Getty Visuals
A mysterious and impressive rootkit has been uncovered that is said to have remained concealed and exploited in attacks because 2016.
Dubbed ‘CosmicStrand’, Kaspersky scientists stated the UEFI rootkit was found on a variety of victims’ equipment throughout China, Russia, Iran, and Vietnam.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The destructive rootkit was uncovered on Asus and Gigabyte motherboards that shared the H81 chipset, unveiled between 2013 and 2015, indicating there may be a typical vulnerability throughout this devices which has largely been discontinued.
UEFI malware is not much too common, but there has been a slight improve in attacks in latest several years, with far more study uncovering strategies these as MoonBounce and LoJax.
Kaspersky predicts attacks of this mother nature will maximize in the many years to occur, as does the US authorities which, in February 2022, posted a report detailing how the increase of UEFI malware was “an alarming trend” and these attacks witnessed in the wild “were formerly only theoretical”.
Rootkits are an eye-catching resource for attackers simply because they are notably difficult to locate and investigation, getting embedded within a motherboard’s firmware image. For the reason that of this, they afford attackers substantial abilities many thanks to a low risk of detection. It can be possible that the computer system will be infected with the rootkit without end, the report go through.
The researchers were unable to ascertain how the victims initially turned infected, but earlier investigation from Qihoo360 on an early variant identified in 2017 alleged that a victim may well have acquired an infected motherboard from a second-hand merchant, even though this has not been verified.
The researchers included that creating a rootkit of this high quality is specifically challenging, mainly simply because a UEFI execution context terminates just before Windows is loaded, creating it more difficult for the UEFI code to be transposed into Windows.
The industry experts suggested it’s even much more intriguing that the victims appeared to be private people today, not tied to any organisation or marketplace, given the technical expertise needed to construct it.
Commonly developers of malware would concentrate on large-value people in get to exfiltrate data, or deploy payloads this kind of as ransomware in economically-pushed campaigns.
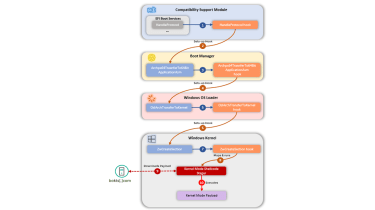
CosmicStrand’s an infection chain
Kaspersky
The kernel-level implant deploys a destructive component in Windows every single time the functioning process (OS) loads. After the an infection chain is finish and the implant is linked to the cyber criminal’s C2 infrastructure, attackers can then feed malicious code to assemble into shellcode.
Kaspersky said it was in a position to capture and analyse an case in point of this shellcode but it believes numerous far more exist that it wasn’t able to discover.
From its analysis, the code appeared to attempt to build a new consumer on the victim’s device. The researchers said it can be inferred from the shellcodes that they could be stagers for attacker-provided portable executables – a Windows file structure that wraps executable code, dynamic backlink libraries (DLLs) and other code for later on use.
The scientists stated they are not sure pertaining to whom or what group they can attribute the attack to, but there is evidence to suggest a Chinese-talking danger actor could be behind it.
The principal reason Kaspersky believes a Chinese-talking attacker could be driving it is the similarity in some code snippets among CosmicStrand and the MyKings botnet. Located in 2020 by ESET, the researchers stated at the time they noticed numerous artefacts exhibiting the Chinese language.
CosmicStrand and MyKings use the very same MBR rootkit to build persistence, both of those generate network packets in the identical way and the API hashing code is also equivalent. The algorithm employed below has only been observed 2 times by Kaspersky – in MoonBounce and xTalker – the two of which are tied to Chinese-talking threat actors, it said.
“The various rootkits found out so far proof a blind spot in our industry that needs to be addressed faster somewhat than afterwards,” stated the scientists.
“The most striking element of this report is that this UEFI implant appears to be to have been made use of in the wild due to the fact the finish of 2016… this discovery begs a last problem: if this is what the attackers were applying back then, what are they utilizing today?”
Some sections of this report are sourced from:
www.itpro.co.uk

 DataGrail hires former Shopify VP Cathy Polinsky as CTO
DataGrail hires former Shopify VP Cathy Polinsky as CTO