A initially-of-its-variety security investigation of iOS Locate My operate has shown a novel attack area that tends to make it achievable to tamper with the firmware and load malware onto a Bluetooth chip that’s executed when an iPhone is “off.”
The system requires gain of the actuality that wireless chips similar to Bluetooth, In close proximity to-discipline interaction (NFC), and ultra-wideband (UWB) go on to operate whilst iOS is shut down when moving into a “energy reserve” Very low Electric power Manner (LPM).
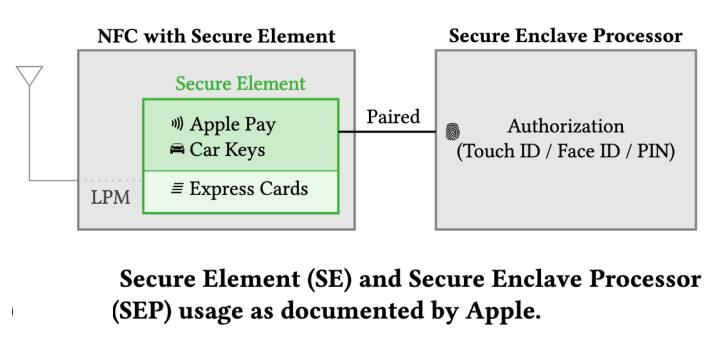
Although this is carried out so as to empower capabilities like Uncover My and aid Convey Card transactions, all the three wireless chips have direct access to the secure component, academics from the Protected Cellular Networking Lab (SEEMOO) at the Specialized College of Darmstadt reported in a paper.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“The Bluetooth and UWB chips are hardwired to the Safe Element (SE) in the NFC chip, storing tricks that really should be obtainable in LPM,” the scientists claimed.
“Because LPM support is carried out in hardware, it can not be eradicated by switching computer software components. As a result, on contemporary iPhones, wireless chips can no more time be trustworthy to be turned off right after shutdown. This poses a new menace model.”
The results are set to be presented at the ACM Meeting on Security and Privacy in Wi-fi and Cell Networks (WiSec 2022) this week.
The LPM capabilities, freshly released previous yr with iOS 15, make it achievable to observe lost equipment using the Uncover My network. Current units with Extremely-wideband assist include iPhone 11, iPhone 12, and iPhone 13.
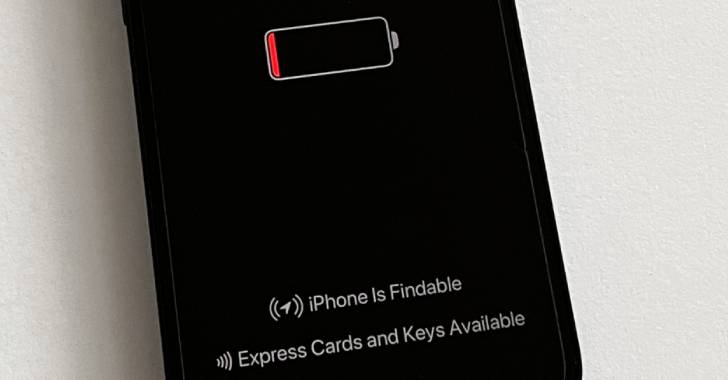
A concept displayed when turning off iPhones reads so: “iPhone remains findable just after ability off. Come across My assists you locate this iPhone when it is misplaced or stolen, even when it is in electric power reserve manner or when powered off.”
Calling the recent LPM implementation “opaque,” the researchers not only in some cases noticed failures when initializing Locate My commercials through energy off, effectively contradicting the aforementioned message, they also observed that the Bluetooth firmware is neither signed nor encrypted.
By using benefit of this loophole, an adversary with privileged access can create malware that is able of staying executed on an iPhone Bluetooth chip even when it is driven off.
Having said that, for this sort of a firmware compromise to transpire, the attacker need to be able to converse to the firmware through the running procedure, modify the firmware image, or obtain code execution on an LPM-enabled chip in excess of-the-air by exploiting flaws this kind of as BrakTooth.

Set otherwise, the notion is to alter the LPM software thread to embed malware, these as those people that could notify the malicious actor of a victim’s Come across My Bluetooth broadcasts, enabling the menace actor to retain remote tabs on the concentrate on.
“Alternatively of shifting present operation, they could also incorporate completely new functions,” SEEMOO scientists pointed out, adding they responsibly disclosed all the issues to Apple, but that the tech huge “had no feed-back.”
With LPM-associated characteristics taking a far more stealthier method to carrying out its intended use scenarios, SEEMOO known as on Apple to contain a hardware-based mostly change to disconnect the battery so as to reduce any surveillance worries that could occur out of firmware-level attacks.
“Considering that LPM assist is centered on the iPhone’s hardware, it simply cannot be eradicated with process updates,” the researchers reported. “So, it has a extended-long lasting influence on the overall iOS security model.”
“Layout of LPM capabilities would seem to be mostly driven by functionality, without the need of taking into consideration threats outside the house of the supposed programs. Find My just after ability off turns shutdown iPhones into monitoring gadgets by design and style, and the implementation inside the Bluetooth firmware is not secured against manipulation.”
Found this article intriguing? Comply with THN on Facebook, Twitter and LinkedIn to examine more exceptional material we submit.
Some areas of this write-up are sourced from:
thehackernews.com

 ‘The People Hacker’ Jenny Radcliffe Inducted into Infosecurity Europe’s Hall of Fame
‘The People Hacker’ Jenny Radcliffe Inducted into Infosecurity Europe’s Hall of Fame