A not too long ago uncovered hacking team recognized for concentrating on employees dealing with corporate transactions has been connected to a new backdoor called Danfuan.
This hitherto undocumented malware is shipped by way of an additional dropper called Geppei, researchers from Symantec, by Broadcom Software program, stated in a report shared with The Hacker News.
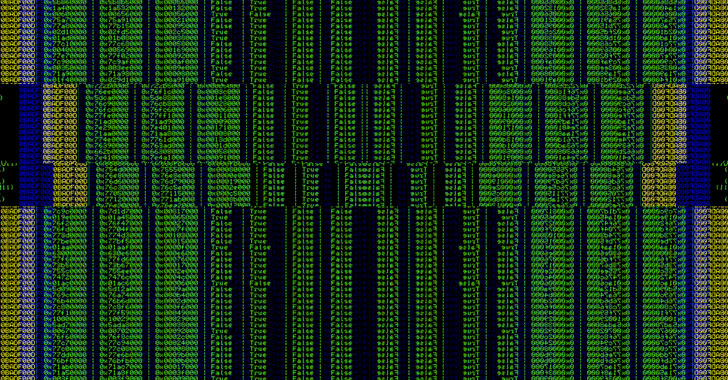
The dropper “is staying made use of to put in a new backdoor and other instruments using the novel strategy of reading instructions from seemingly innocuous Internet Data Services (IIS) logs,” the researchers explained.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The toolset has been attributed by the cybersecurity firm to a suspected espionage actor termed UNC3524, aka Cranefly, which to start with arrived to gentle in May 2022 for its aim on bulk email collection from victims who offer with mergers and acquisitions and other money transactions.
A person of the group’s crucial malware strains is QUIETEXIT, a backdoor deployed on network appliances that do not aid antivirus or endpoint detection, this kind of as load balancers and wi-fi access position controllers, enabling the attacker to escape detection for prolonged intervals of time.
Geppei and Danfuan increase to Cranefly’s custom made cyber weaponry, with the previous acting a dropper by looking through instructions from IIS logs that masquerade as harmless web entry requests despatched to a compromised server.
“The commands study by Geppei comprise malicious encoded .ashx documents,” the scientists observed. “These documents are saved to an arbitrary folder determined by the command parameter and they run as backdoors.”

This consists of a web shell known as reGeorg, which has been place to use by other actors like APT28, DeftTorero, and Worok, and a in no way-right before-observed malware dubbed Danfuan, which is engineered to execute obtained C# code.
Symantec said it has not noticed the danger actor exfiltrating facts from target machines despite a prolonged dwell time of 18 months on compromised networks.
“The use of a novel procedure and customized equipment, as well as the steps taken to conceal traces of this exercise on sufferer devices, point out that Cranefly is a fairly competent risk actor,” the researchers concluded.
“The instruments deployed and efforts taken to conceal this action […] show that the most very likely determination for this group is intelligence gathering.”
Observed this posting appealing? Adhere to THN on Facebook, Twitter and LinkedIn to go through far more exceptional written content we article.
Some elements of this report are sourced from:
thehackernews.com

 IT Pro News: Medibank cyber attack, Microsoft record cloud revenue, See Tickets data breach
IT Pro News: Medibank cyber attack, Microsoft record cloud revenue, See Tickets data breach