A new cyber mercenary hacker-for-seek the services of team dubbed “Void Balaur” has been connected to a string of cyberespionage and facts theft routines concentrating on thousands of entities as properly as human rights activists, politicians, and govt officers close to the globe at least since 2015 for economical gain while lurking in the shadows.
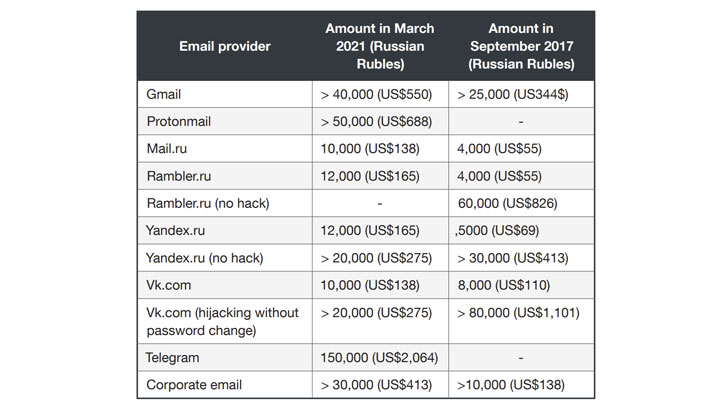
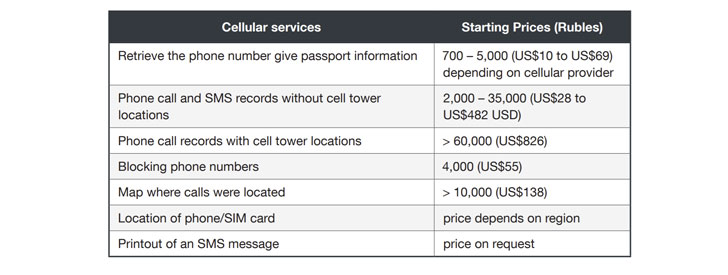
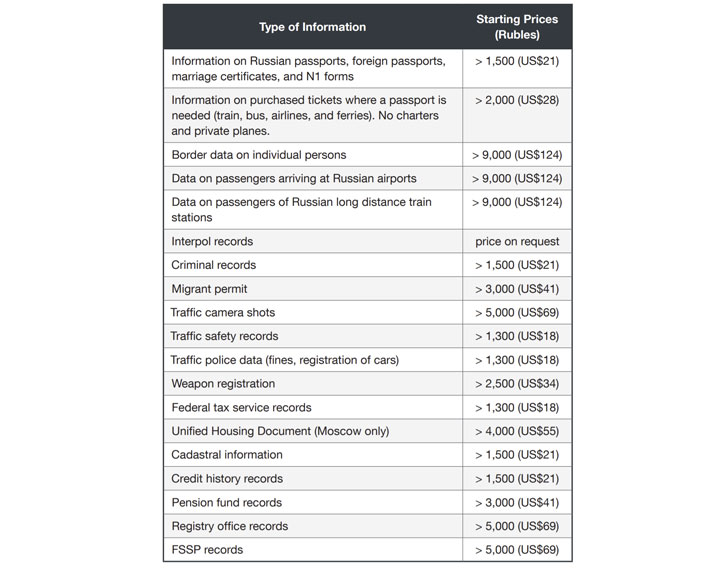
Named following a lots of-headed dragon from Romanian folklore, the adversary has been unmasked promotion its providers in Russian-talking underground message boards relationship all the way back again to 2017 and advertising troves of delicate info such as cell tower phone logs, passenger flight records, credit rating studies, banking knowledge, SMS messages, and passport details. The risk actor calls by itself “Rockethack.”
“This hacker-for-retain the services of team does not function out of a bodily building, nor does it have a shiny prospectus that describes its providers,” Pattern Micro researcher Feike Hacquebord mentioned in a freshly published profile of the collective.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

“The team does not attempt to wriggle out of a tough position by justifying its business enterprise, nor is it concerned in lawsuits in opposition to any individual attempting to report on their functions. Rather, this team is fairly open about what it does: breaking into email accounts and social media accounts for revenue,” Hacquebord additional.
Apart from gaining in the vicinity of unanimous beneficial evaluations on the boards for its capability to supply high-quality facts, Void Balaur is also thought to have centered on cryptocurrency exchanges by creating several phishing internet sites to trick cryptocurrency exchange customers in purchase to get unauthorized entry to their wallets. What is additional, the mercenary collective has deployed an details stealer named Z*Stealer and Android malware these types of as DroidWatcher from its targets.
Void Balaur’s intrusion set has been observed deployed from a vast vary of people today and entities, which includes journalists, human legal rights activists, politicians, scientists, health professionals functioning in IVF clinics, genomics and biotechnology firms, and telecom engineers. Pattern Micro mentioned it unearthed more than 3,500 email addresses the team set its aim on.
Most of the group’s targets are claimed to be found in Russia and other neighboring nations like Ukraine, Slovakia, and Kazakhstan, with victims also situated in the U.S., Israel, Japan, India, and European nations. Assaulted corporations operate the gamut from telecom companies, satellite conversation businesses, and fintech firms to ATM equipment suppliers, level-of-sale (PoS) vendors, and biotech firms.
“Void Balaur goes soon after the most non-public and particular information of corporations and people today then sells that info to whomever desires to pay out for it,” the scientists mentioned. The explanation why these folks and entities were being focused continues to be unfamiliar as still.
It can be not immediately distinct how delicate phone and email data are acquired from the targets without the need of conversation, while the scientists suspect that the menace actor could have possibly specifically (or indirectly) included rogue insiders at the concerned corporations to offer the info or by compromising accounts of critical workforce with accessibility to the focused email mailboxes.
Trend Micro’s deep-dive examination has also uncovered some frequent ground with an additional Russia-dependent sophisticated persistent danger team named Pawn Storm (aka APT28, Sofacy, or Iron Twilight), with overlaps noticed in the targeted email addresses concerning the two teams, although also considerably differing in a amount of techniques, which includes Void Balaur’s modus operandi of putting cryptocurrency buyers and their operational hrs.

If nearly anything, the growth when once more highlights the rampantly developing illicit mercenary-linked things to do in cyberspace and the need for these kinds of expert services, what with a quantity of operations — BellTroX (aka Dark Basin), Bahamut, CostaRicto, and PowerPepper — that have been uncovered as targeting money institutions and govt organizations in latest months.
To defend against the hacking attacks, it is really encouraged to permit two-factor authentication (2FA) by way of an authenticator app or a components security vital, depend on applications with conclude-to-close encryption (E2EE) for email and communications, and permanently delete aged, unwelcome messages to mitigate the risk of data publicity.
“The reality is that frequent internet people simply cannot quickly prevent a decided cyber mercenary,” the researchers concluded. “Whilst [advanced offensive tools in a cyber mercenary’s arsenal] may well be meant to be made use of in the battle in opposition to terrorism and organized criminal offense, the actuality is that they — knowingly or unknowingly — close up in the hands of menace actors who use it from unwitting targets.”
Found this posting interesting? Abide by THN on Facebook, Twitter and LinkedIn to read a lot more exclusive material we put up.
Some sections of this report are sourced from:
thehackernews.com


 Big zero-day flaw found in Palo Alto security appliance
Big zero-day flaw found in Palo Alto security appliance