An enterprise-quality surveillanceware dubbed Hermit has been set to use by entities working from inside of Kazakhstan, Syria, and Italy more than the decades considering that 2019, new investigate has discovered.
Lookout attributed the spy computer software, which is geared up to goal each Android and iOS, to an Italian company named RCS Lab S.p.A and Tykelab Srl, a telecom solutions company which it suspects to be a entrance firm. The San Francisco-dependent cybersecurity agency claimed it detected the marketing campaign aimed at Kazakhstan in April 2022.
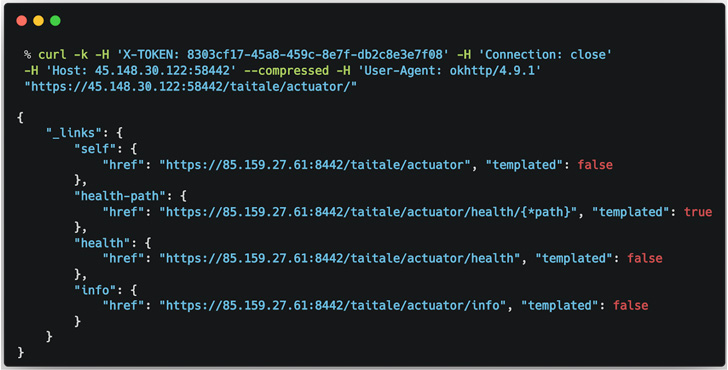
Hermit is modular and will come with myriad capabilities that let it to “exploit a rooted system, file audio and make and redirect phone phone calls, as properly as acquire data this sort of as simply call logs, contacts, pictures, product locale and SMS messages,” Lookout scientists Justin Albrecht and Paul Shunk stated in a new produce-up.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
The spyware is considered to be dispersed through SMS messages that trick customers into setting up what are seemingly innocuous apps from Samsung, Vivo, and Oppo, which, when opened, hundreds a web site from the impersonated business while stealthily activating the destroy chain in the background.

Like other Android malware threats, Hermit is engineered to abuse its obtain to accessibility providers and other main components of the running program (i.e., contacts, digital camera, calendar, clipboard, etc.) for most of its destructive routines.
Android units have been at the receiving close of spy ware in the previous. In November 2021, the risk actor tracked as APT-C-23 (aka Arid Viper) was joined to a wave of attacks concentrating on Center East customers with new variants of FrozenCell.
Then previous month, Google’s Risk Examination Group (TAG) disclosed that at minimum federal government-backed actors located in Egypt, Armenia, Greece, Madagascar, Côte d’Ivoire, Serbia, Spain, and Indonesia are getting Android zero-working day exploits for covert surveillance campaigns.
“RCS Lab, a identified developer that has been lively for more than three decades, operates in the exact marketplace as Pegasus developer NSO Team Technologies and Gamma Group, which produced FinFisher,” the researchers noted.
“Collectively branded as ‘lawful intercept’ businesses, they claim to only provide to clients with reputable use for surveillanceware, this kind of as intelligence and law enforcement organizations. In reality, this sort of tools have often been abused less than the guise of nationwide security to spy on small business executives, human legal rights activists, journalists, teachers and federal government officials.”

The conclusions appear as the Israel-primarily based NSO Team is reported to be reportedly in talks to offer off its Pegasus technology to U.S. defense contractor L3Harris, the company that manufactures StingRay cellular phone trackers, prompting problems that it could open the door for regulation enforcement’s use of the controversial hacking software.
The German maker at the rear of FinFisher has been courting problems of its personal in the wake of raids carried out by investigating authorities in link with suspected violations of foreign investing rules by way of offering its spy ware in Turkey without the need of acquiring the necessary license.
Before this March, it shut down its operations and submitted for insolvency, Netzpolitik and Bloomberg noted, including, “the business has been dissolved, the employees have been laid off, and company functions have ceased.”
Located this write-up appealing? Stick to THN on Facebook, Twitter and LinkedIn to study a lot more special articles we write-up.
Some elements of this article are sourced from:
thehackernews.com

 China-linked APT Flew Under Radar for Decade
China-linked APT Flew Under Radar for Decade