Two new Android surveillanceware family members have been uncovered to goal military services, nuclear, and election entities in Pakistan and Kashmir as component of a pro-India, state-sponsored hacking campaign.
Dubbed Hornbill and Sunbird, the malware impersonates legitimate or seemingly innocuous providers to deal with its tracks, only to stealthily acquire SMS, encrypted messaging app articles, and geolocation, between other kinds of delicate details.
The findings released by Lookout is the consequence of an assessment of 18GB of exfiltrated facts that was publicly exposed from at minimum 6 insecurely configured command-and-handle (C2) servers positioned in India.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
“Some noteworthy targets bundled an specific who applied for a posture at the Pakistan Atomic Strength Commission, folks with a lot of contacts in the Pakistan Air Drive (PAF), as properly as officers dependable for electoral rolls (Booth Level Officers) positioned in the Pulwama district of Kashmir,” the scientists stated in a Wednesday evaluation.

In all, the attacks targeted 156 victims with phone numbers from India, Pakistan, and Kazakhstan more than the very last various a long time.
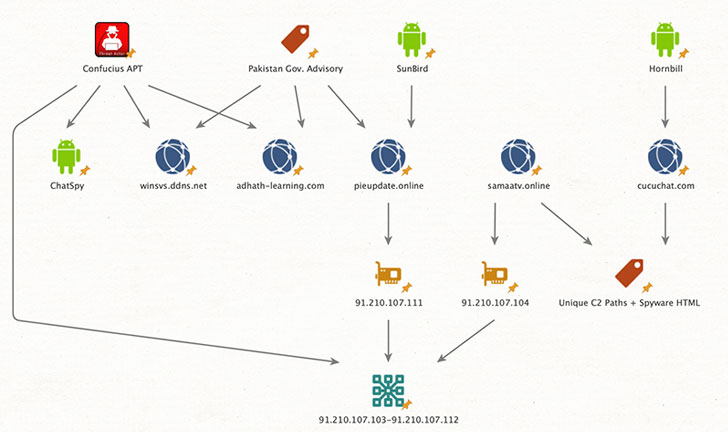
Lookout attributed the two instruments to an sophisticated persistent threat (APT) tracked as Confucius, a team recognised for its attacks on South Asian nations around the world at minimum given that 2013. The cybersecurity firm referred to as Hornbill a “passive reconnaissance instrument.”
When Hornbill appears to be derived from the identical code base as a formerly lively industrial surveillance solution recognized as MobileSpy, SunBird has been traced to a group of Indian developers behind one more cell tracking software package known as BuzzOut. Clues uncovered by the Lookout also level to the actuality the operators of Hornbill worked alongside one another at a variety of Android and iOS application development providers registered and functioning in or near the Indian metropolis of Chandigarh.
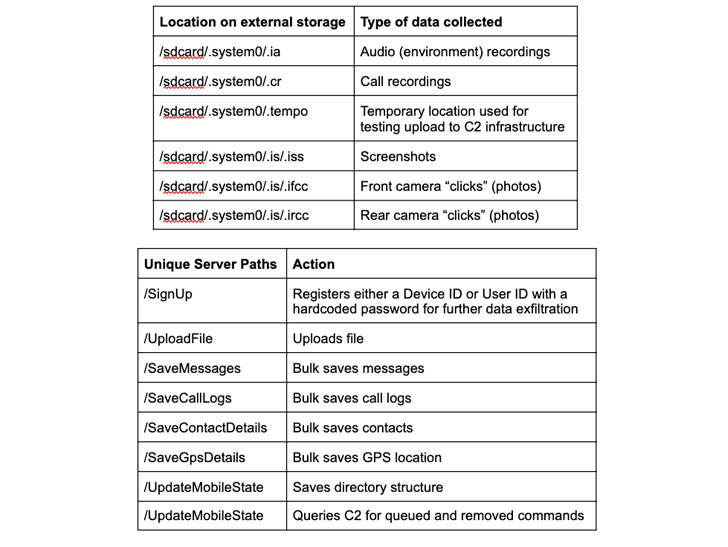
Both of those the pieces of adware are geared up to amass a huge range of info, these as connect with logs, contacts, procedure facts, area, pictures stored on exterior drives, history audio and video clip, seize screenshots, with a particular concentrate on plundering WhatsApp messages and voice notes by abusing Android’s accessibility APIs.
SunBird also differs from Hornbill in that the former capabilities remote obtain Trojan (RAT) performance, allowing for the attackers to execute arbitrary instructions on the goal device. In addition, it can be able of exfiltrating browser histories, calendar details, and even siphoning written content from BlackBerry Messenger and IMO fast messaging applications.
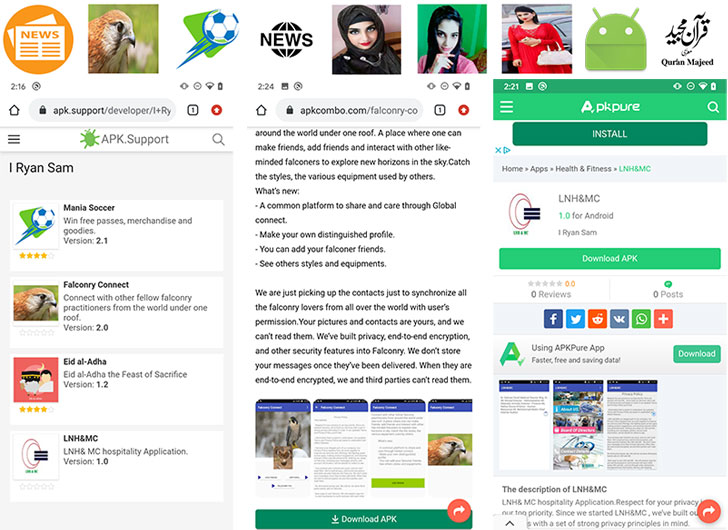
“Samples of SunBird have been uncovered hosted on third-party application stores, indicating 1 achievable distribution mechanism,” the scientists in-depth. “Considering a lot of of these malware samples are trojanized – as in they have total user functionality — social engineering may well also enjoy a portion in convincing targets to put in the malware.”
Lookout identified Hornbill samples as a short while ago as December 2020, indicating an active use of the malware considering that their discovery in 2018. On the other hand, Sunbird looks to have been actively deployed in 2018 and 2019, in advance of the risk actor shifted to a further Android-primarily based adware product or service named ChatSpy final 12 months.
Interestingly, the C2 infrastructure shared by Hornbill and SunBird reveals even further connections with other stalkerware operations performed by the Confucius team — like a publicly-obtainable 2018 Pakistani authorities advisory warning of a desktop malware campaign concentrating on officers and federal government staff — implying that the two tools are utilized by the exact actor for different surveillance uses.
While India has been a relatively new entrant in the spy ware and surveillance sector, Citizen Lab researchers previous June outed a mercenary hack-for-retain the services of group centered in Delhi referred to as BellTroX InfoTech that aimed to steal qualifications from journalists, advocacy groups, financial investment firms, and an array of other higher-profile targets.
Found this write-up appealing? Adhere to THN on Fb, Twitter and LinkedIn to browse more distinctive material we put up.
Some sections of this article are sourced from:
thehackernews.com


 Various Malware Lurks in Discord App to Target Gamers
Various Malware Lurks in Discord App to Target Gamers