A formerly undocumented Linux malware with backdoor capabilities has managed to keep under the radar for about 3 many years, enabling the risk actor behind to harvest and exfiltrate sensitive details from contaminated programs.
Dubbed “RotaJakiro” by researchers from Qihoo 360 NETLAB, the backdoor targets Linux X64 devices, and is so named immediately after the reality that “the spouse and children utilizes rotate encryption and behaves differently for root/non-root accounts when executing.”


Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The conclusions arrive from an evaluation of a malware sample it detected on March 25, despite the fact that early variations seem to have been uploaded to VirusTotal as early as Could 2018. A overall of 4 samples have been found to day on the databases, all of which stay undetected by most anti-malware engines. As of writing, only 7 security suppliers flag the most recent variation of the malware as destructive.
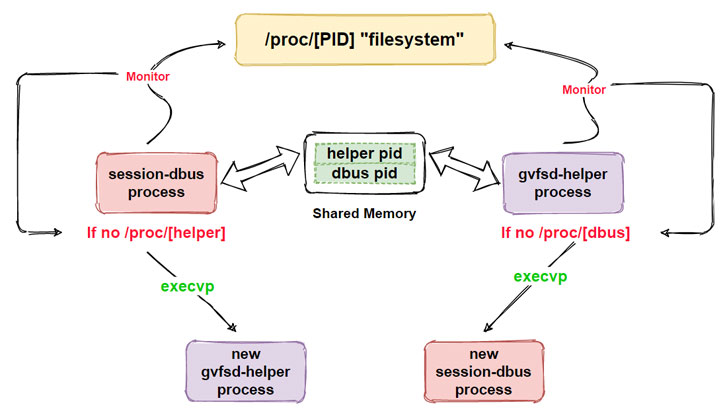
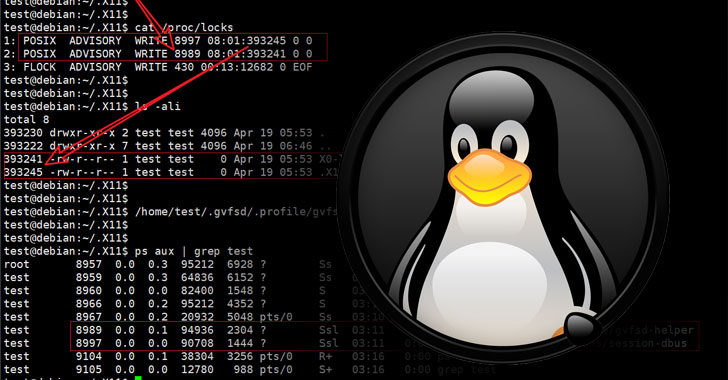
“At the useful level, RotaJakiro very first decides regardless of whether the user is root or non-root at run time, with diverse execution procedures for distinct accounts, then decrypts the related delicate sources using AES& ROTATE for subsequent persistence, course of action guarding and solitary instance use, and ultimately establishes communication with C2 and waits for the execution of commands issued by C2,” the researchers described.
RotaJakiro is intended with stealth in mind, relying on a mix of cryptographic algorithms to encrypt its communications with a command-and-control (C2) server, in addition to possessing guidance for 12 capabilities that just take treatment of accumulating product metadata, thieving sensitive information and facts, carrying out file similar operations, and downloading and executing plug-ins pulled from the C2 server.

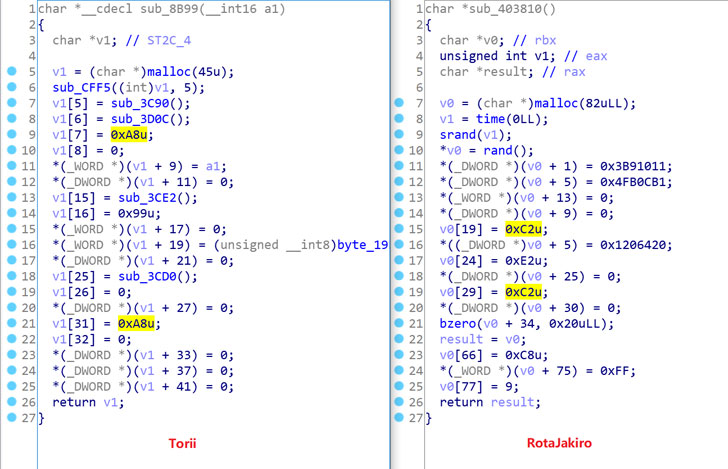
But with no evidence to get rid of light-weight on the character of plugins, the true intent driving the malware campaign continues to be unclear. Curiously, some of the C2 domains were registered dating all the way back again to December 2015, with the researchers also observing overlaps involving RotaJakiro and a botnet named Torii.
“From the viewpoint of reverse engineering, RotaJakiro and Torii share equivalent variations: the use of encryption algorithms to cover sensitive resources, the implementation of a instead aged-university design and style of persistence, structured network targeted visitors, and many others.,” the scientists mentioned. “We do not just know the answer, but it seems that RotaJakiro and Torii have some connections.”
Found this short article intriguing? Adhere to THN on Fb, Twitter and LinkedIn to browse more distinctive material we publish.
Some components of this article are sourced from:
thehackernews.com

 Can the Bytecode Alliance secure the supply chain with WebAssembly?
Can the Bytecode Alliance secure the supply chain with WebAssembly?