Cybersecurity scientists on Tuesday exposed specifics of a formerly undocumented UEFI (Unified Extensible Firmware Interface) bootkit that has been place to use by threat actors to backdoor Windows programs as early as 2012 by modifying a reputable Windows Boot Supervisor binary to realize persistence, once once again demonstrating how technology meant to safe the natural environment prior to loading the running method is increasingly getting to be a “tempting focus on.”
Slovak cybersecurity organization ESET codenamed the new malware “ESPecter” for its skill to persist on the EFI Program Partition (ESP), in addition to circumventing Microsoft Windows Driver Signature Enforcement to load its have unsigned driver that can be used to aid espionage routines this kind of as doc theft, keylogging, and monitor checking by periodically capturing screenshots.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
“ESPecter demonstrates that threat actors are relying not only on UEFI firmware implants when it comes to pre-OS persistence and, even with the present security mechanisms like UEFI Protected Boot, commit their time into building malware that would be very easily blocked by this kind of mechanisms, if enabled and configured accurately,” ESET researchers Martin Smolár and Anton Cherepanov reported in a specialized produce-up published Tuesday.
The growth marks the fourth time genuine-planet conditions of UEFI malware have been found out so considerably, following LoJax, MosaicRegressor, and most not long ago FinFisher, the very last of which was found leveraging the same approach of compromise to persist on the ESP in the kind of a patched Windows Boot Manager.
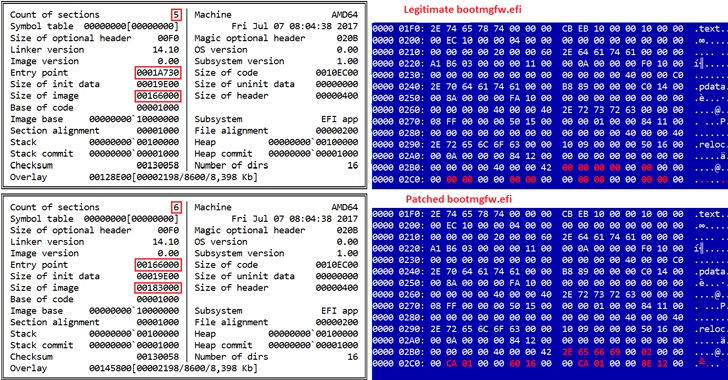
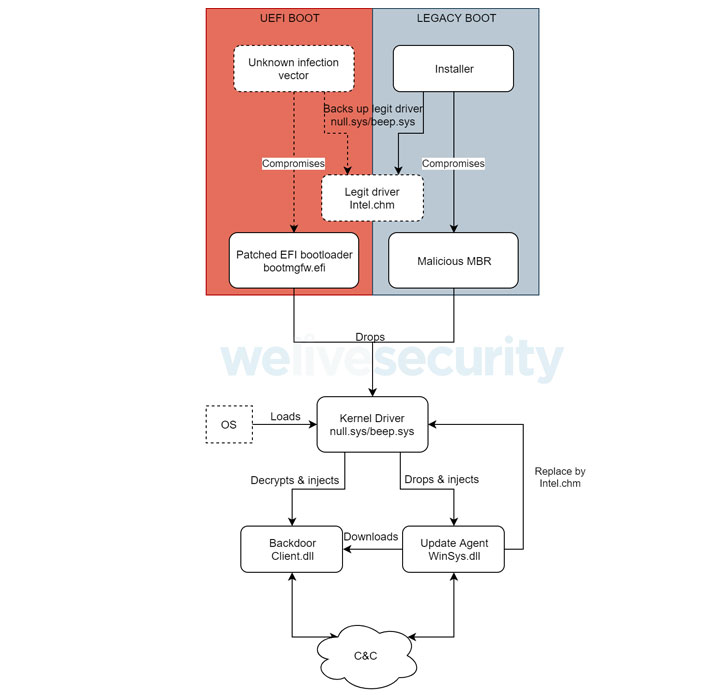
“By patching the Windows Boot Supervisor, attackers attain execution in the early phases of the method boot process, ahead of the functioning method is thoroughly loaded,” the researchers reported. “This enables ESPecter to bypass Windows Driver Signature Enforcement (DSE) in get to execute its possess unsigned driver at system startup.”
On the other hand, on devices that help Legacy BIOS Boot Method, ESPecter gains persistence by altering the master boot history (MBR) code located in the initial bodily sector of the disk travel to interfere with the loading of the boot manager and load the malicious kernel driver, which is developed to load added user-manner payloads and established up the keylogger, in advance of erasing its very own traces from the equipment.

In the remaining period, the driver is utilised to inject future-phase consumer-manner factors into certain technique processes to build communications with a remote server, thus enabling an attacker to commandeer the compromised machine and take over handle, not to point out download and execute a lot more malware or commands fetched from the server.
ESET did not attribute the bootkit to a particular nation-point out or hacking group, but the use of Chinese debug messages in the user-method shopper payload has raised the probability that it could be the get the job done of an unfamiliar Chinese-speaking danger actor.
“Even even though Safe Boot stands in the way of executing untrusted UEFI binaries from the ESP, above the very last few several years we have been witness to many UEFI firmware vulnerabilities affecting countless numbers of products that allow for disabling or bypassing Safe Boot,” the researchers pointed out. “This exhibits that securing UEFI firmware is a tough task and that the way a variety of distributors apply security insurance policies and use UEFI companies is not constantly ideal.”
Found this post appealing? Comply with THN on Facebook, Twitter and LinkedIn to read through extra exclusive information we post.
Some elements of this post are sourced from:
thehackernews.com

 How to Build an Incident-Response Plan, Before Security Disaster Strikes
How to Build an Incident-Response Plan, Before Security Disaster Strikes