Cybersecurity scientists uncovered fresh proof of an ongoing cyberespionage marketing campaign against Indian protection units and armed forces personnel at minimum considering the fact that 2019 with an aim to steal sensitive information and facts.
Dubbed “Operation SideCopy” by Indian cybersecurity firm Quick Heal, the assaults have been attributed to an innovative persistent menace (APT) team that has properly managed to continue to be under the radar by “copying” the ways of other menace actors these as the SideWinder.
Exploiting Microsoft Equation Editor Flaw
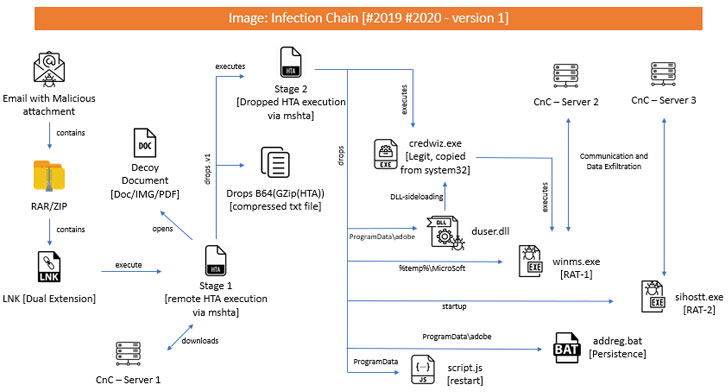
The campaign’s setting up point is an email with an embedded destructive attachment — either in the sort of a ZIP file containing an LNK file or a Microsoft Phrase document — that triggers an infection chain through a sequence of measures to obtain the ultimate-stage payload.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

Apart from figuring out a few various an infection chains, what is notable is the fact that one of them exploited template injection and Microsoft Equation Editor flaw (CVE-2017-11882), a 20-12 months old memory corruption issue in Microsoft Office, which, when exploited properly, let attackers execute distant code on a vulnerable device even without the need of person interaction.
Microsoft resolved the issue in a patch launched in November 2017.
As is frequently the situation with these malspam strategies, the attack relies on a little bit of social engineering to bait the person into opening a seemingly practical Term document that claims to be about the Indian government’s protection manufacturing plan.
What is actually additional, the LNK information have a double extension (“Defence-Creation-Plan-2020.docx.lnk”) and appear with document icons, therefore tricking an unsuspecting sufferer into opening the file.
At the time opened, the LNK files abuse “mshta.exe” to execute destructive HTA (small for Microsoft HTML Apps) information that are hosted on fraudulent internet websites, with the HTA data files produced employing an open up-sourced payload generation resource called CACTUSTORCH.
A Multi-phase Malware Shipping Procedure
The to start with phase HTA file involves a decoy document and a malicious .Net module that executes the said document and downloads a 2nd-phase HTA file, which in transform checks for the existence of preferred antivirus methods in advance of copying Microsoft’s credential back again and restore utility (“credwiz.exe”) to a various folder on the target device and modifying the registry to run the copied executable each and every time upon startup.
Therefore, when this file receives executed, not only does it facet-load a destructive “DUser.dll” file, it also launches the RAT module “winms.exe,” each of which are acquired from the stage-2 HTA.
“This DUser.dll will initiate the connection about this IP deal with ‘173.212.224.110’ more than TCP port 6102,” the researchers claimed.
“When efficiently linked, it will […] then commence for performing several operations based mostly on the command acquired from C2. For illustration, if C2 sends , then it collects the Laptop Name, Username, OS edition and so forth. and sends it back again to C2.”
Stating the RAT shared code-stage similarities with Allakore Remote, an open-sourced distant-entry application published in Delphi, Rapid Heal’s Seqrite workforce pointed out that the Trojan employed Allakore’s RFB (distant frame buffer) protocol to exfiltrate facts from the infected technique.
Possible Back links to Transparent Tribe APT
In addition, a few attack chains are also claimed to have dropped a beforehand unseen .Web-based mostly RAT (identified as “Crimson RAT” by Kaspersky researchers) that will come geared up with a huge array of abilities, like obtain documents, clipboard information, eliminate processes, and even execute arbitrary commands.
While the modus operandi of naming DLL information shares similarities with the SideWinder group, the APT’s heavy reliance on the open up-sourced toolset and an totally diverse C2 infrastructure led the researchers to conclude with reasonable confidence that the threat actor is of Pakistani origin — precisely the Transparent Tribe group, which has been not long ago joined to numerous attacks focusing on the Indian military and government staff.
“Therefore, we suspect that the actor driving this operation is a sub-division under (or element of) Clear-Tribe APT group and are just copying TTPs of other risk actors to mislead the security community,” Swift Heal explained.
Uncovered this report attention-grabbing? Adhere to THN on Facebook, Twitter and LinkedIn to browse much more exclusive content we put up.
Some parts of this article is sourced from:
thehackernews.com

 Ivanti Adds VPN and MDM Technolgies in Double Acquisition
Ivanti Adds VPN and MDM Technolgies in Double Acquisition