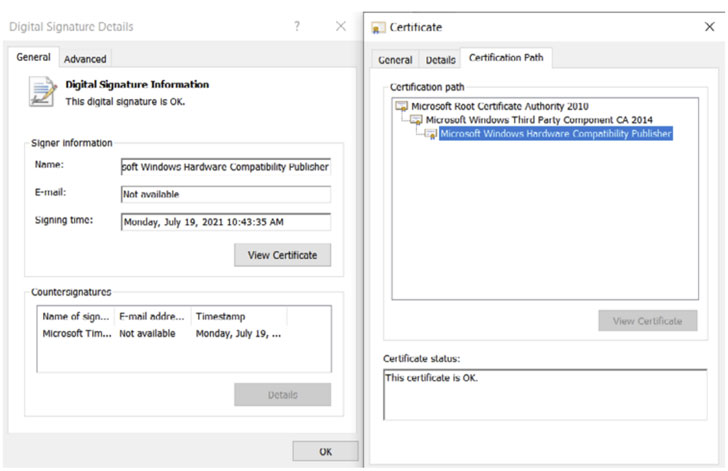
A freshly determined rootkit has been identified with a legitimate digital signature issued by Microsoft which is used to proxy site visitors to internet addresses of interest to the attackers for around a yr targeting on the internet players in China.
Bucharest-headquartered cybersecurity technology organization Bitdefender named the malware “FiveSys,” contacting out its achievable credential theft and in-activity-buy hijacking motives. The Windows maker has given that revoked the signature adhering to dependable disclosure.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“Digital signatures are a way of creating trust,” Bitdefender researchers reported in a white paper, including “a legitimate electronic signature will help the attacker navigate close to the operating system’s restrictions on loading 3rd-party modules into the kernel. When loaded, the rootkit makes it possible for its creators to attain just about limitless privileges.”
Rootkits are both of those evasive and stealthy as they present threat actors an entrenched foothold on to victims’ techniques and conceal their destructive actions from the working process (OS) as perfectly as from anti-malware remedies, enabling the adversaries to keep extended persistence even after OS reinstallation or alternative of the tough push.
In the case of FiveSys, the malware’s primary aim is to redirect and route internet site visitors for the two HTTP and HTTPS connections to destructive domains below the attacker’s manage by using a personalized proxy server. The rootkit operators also hire the apply of blocking the loading of drivers from competing teams using a signature blocklist of stolen certificates to avoid them from having handle of the equipment.
“To make probable takedown attempts a lot more difficult, the rootkit will come with a constructed-in listing of 300 domains on the ‘.xyz’ [top-level domain],” the scientists noted. “They seem to be to be generated randomly and saved in an encrypted variety inside the binary.”
The advancement marks the next time whereby destructive motorists with legitimate electronic signatures issued by Microsoft by means of the Windows Hardware Quality Labs (WHQL) signing process have slipped by way of the cracks. In late June 2021, German cybersecurity business G Info disclosed specifics of yet another rootkit dubbed “Netfilter” (and tracked by Microsoft as “Retliften”), which, like FiveSys, also aimed at avid gamers in China.
Uncovered this article attention-grabbing? Adhere to THN on Fb, Twitter and LinkedIn to examine far more distinctive written content we submit.
Some elements of this report are sourced from:
thehackernews.com


 22% of Brits Received Proof of Vaccination Phishing Email in Past Six Months
22% of Brits Received Proof of Vaccination Phishing Email in Past Six Months