Cybersecurity researchers disclosed details of what they say is the “most significant botnet” noticed in the wild in the last six decades, infecting around 1.6 million devices mainly located in China, with the intention of launching distributed denial-of-services (DDoS) attacks and inserting commercials into HTTP sites frequented by unsuspecting end users.
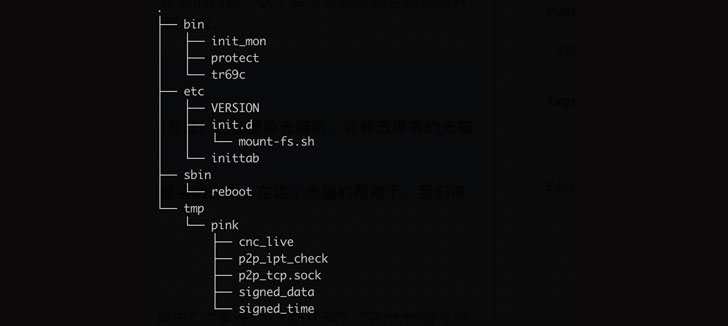
Qihoo 360’s Netlab security group dubbed the botnet “Pink” primarily based on a sample received on November 21, 2019, owing to a big selection of purpose names commencing with “pink.”


Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code
Mainly concentrating on MIPS-based mostly fiber routers, the botnet leverages a mix of 3rd-party solutions such as GitHub, peer-to-peer (P2P) networks, and central command-and-management (C2) servers for its bots to controller communications, not to point out fully encrypting the transmission channels to stop the victimized gadgets from currently being taken over.
“Pink raced with the seller to keep command more than the infected devices, although seller manufactured repeated tries to deal with the dilemma, the bot learn recognized the vendor’s action also in authentic time, and made many firmware updates on the fiber routers correspondingly,” the scientists claimed in an analysis revealed very last 7 days adhering to coordinated action taken by the unspecified seller and China’s Personal computer Network Emergency Response Complex Team/Coordination Center (CNCERT/CC).
Curiously, Pink has also been found adopting DNS-Above-HTTPS (DoH), a protocol employed for executing distant Area Title Method resolution through the HTTPS protocol, to connect to the controller specified in a configuration file that is shipped both by using a GitHub or Baidu Tieba as effectively as a constructed-in area name tricky-coded into some of the samples.
Much more than 96% of the zombie nodes portion of the “super-substantial-scale bot network” ended up positioned in China, Beijing-primarily based cybersecurity firm NSFOCUS noted in an independent report, with the risk actor breaking into the equipment to put in malicious applications by taking advantage of zero-working day vulnerabilities in the network gateway gadgets. Though a sizeable chunk of the contaminated gadgets has since been fixed and restored to their past point out as of July 2020, the botnet is however said to be lively, comprising about 100,000 nodes.
With practically 100 DDoS attacks obtaining been launched by the botnet to day, the conclusions are still one more indication as to how botnets can present a powerful infrastructure for terrible actors to mount a assortment of intrusions. “Internet of Issues equipment have grow to be an essential purpose for black creation companies and even state-of-the-art persistent threats (APT) corporations,” NSFOCUS scientists claimed. “Although Pink is the greatest botnet ever identified, it will in no way be the very last 1.”
Uncovered this post appealing? Abide by THN on Facebook, Twitter and LinkedIn to read through additional exclusive written content we put up.
Some components of this write-up are sourced from:
thehackernews.com

 Police Arrest Suspected Ransomware Hackers Behind 1,800 Attacks Worldwide
Police Arrest Suspected Ransomware Hackers Behind 1,800 Attacks Worldwide