts the Android model of Groups, could trigger the application to crash just by sending a message with a specifically crafted link preview that contains an invalid goal as an alternative of a authentic URL. The final of the issues fears an IP tackle leak, which also influences the Android app. By intercepting messages that include a hyperlink preview to point the thumbnail URL to a non-Microsoft domain, Good Security stated it is really probable to achieve entry to a user’s IP deal with and consumer agent knowledge.
“Whilst the identified vulnerabilities have a restricted effects, it really is stunning each that such easy attack vectors have seemingly not been analyzed for right before, and that Microsoft does not have the willingness or assets to safeguard their consumers from them,” Beneficial Security’s co-founder Fabian Bräunlein reported.
Observed this posting fascinating? Observe THN on Fb, Twitter and LinkedIn to read through a lot more special material we put up.
Some elements of this report are sourced from:
thehackernews.com



 Cyber-Attack on Belgium’s Military
Cyber-Attack on Belgium’s Military