SunCrypt, a ransomware pressure that went on to infect various targets last 12 months, may be an updated edition of the QNAPCrypt ransomware, which qualified Linux-based mostly file storage systems, in accordance to new study.
“Though the two ransomware [families] are operated by unique distinctive danger actors on the dark web, there are solid technological connections in code reuse and methods, linking the two ransomware to the exact same writer,” Intezer Lab researcher Joakim Kennedy explained in a malware examination published right now revealing the attackers’ ways on the dark web.
Very first identified in July 2019, QNAPCrypt (or eCh0raix) is a ransomware relatives that was uncovered to target Network Hooked up Storage (NAS) products from Taiwanese organizations QNAP Systems and Synology. The products had been compromised by brute-forcing weak qualifications and exploiting known vulnerabilities with the objective of encrypting files found in the program.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
The ransomware has considering the fact that been tracked to a Russian cybercrime team referred to as “FullOfDeep,” with Intezer shutting down as many as 15 ransomware strategies applying the QNAPCrypt variant with denial of services attacks focusing on a listing of static bitcoin wallets that were being developed for the express intent of accepting ransom payments from victims, and avert long run bacterial infections.
SunCrypt, on the other hand, emerged as a Windows-based ransomware instrument prepared at first in Go in October 2019, before it was ported to a C/C++ version in mid-2020. Apart from stealing victims’ data prior to encrypting the documents and threatening with public disclosure, the team has leveraged distributed denial-of-support (DDoS) attacks as a secondary extortion tactic to stress victims into having to pay the demanded ransom.
Most just lately, the ransomware was deployed to focus on a New South Wales-centered professional medical diagnostics enterprise called PRP Diagnostic Imaging on December 29, which concerned the theft of “a tiny quantity of affected individual documents” from two of its administrative file servers.
Even though the two ransomware people have directed their attacks versus distinctive running programs, reviews of SunCrypt’s connections to other ransomware groups have been beforehand speculated.
Indeed, blockchain examination business Chainalysis previously last thirty day period quoted a “privately circulated report” from menace intelligence firm Intel 471 that claimed representatives from SunCrypt explained their strain as a “rewritten and rebranded version of a ‘well-known’ ransomware pressure.”
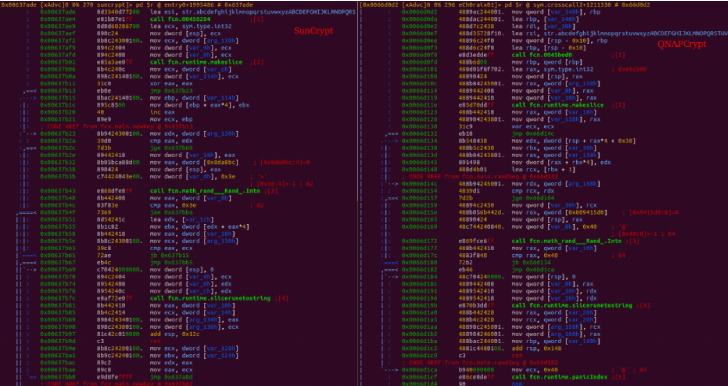
Now according to Intezer’s assessment of the SunCrypt Go binaries, not only does the ransomware share very similar encryption capabilities with QNAPCrypt, but also in the file varieties encrypted and the solutions made use of to produce the encryption password as nicely as execute system locale checks to ascertain if the machine in dilemma is positioned in a disallowed region.
Also of note is the simple fact that both of those QNAPCrypt and SunCrypt make use of the ransomware-as-a-assistance (RaaS) design to promote their instruments on underground forums, wherein affiliate marketers carry out the ransomware attacks on their own and spend a percentage of each and every victim’s payment back to the strain’s creators and directors.
Taking into account the overlaps and the behavioral dissimilarities between the two groups, Intezer suspects that “the eCh0raix ransomware was transferred to and upgraded by the SunCrypt operators.”
“Although the technological based proof strongly provides a url in between QNAPCrypt and the earlier variation of SunCrypt, it is clear that equally ransomware are operated by unique people today,” the researchers concluded.
“Centered on the out there knowledge, it is not achievable to hook up the activity among the two actors on the discussion board. This indicates that when new malware services derived from older expert services show up, they could not always be operated by the exact folks.”
Uncovered this post attention-grabbing? Abide by THN on Facebook, Twitter and LinkedIn to study additional exclusive written content we put up.
Some components of this posting are sourced from:
thehackernews.com


 Kaspersky to Co-Chair Working Group of the Paris Call
Kaspersky to Co-Chair Working Group of the Paris Call