A nascent info stealer identified as Mars has been observed in campaigns that take gain of cracked variations of the malware to steal info saved in web browsers and cryptocurrency wallets.
“Mars Stealer is staying distributed by way of social engineering tactics, malspam strategies, destructive program cracks, and keygens,” Morphisec malware researcher Arnold Osipov stated in a report revealed Tuesday.
Centered on the Oski Stealer and initial discovered in June 2021, Mars Stealer is claimed to be frequently underneath enhancement and readily available for sale on above 47 underground forums, darknet websites, and Telegram channels, costing only $160 for a lifetime membership.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

Facts stealers enable adversaries to vacuum personalized information from compromised techniques, which include stored credentials and browser cookies, which are then marketed on criminal marketplaces or employed as a springboard for launching more attacks.
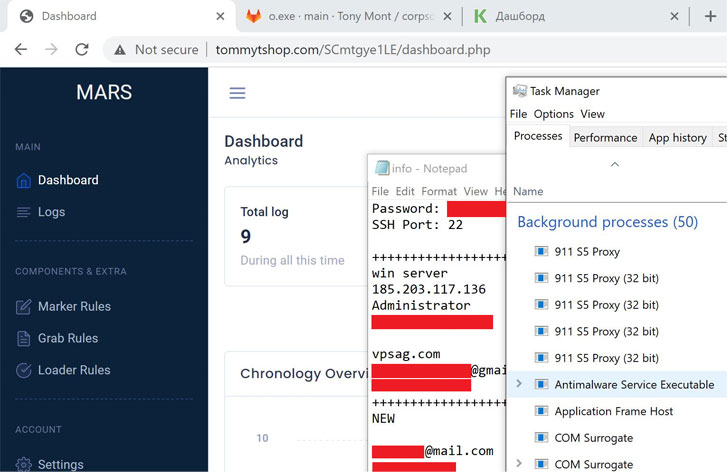
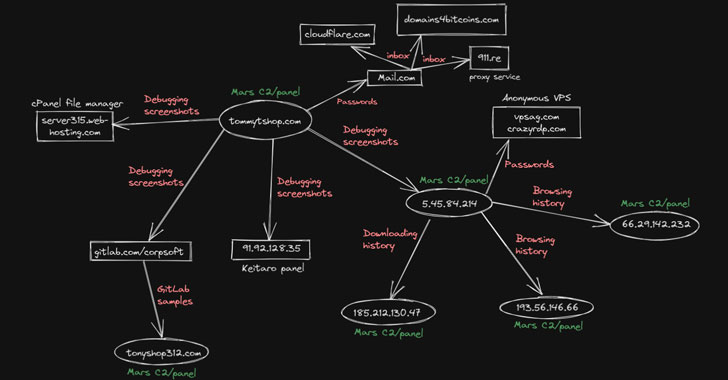
The release of Mars Stealer previous 12 months has also been accompanied by a continuous increase in attack campaigns, some of which have concerned the use of a cracked edition of the malware that has been configured in these a fashion that it has exposed critical property on the internet, inadvertently leaking details about the menace actor’s infrastructure.
Also notable is a campaign observed past thirty day period that siphoned the passwords belonging to students, faculty customers, and information makers who have downloaded trojanized versions of legitimate apps.
On major of that, the cybersecurity organization noted that it “identified qualifications which led to the total compromise of a foremost health care infrastructure service provider in Canada, and a selection of significant-profile Canadian provider firms.”
Although Mars Stealer is most frequently distributed via spam email messaging containing a compressed executable, down load backlink, or document payload, it can be also propagated by using fraudulent cloned internet websites marketing perfectly-recognised software program this sort of as OpenOffice that ended up then pushed as a result of Google Ads.
The purpose is to leverage geographically targeted advertisements to trick potential victims looking for the authentic application into browsing a destructive web-site as an alternative, in the long run foremost to the deployment of the malware.
Mars Stealer, for its section, is engineered to harvest and exfiltrate browser autofill knowledge, credit rating card information and facts, browser extension specifics, such as that of cryptocurrency wallets like Metamask, Coinbase Wallet, and Binance Wallet, and program metadata.
But for the reason that the menace actor compromised their possess machine with the Mars Stealer for the duration of debugging, the OPSEC error authorized the researchers to attribute the campaign to a Russian speaker as properly as uncover facts about the adversary’s use of GitLab and stolen credentials to put Google Adverts.
“Infostealers present an available entry stage to criminal action,” Osipov reported, incorporating these equipment “empower beginner cybercriminals to construct a status they can leverage to get additional powerful malware from extra complex actors.”
Uncovered this short article exciting? Follow THN on Facebook, Twitter and LinkedIn to examine a lot more exceptional content we put up.
Some elements of this posting are sourced from:
thehackernews.com


 MSHTML Flaw Exploited to Attack Russian Dissidents
MSHTML Flaw Exploited to Attack Russian Dissidents