A group of lecturers has proposed a device mastering solution that makes use of reliable interactions involving units in Bluetooth networks as a basis to deal with system-to-device authentication reliably.
Identified as “Verification of Conversation Authenticity” (aka Via), the recurring authentication plan aims to resolve the difficulty of passive, continuous authentication and automated deauthentication the moment two devices are paired with just one one more, which remain authenticated until eventually an express deauthentication motion is taken, or the authenticated session expires.
“Think about equipment that pair through Bluetooth, which typically adhere to the sample of pair at the time, belief indefinitely. After two equipment link, all those products are bonded right up until a consumer explicitly removes the bond. This bond is possible to stay intact as extended as the units exist, or until finally they transfer ownership,” Travis Peters, a single of the co-authors of the analyze, mentioned.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“The elevated adoption of (Bluetooth-enabled) IoT equipment and experiences of the inadequacy of their security would make indefinite trust of products problematic. The reality of ubiquitous connectivity and recurrent mobility provides rise to a myriad of prospects for equipment to be compromised,” Peters additional.
Authentication is a method to confirm that an specific or a process is, in fact, who or what it claims to be. While authentication can also be obtained by identification — a little something who you are — the most recent research ways it from a verification point of view in that it aims to validate that applications and equipment interact in a manner that is steady with their prior observations. In other terms, the device’s conversation styles act as a barometer of its all round actions.
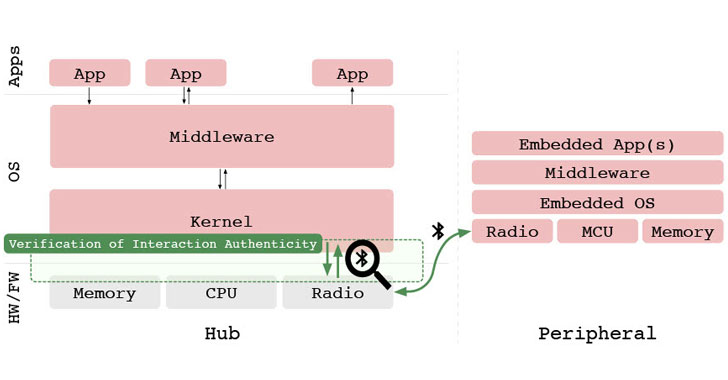
To this conclude, the recurring validation of interaction patterns enables for authenticating the system by cross-checking the device’s conduct towards a formerly discovered equipment understanding product that represents usual, reputable interactions, with the initially authentication factor being the use of regular Bluetooth identifiers and credentials.
“For example, a person that has a blood-stress gadget could genuinely only care if a blood-pressure check product is ‘hooked up’ to the measurement application, and is running in a way that is dependable with how a blood-tension keep an eye on need to run,” the scientists outlined.
“Presumably, so long as these houses keep, there is no speedy or obvious risk. If, having said that, a device connects as a blood-tension observe and then goes on to interact in a way that is inconsistent with standard interactions for this variety of device, then there may perhaps be trigger for concern.”

Through functions by extracting characteristics from packet headers and payloads and evaluating them to a verification design to corroborate no matter if the ongoing interactions are steady with this recognized genuine behavioral product, and if so, allow the products to go on speaking with each and every other. As a consequence, any deviation from authentic interactions will consequence in failed verification, enabling devices to take measures to mitigate any potential risk.
The design is produced making use of a combination of characteristics, this sort of as n-grams developed from deep packet inspection, protocol identifiers and packet varieties, packet lengths, and packet directionality. The dataset is composed of a selection of 300 Bluetooth HCI network traces that seize interactions concerning 20 unique wise wellbeing and wise home products and 13 diverse smartphone applications mounted on a Nexus 5 smartphone managing Android 6..1.
“We see VIA’s recurring verification of interaction designs as a kind of second factor for authenticating the gadget,” the scientists explained. “As a outcome of this plan, we introduce the notion of recurring behavioral authentication for Bluetooth connections, which can be built-in into a Bluetooth gateway gadget, this sort of as a smartphone.”
Found this short article interesting? Observe THN on Fb, Twitter and LinkedIn to study more special information we write-up.
Some elements of this short article are sourced from:
thehackernews.com

 Ransomware May Have Cost US Schools Over $6bn in 2020
Ransomware May Have Cost US Schools Over $6bn in 2020