Security scientists have uncovered the very first acknowledged malware, dubbed “Siloscope,” focusing on Windows Server containers to infect Kubernetes clusters in cloud environments.
“Siloscape is heavily obfuscated malware targeting Kubernetes clusters through Windows containers,” stated Device 42 researcher Daniel Prizmant. “Its key objective is to open a backdoor into inadequately configured Kubernetes clusters in order to run malicious containers such as, but not minimal to, cryptojackers.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Siloscape, 1st detected in March 2021, is characterized by many procedures, which includes focusing on common cloud programs these kinds of as web servers to attain an original foothold by means of regarded vulnerabilities, next which it leverages Windows container escape techniques to split out of the confines of the container and obtain remote code execution on the underlying node.
A container is an isolated, light-weight silo for running an software on the host functioning procedure. The malware’s title — quick for silo escape — is derived from its principal purpose to escape the container, in this circumstance, the silo. To realize this, Siloscape makes use of a system termed Thread Impersonation.
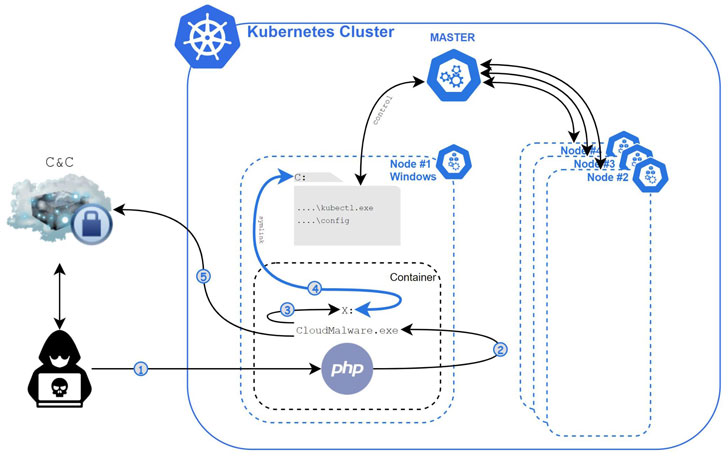
“Siloscape mimics CExecSvc.exe privileges by impersonating its key thread and then calls NtSetInformationSymbolicLink on a recently made symbolic url to crack out of the container,” claimed Prizmant. “Additional exclusively, it backlinks its nearby containerized X travel to the host’s C generate.”
Armed with this privilege, the malware then makes an attempt to abuse the node’s credentials to spread across the cluster, just before anonymously creating a link to its command-and-regulate (C2) server utilizing a Tor proxy for further more guidelines, together with taking benefit of the computing resources in a Kubernetes cluster for cryptojacking and even exfiltrating delicate knowledge from applications managing in the compromised clusters.

Immediately after gaining obtain to the C2 server, Unit 42 reported it observed 23 active victims, with the server hosting a total of 313 people. The campaign is reported to have started at minimum all-around Jan. 12, 2020, based on the creation date of the C2 server, suggesting that the malware could just be a tiny part of a greater marketing campaign that commenced above a yr back.
“Contrary to most cloud malware, which primarily focuses on source hijacking and denial of service (DoS), Siloscape doesn’t limit by itself to any specific purpose,” Prizmant famous. “Alternatively, it opens a backdoor to all sorts of malicious functions.” In addition to securely configuring Kubernetes clusters, it truly is also advised to deploy Hyper-V containers if containerization is used as a kind of the security boundary.
Found this write-up intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to read much more exceptional information we write-up.
Some pieces of this post are sourced from:
thehackernews.com

 IT Pro 20/20: What the EU’s new AI rules mean for business
IT Pro 20/20: What the EU’s new AI rules mean for business