A fiscally inspired risk actor infamous for placing its sights on retail, hospitality, and leisure industries has been observed deploying a absolutely new backdoor on infected programs, indicating the operators are repeatedly retooling their malware arsenal to keep away from detection and keep below the radar.
The beforehand undocumented malware has been dubbed “Sardonic” by Romanian cybersecurity technology firm Bitdefender, which it encountered throughout a forensic investigation in the wake of an unsuccessful attack carried out by FIN8 aimed at an unnamed financial institution found in the U.S.


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Stated to be below energetic advancement, “Sardonic backdoor is very potent and has a extensive variety of capabilities that aid the threat actor leverage new malware on the fly without updating elements,” Bitdefender researchers Eduard Budaca and Victor Vrabie claimed in a report shared with The Hacker News.
Because rising on the scene in January 2016, FIN8 has leveraged a multitude of methods these kinds of as spear-phishing and malicious software such as PUNCHTRACK and BADHATCH to steal payment card information from place-of-sale (POS) systems.
The threat group, which is regarded for taking prolonged breaks in between campaigns to fantastic-tune its techniques and increase the success amount of its operations, conducts cyber incursions generally by “residing off the land” attacks, working with designed-in tools and interfaces like PowerShell as well as getting advantage of reputable products and services like sslip.io to disguise their action.
Previously this March, Bitdefender uncovered FIN8’s return following a 12 months-and-a-half hiatus to concentrate on insurance plan, retail, technology, and chemical industries in the U.S., Canada, South Africa, Puerto Rico, Panama, and Italy with a revamped edition of the BADHATCH implant showcasing upgraded capabilities, together with screen capturing, proxy tunneling, credential theft, and fileless execution.

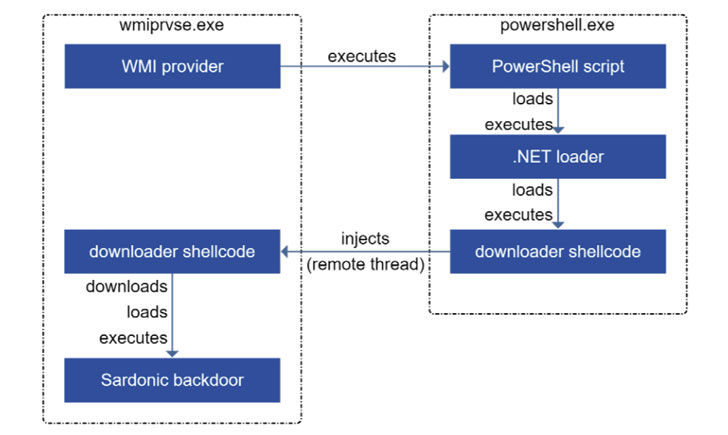
In the most up-to-date incident analyzed by the organization, the attackers are said to have infiltrated the goal network to perform specific reconnaissance, right before carrying out lateral motion and privilege escalation functions to deploy the malware payload. “There were many makes an attempt to deploy the Sardonic backdoor on domain controllers in get to continue with privilege escalation and lateral movement, but the malicious command strains were being blocked,” the researchers mentioned.
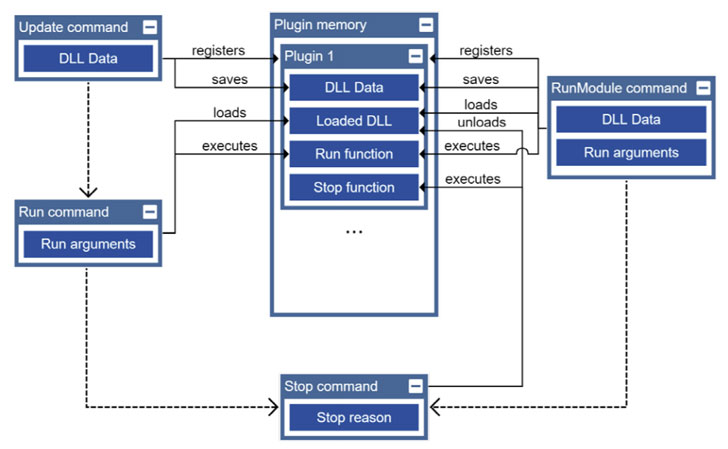
Written in C++, Sardonic not only usually takes steps to establish persistence on the compromised machine, but also will come outfitted with abilities that enable it to obtain technique information and facts, execute arbitrary commands, and load and execute further plugins, the final results of which are transmitted to a distant attacker-controlled server.
If just about anything, the latest development is nonetheless another indicator of FIN8’s shift in ways by strengthening its capabilities and malware shipping infrastructure. To mitigate the risk connected with economic malware, firms are proposed to independent their POS networks from all those made use of by personnel or attendees, teach staff to greater place phishing e-mail, and increase email security options to filter most likely suspicious attachments.
Observed this article interesting? Stick to THN on Facebook, Twitter and LinkedIn to study much more exceptional information we article.
Some elements of this write-up are sourced from:
thehackernews.com

 Microsoft Windows Security review: Minimum effort
Microsoft Windows Security review: Minimum effort