FireEye and Microsoft on Thursday stated they found out 3 more malware strains in relationship with the SolarWinds source-chain attack, which includes a “subtle 2nd-phase backdoor,” as the investigation into the sprawling espionage campaign proceeds to generate fresh new clues about the threat actor’s techniques and techniques.
Dubbed GoldMax (aka SUNSHUTTLE), GoldFinder, and Sibot, the new set of malware adds to a expanding listing of destructive resources these types of as Sunspot, Sunburst (or Solorigate), Teardrop, and Raindrop that were being stealthily delivered to business networks by alleged Russian operatives.
“These equipment are new parts of malware that are special to this actor,” Microsoft said. “They are tailor-built for precise networks and are assessed to be launched just after the actor has obtained accessibility by way of compromised qualifications or the SolarWinds binary and just after going laterally with Teardrop and other hands-on-keyboard steps.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Microsoft also took the chance to identify the actor guiding the attacks in opposition to SolarWinds as NOBELIUM, which is also getting tracked under various monikers by the cybersecurity local community, like UNC2452 (FireEye), SolarStorm (Palo Alto Unit 42), StellarParticle (CrowdStrike), and Dark Halo (Volexity).
Whilst Sunspot was deployed into the create environment to inject the Sunburst backdoor into SolarWinds’s Orion network checking system, Teardrop and Raindrop have been primarily utilized as put up-exploitation instruments to laterally move throughout the network and provide the Cobalt Strike Beacon.
Spotted concerning August to September 2020, SUNSHUTTLE is a Golang-based malware that acts as a command-and-management backdoor, establishing a secure relationship with an attacker-managed server to receive commands to download and execute data files, add files from the technique to the server, and execute functioning system instructions on the compromised machine.
For its element, FireEye said it observed the malware at a victim compromised by UNC2452, but added it has not been capable to absolutely confirm the backdoor’s link to the risk actor. The company also said it identified SUNSHUTTLE in August 2020 right after it was uploaded to a public malware repository by an unnamed U.S.-based entity.
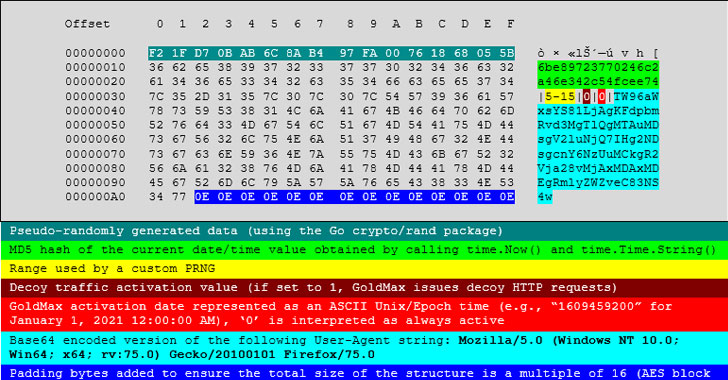
1 of the most notable functions of GoldMax is the means to cloak its destructive network visitors with seemingly benign site visitors by pseudo-randomly picking referrers from a checklist of well known web-site URLs (these types of as www.bing.com, www.yahoo.com, www.fb.com, www.twitter.com, and www.google.com) for decoy HTTP GET requests pointing to C2 domains.
“The new SUNSHUTTLE backdoor is a advanced 2nd-phase backdoor that demonstrates simple but elegant detection evasion procedures by using its ‘blend-in’ traffic capabilities for C2 communications,” FireEye thorough. “SUNSHUTTLE would functionality as a second-stage backdoor in this kind of a compromise for conducting network reconnaissance together with other Sunburst-relevant tools.”
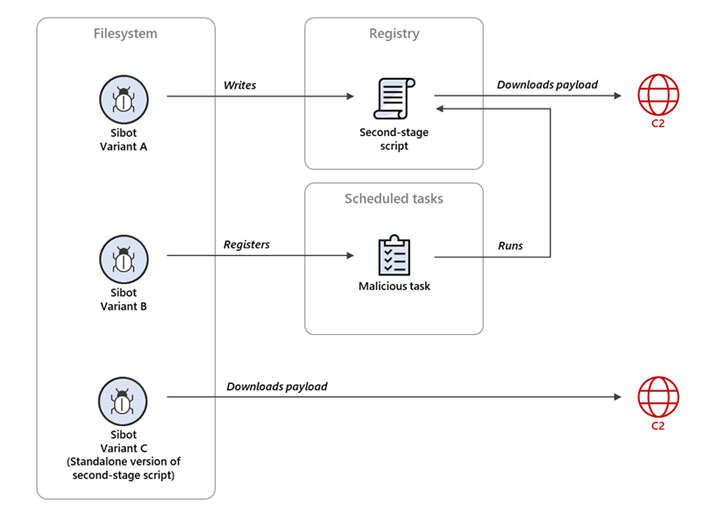
GoldFinder, also prepared in Go, is an HTTP tracer device for logging the route a packet requires to achieve a C2 server. In contrast, Sibot is a twin-function malware executed in VBScript which is built to reach persistence on infected machines prior to downloading and executing a payload from the C2 server. Microsoft reported it observed a few obfuscated variants of Sibot.
Even as the various parts of SolarWinds attack puzzle slide into put, the advancement the moment yet again underscores the scope and sophistication in the array of solutions utilised to penetrate, propagate, and persist in target environments.
“These capabilities vary from formerly identified NOBELIUM tools and attack styles, and reiterate the actor’s sophistication,” Microsoft reported. “In all stages of the attack, the actor demonstrated a deep information of computer software instruments, deployments, security computer software and programs prevalent in networks, and tactics routinely utilized by incident response groups.”
Uncovered this post exciting? Observe THN on Facebook, Twitter and LinkedIn to examine much more special content we put up.
Some areas of this article are sourced from:
thehackernews.com

 What is data and big data mining? An easy guide
What is data and big data mining? An easy guide