New conclusions launched last 7 days showcase the overlapping resource code and tactics in between the operators of Shamoon and Kwampirs, indicating that they “are the very same group or definitely near collaborators.”
“Analysis evidence displays identification of co-evolution between the two Shamoon and Kwampirs malware households all through the recognised timeline,” Pablo Rincón Crespo of Cylera Labs claimed.
“If Kwampirs is based mostly on the first Shamoon, and Shamoon 2 and 3 marketing campaign code is based on Kwampirs, […] then the authors of Kwampirs would be possibly the similar as the authors of Shamoon, or should have a extremely strong romance, as has been observed in excess of the study course of many many years,” Rincón Crespo included.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Shamoon, also identified as DistTrack, functions as an data-stealing malware that also incorporates a harmful ingredient that permits it to overwrite the Learn Boot Record (MBR) with arbitrary knowledge so as to render the contaminated machine inoperable.
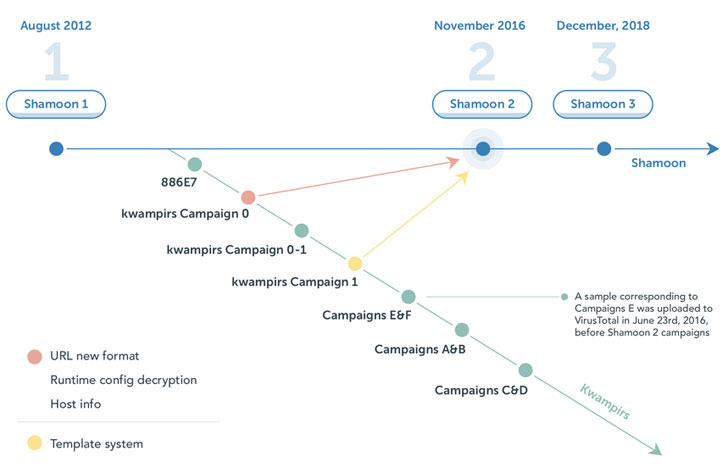
The malware, created by the eponymous hacking crew also tracked as Magic Hound, Timberworm, COBALT GIPSY, was very first documented by Broadcom-owned Symantec in August 2012. At the very least two up to date variations of Shamoon have given that emerged, Shamoon 2 in 2016 and Shamoon 3 in 2018.
In July 2021, the U.S. federal government attributed Shamoon as the handiwork of Iranian state-sponsored actors, linking it to cyber offensives targeting industrial control units.
On the other hand, attack exercise involving the Kwampirs backdoor has been linked to a menace group acknowledged as Orangeworm, with Symantec disclosing an intrusion campaign aimed at entities in the healthcare sector in the U.S., Europe, and Asia.
“First discovered in January 2015, Orangeworm has also conducted targeted attacks against businesses in relevant industries as part of a greater supply-chain attack in order to access their meant victims,” Symantec stated in an analysis in April 2018.
Cylera Labs’ uncovering of the connection stems from malware artifacts and beforehand unnoticed parts, just one of which is explained to be an intermediary “stepping stone” edition. It can be a Shamoon dropper but sans the wiper feature, even though concurrently reusing the same loader code as Kwampirs.
What’s a lot more, code-level similarities have been uncovered concerning Kwampirs and subsequent versions of Shamoon. This includes the features to retrieve technique metadata, fetch MAC tackle, and the victim’s keyboard structure information as very well as the use of the exact same InternetOpenW Windows API to craft HTTP requests to the command-and-control (C2) server.
