Cybersecurity scientists on Wednesday drop light-weight on a new sophisticated backdoor focusing on Linux endpoints and servers that is believed to be the function of Chinese nation-point out actors.
Dubbed “RedXOR” by Intezer, the backdoor masquerades as a polkit daemon, with similarities identified involving the malware and individuals previously involved with the Winnti Umbrella (or Axiom) menace team this sort of as PWNLNX, XOR.DDOS and Groundhog.
RedXOR’s identify arrives from the actuality that it encodes its network data with a scheme dependent on XOR, and that it is compiled with a legacy GCC compiler on an outdated launch of Pink Hat Organization Linux, suggesting that the malware is deployed in targeted attacks versus legacy Linux techniques.

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount
Intezer explained two samples of the malware ended up uploaded from Indonesia and Taiwan all over Feb. 23-24, both equally international locations that are identified to be singled out by China-primarily based danger groups.
Apart from the overlaps in terms of the overall move and functionalities and the use of XOR encoding in between RedXOR and PWNLNX, the backdoor takes the variety of an unstripped 64-bit ELF file (“po1kitd-update-k”), full with a typosquatted title (“po1kitd” vs. “polkitd”), which, on execution, proceeds to produce a hidden directory to store information similar to the malware, right before putting in by itself on the machine.
Polkit (née PolicyKit) is a toolkit for defining and managing authorizations, and is applied for enabling unprivileged procedures to converse with privileged procedures.
In addition, the malware will come with an encrypted configuration that homes the command-and-regulate (C2) IP handle and port, and the password it requires to authenticate to the C2 server, prior to creating connection about a TCP socket.
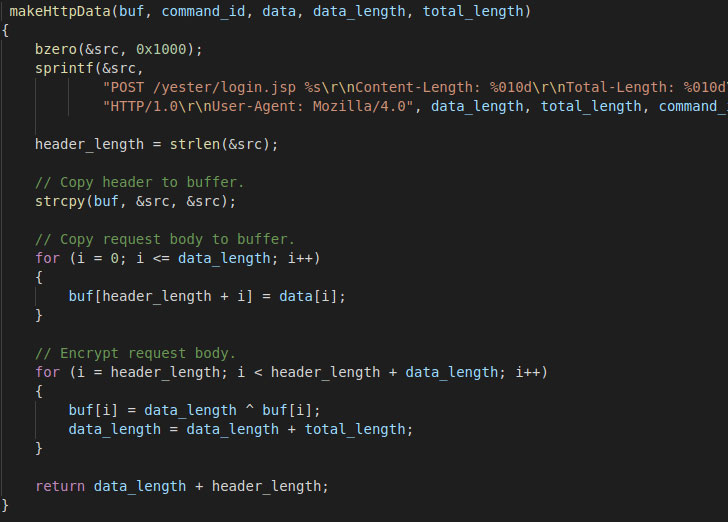
What is actually a lot more, the communications are not only disguised as harmless HTTP site visitors, but are also encoded both means utilizing an XOR encryption scheme, the results of which are decrypted to expose the correct command to be operate.
RedXOR supports a multitude of capabilities, such as accumulating method information and facts (MAC address, username, distribution, clock velocity, kernel model, and so forth.), performing file functions, executing instructions with system privileges, operating arbitrary shell commands, and even choices to remotely update the malware.
Buyers victimized by RedXOR can acquire protective steps by killing the system and getting rid of all information similar to the malware.
If nearly anything, the most current development factors to an improve in the variety of energetic strategies concentrating on Linux units, in portion owing to popular adoption of the working process for IoT units, web servers, and cloud servers, main attackers to port their existing Windows resources to Linux or establish new tools that assist each platforms.
“Some of the most outstanding country-condition actors are incorporating offensive Linux capabilities into their arsenal and it can be anticipated that both equally the range and sophistication of these kinds of attacks will maximize around time,” Intezer scientists outlined in a 2020 report charting the last decade of Linux APT attacks.
Observed this article intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to read much more exclusive information we put up.
Some parts of this write-up are sourced from:
thehackernews.com


 10 groups now targeting Hafnium Microsoft Exchange vulnerabilities
10 groups now targeting Hafnium Microsoft Exchange vulnerabilities