Emotet, a notorious email-centered malware behind a number of botnet-pushed spam strategies and ransomware assaults, contained a flaw that permitted cybersecurity researchers to activate a eliminate-change and reduce the malware from infecting units for six months.
“Most of the vulnerabilities and exploits that you browse about are great information for attackers and terrible information for the relaxation of us,” Binary Defense’s James Quinn claimed.
“On the other hand, it’s vital to continue to keep in head that malware is software program that can also have flaws. Just as attackers can exploit flaws in reputable computer software to trigger hurt, defenders can also reverse-engineer malware to explore its vulnerabilities and then exploit those to defeat the malware.”
The get rid of-change was alive involving February 6, 2020, to August 6, 2020, for 182 times, in advance of the malware authors patched their malware and shut the vulnerability.
Due to the fact its initial identification in 2014, Emotet has advanced from its preliminary roots as a banking malware to a “Swiss Military knife” that can serve as a downloader, info stealer, and spambot based on how it truly is deployed.
Early this February, it produced a new feature to leverage by now infected products to determine and compromise refreshing victims related to nearby Wi-Fi networks.
Alongside with this attribute update arrived a new persistence system, according to Binary Protection, which “created a filename to help you save the malware on each individual victim process, using a randomly chosen exe or dll process filename from the program32 listing.”
The adjust in itself was straight-ahead: it encrypted the filename with an XOR critical that was then saved to the Windows registry price established to the victim’s volume serial range.
The very first variation of the get rid of-switch created by Binary Defense, which went live about 37 hours soon after Emotet unveiled the earlier mentioned variations, utilized a PowerShell script that would make the registry vital worth for just about every sufferer and set the knowledge for every single benefit to null.
This way, when the malware checked the registry for the filename, it would end up loading an vacant exe “.exe,” consequently stopping the malware from running on the target technique.
“When the malware tries to execute ‘.exe,’ it would be unable to operate because ‘.’ translates to the present-day performing listing for lots of working units,” Quinn observed.
EmoCrash to Thwart Emotet
That’s not all. In an improvised edition of the destroy-swap, named EmoCrash, Quinn said he was ready to exploit a buffer overflow vulnerability uncovered in the malware’s installation program to crash Emotet during the installation approach, thereby efficiently blocking consumers from getting contaminated.
So alternatively of resetting the registry price, the script functions by pinpointing the program architecture to crank out the put in registry value for the user’s quantity serial variety, employing it to help save a buffer of 832 bytes.
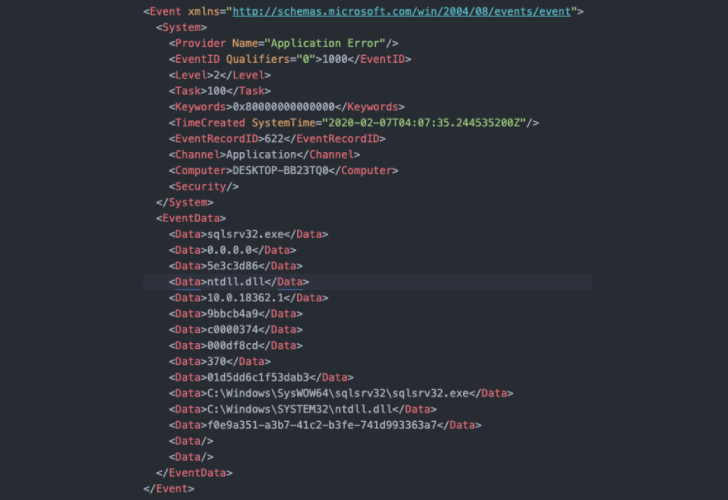
“This tiny data buffer was all that was required to crash Emotet, and could even be deployed prior to infection (like a vaccine) or mid-infection (like a killswitch),” Quinn said. “Two crash logs would appear with party ID 1000 and 1001, which could be used to identify endpoints with disabled and dead Emotet binaries after deployment of the killswitch (and a computer restart).”
To hold it a top secret from danger actors and patch their code, Binary Protection claimed it coordinated with Pc Emergency Response Teams (CERTs) and Group Cymru to distribute the EmoCrash exploit script to prone organizations.
While Emotet retired its registry essential-primarily based installation process in mid-April, it was not till August 6 when an update to the malware loader solely taken out the susceptible registry benefit code.
“On July 17, 2020, Emotet at last returned to spamming soon after their a number of months-prolonged progress time period,” Quinn mentioned. “With EmoCrash nevertheless active at the start off of their comprehensive return, up right up until August 6, EmoCrash was in a position to give total protection from Emotet.”
“Not poor for a 832-byte buffer!,” he included.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Identified this article fascinating? Stick to THN on Fb, Twitter and LinkedIn to examine far more unique material we post.


 Vodafone Provides Trend Micro’s “Worry-Free” Detection Service to its Security Giving
Vodafone Provides Trend Micro’s “Worry-Free” Detection Service to its Security Giving