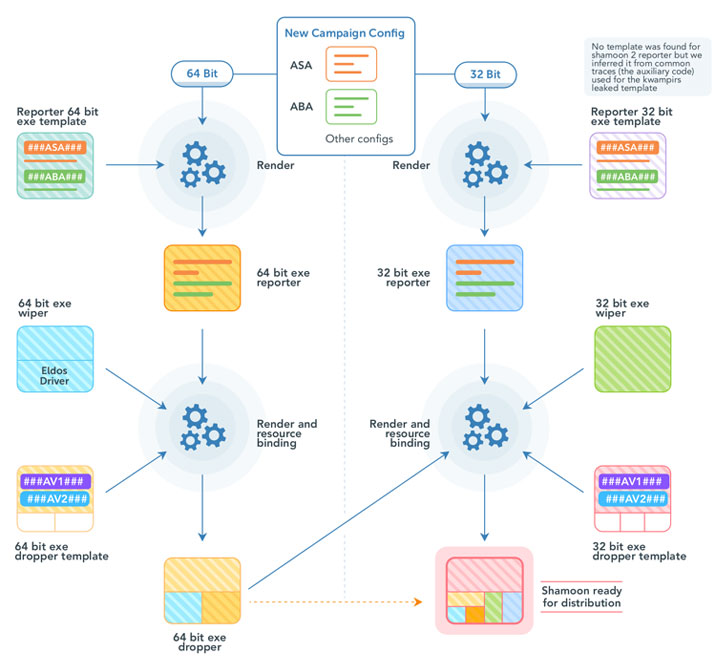
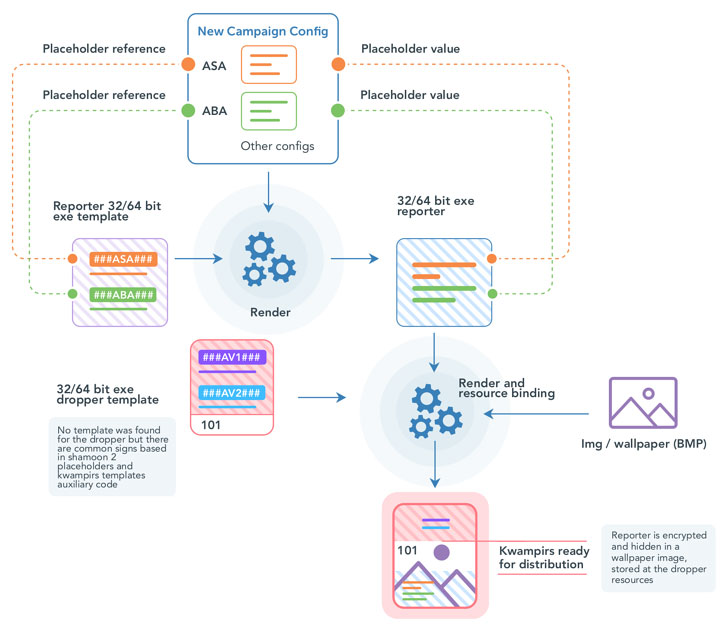
Also put to use is a frequent template technique to develop the reporter module that residences capabilities to add host facts and obtain more payloads to execute from their C2 servers, a attribute that was lacking in the very first variation of Shamoon.
In connecting the disparate dots, the investigation has led to the evaluation that Kwampirs is probable dependent on Shamoon 1 and that Shamoon 2 inherited some of its code from Kwampirs, implying that the operators of the two the malware are different sub-teams of a bigger umbrella teams or that it is the work of a single actor.
These types of a declare just isn’t without the need of precedence. Just last 7 days, Cisco Talos detailed the TTPs of another Iranian actor termed MuddyWater, noting that the nation-state actor is a “conglomerate” of multiple groups working independently fairly than a solitary danger actor team.
“These conclusions, if in fact correct, would recast Kwampirs as a massive-scale, multi-calendar year attack on world-wide healthcare supply chains done by a international point out actor,” the researchers concluded.
“The knowledge gathered and programs accessed in these campaigns have a wide selection of probable usage, which includes theft of intellectual home, accumulating of clinical documents of targets like dissidents or armed service leaders, or reconnaissance to aid in the preparing of potential damaging attacks.”
Located this article interesting? Follow THN on Fb, Twitter and LinkedIn to examine far more distinctive material we article.
Some pieces of this article are sourced from:
thehackernews.com




 Avast Suspends Operations in Russia and Belarus
Avast Suspends Operations in Russia and Belarus