A beforehand undocumented strain of Android spy ware with comprehensive data collecting abilities has been found disguised as a ebook very likely intended to target the Uyghur local community in China.
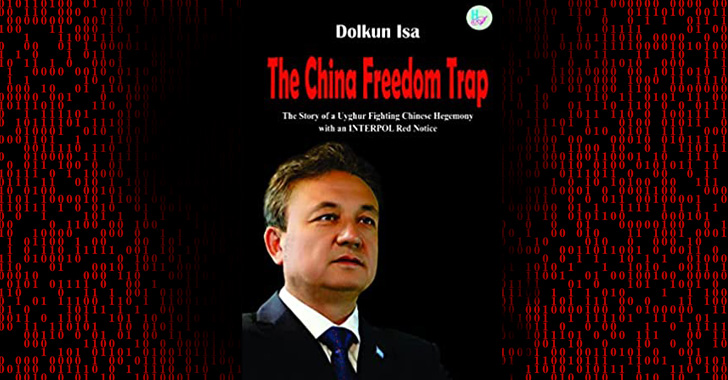
The malware will come under the guise of a e-book titled “The China Freedom Lure,” a biography published by the exiled Uyghur leader Dolkun Isa.


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“In light-weight of the ongoing conflict among the Govt of the People’s Republic of China and the Uyghur community, the malware disguised as the e book is a beneficial bait used by menace actors (TAs) to unfold destructive infection in the specific group,” cybersecurity company Cyble mentioned in a report printed Monday.
The existence of the malware samples, which arrive with the package deal title “com.emc.pdf,” was very first disclosed by researchers from the MalwareHunterTeam late very last month.
Dispersed exterior of the formal Google Perform Store, the app, the moment mounted and opened, shows a handful of web pages of the e-book, like the cover webpage, an introduction, and a letter purportedly despatched by Michael Kozak and Sam Brownback to Isa on June 15, 2018, condoling his mother’s loss of life.

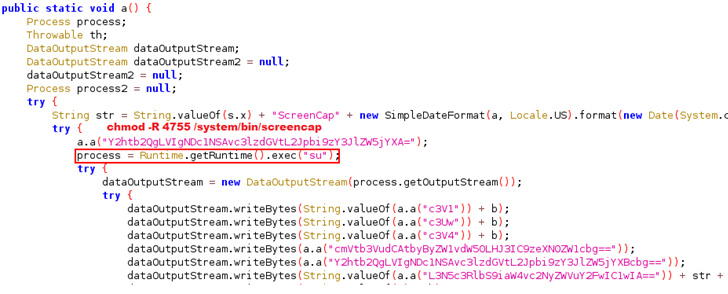
In truth, having said that, the malicious APK file is engineered to:
- hide application icon,
- steal product and SIM information and facts,
- steal SMS messages, contacts and connect with logs,
- identify neighboring mobile data (gained sign power, Cell ID site),
- make Calls and Send out SMSs on behalf of victims,
- delete SMS and get in touch with logs,
- as nicely as take images from the contaminated device’s digicam and seize its display screen.
“TAs are leveraging a variety of strategies, which include regional and biogeographical conflicts, to satisfy their malicious intentions,” the scientists claimed. “In this circumstance, they are viewed taking advantage of the Uyghur-Chinese conflict to concentrate on unsuspecting people.”
Identified this post exciting? Abide by THN on Facebook, Twitter and LinkedIn to examine much more special content material we write-up.
Some areas of this posting are sourced from:
thehackernews.com

 QNAP Warns of New DeadBolt Ransomware Attacks Exploiting Photo Station Flaw
QNAP Warns of New DeadBolt Ransomware Attacks Exploiting Photo Station Flaw