Cybersecurity researchers have disclosed a new kind of Business office malware dispersed as component of a destructive email campaign that qualified extra than 80 buyers around the world in an try to handle sufferer devices and steal information remotely.
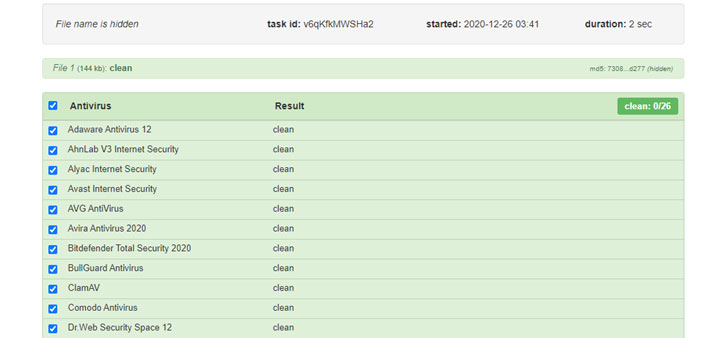
The software — dubbed “APOMacroSploit” — is a macro exploit generator that will allow the user to build an Excel doc able of bypassing antivirus software, Windows Antimalware Scan Interface (AMSI), and even Gmail and other email-based mostly phishing detection.
APOMacroSploit is believed to be the operate of two French-centered danger actors “Apocaliptique” and “Nitrix,” who are believed to have built at the very least $5000 in fewer than two months advertising the product or service on HackForums.net.

Protect and backup your data using AOMEI Backupper. AOMEI Backupper takes secure and encrypted backups from your Windows, hard drives or partitions. With AOMEI Backupper you will never be worried about loosing your data anymore.
Get AOMEI Backupper with 72% discount from an authorized distrinutor of AOMEI: SerialCart® (Limited Offer).
➤ Activate Your Coupon Code

About 40 hackers in whole are stated to be driving the procedure, using 100 various email senders in a slew of attacks concentrating on users in more than 30 distinctive nations around the world. The attacks were being spotted for the 1st time at the close of November 2020, according to cybersecurity business Test Level.
“The malware infection begins when the dynamic material of the connected XLS doc is enabled, and an XLM macro instantly starts off downloading a Windows technique command script,” the business claimed in a Tuesday report.
This program command script is retrieved from cutt.ly, which directs to servers hosting numerous BAT scripts that have the nickname of the buyers inserted connected to the filenames. The scripts are also dependable for executing the malware (“fola.exe”) on Windows methods, but not right before incorporating the malware spot in the exclusion route of Windows Defender and disabling Windows cleanup.
In a single of the attacks, the malware — a Delphi Crypter followed by a 2nd-stage distant accessibility Trojan termed BitRAT — was observed hosted on a Bulgarian web page catering to health-related equipment and supplies, implying that the attackers breached the web-site to retail store the destructive executable.
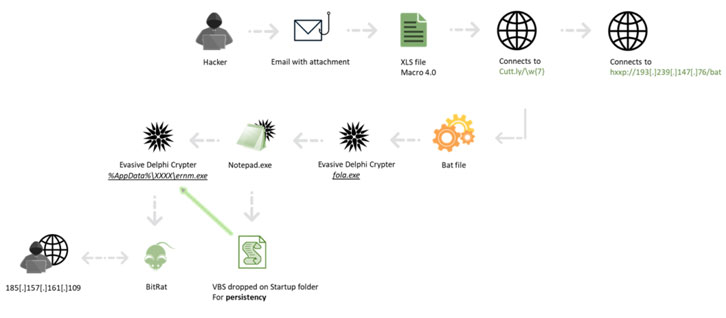
The notion of utilizing “crypters” or “packers” has become increasingly well known among the risk actors to not only compress but also to make malware samples extra evasive and reverse engineer.
BitRAT, which was formally documented past August, will come with functions to mine cryptocurrencies, hack webcams, log keystrokes, down load and upload arbitrary information, and remotely management the procedure via a command-and-management server, which in this case resolved to a sub-domain of a respectable Bulgarian internet site for video clip surveillance systems.
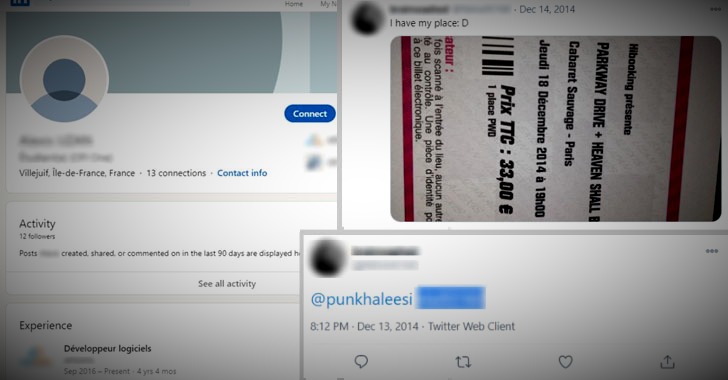
Even further investigation by Examine Issue included chasing the electronic path left by the two operators — including two League of Legends participant profiles — in the end main the researchers to unmask the authentic identity of Nitrix, who revealed his genuine name on Twitter when he posted a photograph of a ticket he purchased for a concert in December 2014.
Though Nitrix is a program developer from Noisy-Le-Grand with four a long time of expertise as a software package developer, Apocaliptique’s use of option names this sort of as “apo93” or “apocaliptique93” has stirred up opportunities that the individual may also be a French resident, as “93” is the colloquial name for the French section of Seine-Saint-Denis.
Examine Stage Exploration said it had alerted law enforcement authorities about the identities of the attackers.
Uncovered this report fascinating? Comply with THN on Fb, Twitter and LinkedIn to read extra distinctive content material we submit.
Some sections of this article are sourced from:
thehackernews.com

 YouTube Terminates 3000 Channels in Russia and China Clampdown
YouTube Terminates 3000 Channels in Russia and China Clampdown