Iran has been joined to still an additional condition-sponsored ransomware procedure as a result of a contracting corporation dependent in the state, in accordance to new investigation.
“Iran’s Islamic Groundbreaking Guard Corps (IRGC) was functioning a state-sponsored ransomware marketing campaign by way of an Iranian contracting corporation named ‘Emen Net Pasargard’ (ENP),” cybersecurity business Flashpoint explained in its results summarizing 3 files leaked by an anonymous entity named Read through My Lips or Lab Dookhtegan between March 19 and April 1 by means of its Telegram channel.
Dubbed “Project Signal,” the initiative is claimed to have kickstarted sometime between late July 2020 and early September 2020, with ENP’s inner investigate group, named the “Reports Centre,” putting with each other a list of unspecified concentrate on internet sites.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

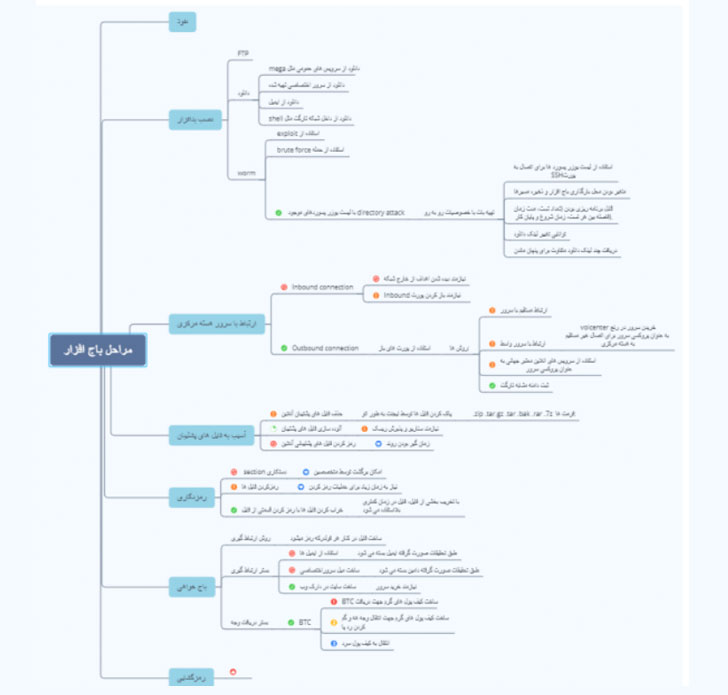
A next spreadsheet validated by Flashpoint explicitly spelled out the project’s fiscal motivations, with plans to start the ransomware operations in late 2020 for a period of time of 4 times amongst Oct. 18 and 21. A different doc outlined the workflows, which includes ways for getting Bitcoin payments from ransomware victims and decrypting the locked info.
It can be not immediately crystal clear if these attacks went in advance as planned and whom they qualified.
“ENP operates on behalf of Iran’s intelligence expert services furnishing cyber abilities and assist to Iran’s Islamic Innovative Guard Corps (IRGC), the IRGC Quds Power (IRGC-QF), and Iran’s Ministry of Intelligence and Security (MOIS),” the scientists explained.
Inspite of the project’s ransomware themes, the scientists suspect the go could possible be a “subterfuge procedure” to mimic the methods, procedures, and strategies (TTPs) of other economically enthusiastic cybercriminal ransomware teams so as to make attribution more difficult and improved blend in with the menace landscape.
Apparently, the rollout of Project Signal also dovetailed with yet another Iranian ransomware marketing campaign named “Shell out2Crucial,” which ensnared dozens of Israeli companies in Nov. and Dec. 2020. Tel Aviv-based cybersecurity business ClearSky attributed the wave of attacks to a group called Fox Kitten. Presented the deficiency of proof, it can be mysterious what link, if any, the two strategies may have with every single other.
This is not the first time Lab Dookhtegan has dumped very important info pertaining to Iran’s malicious cyber activities. In a style echoing the Shadow Brokers, Lab Dookhtegan earlier spilled the secrets and techniques of an Iranian hacker team identified as APT34 or OilRig, including publishing the adversary’s arsenal of hacking instruments, along with info on 66 sufferer companies and doxxing the real-earth identities of members of Iranian govt intelligence brokers.
Information of Iran’s new ransomware operation also comes as a coalition of governing administration and tech corporations in the personal sector, referred to as the Ransomware Undertaking Power, shared a 81-website page report comprising a record of 48 suggestions to detect and disrupt ransomware attacks, in addition to supporting organizations prepare and answer to these intrusions additional correctly.
Located this article fascinating? Abide by THN on Fb, Twitter and LinkedIn to read much more distinctive information we post.
Some elements of this write-up are sourced from:
thehackernews.com


 New Chinese Malware Targeted Russia’s Largest Nuclear Submarine Designer
New Chinese Malware Targeted Russia’s Largest Nuclear Submarine Designer