Cybersecurity researchers on Tuesday took the wraps off four up-and-coming ransomware teams that could pose a critical danger to enterprises and critical infrastructure, as the ripple outcome of a current spurt in ransomware incidents demonstrate that attackers are increasing additional complex and more rewarding in extracting payouts from victims.
“Whilst the ransomware disaster seems poised to get worse in advance of it receives much better, the cast of cybercrime teams that lead to the most harm is consistently modifying,” Palo Alto Networks’ Device 42 risk intelligence team stated in a report shared with The Hacker News.
“Groups occasionally go peaceful when they have obtained so significantly notoriety that they become a precedence for regulation enforcement. Some others reboot their functions to make them more rewarding by revising their strategies, strategies and techniques, updating their application and launching marketing and advertising campaigns to recruit new affiliate marketers.”

Protect your privacy by Mullvad VPN. Mullvad VPN is one of the famous brands in the security and privacy world. With Mullvad VPN you will not even be asked for your email address. No log policy, no data from you will be saved. Get your license key now from the official distributor of Mullvad with discount: SerialCart® (Limited Offer).
➤ Get Mullvad VPN with 12% Discount

The development will come as ransomware attacks are obtaining even larger and a lot more regular, growing in sizing and severity, while also evolving outside of economical extortion to an urgent national security and safety issue that has threatened universities, hospitals, businesses, and governments across the world, prompting intercontinental authorities to formulate a series of steps versus both equally operators of ransomware and the broader ecosystem of IT and funds laundering infrastructure which is abused to siphon resources.
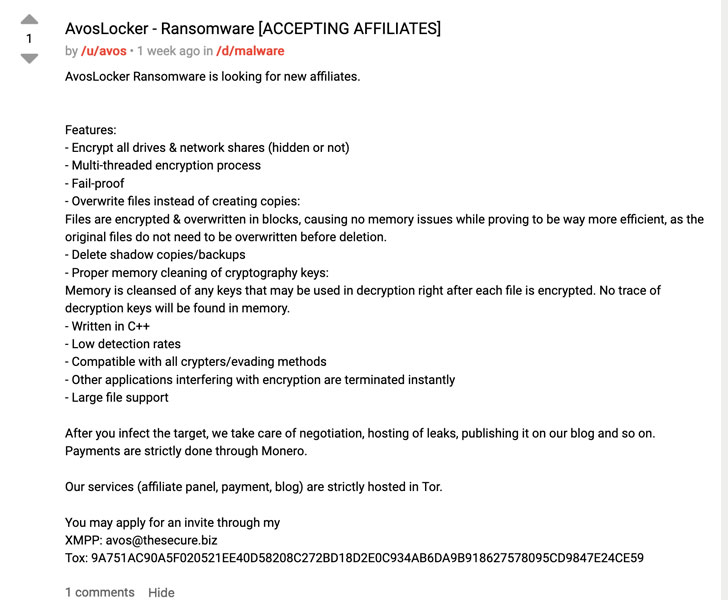
Main among the new entrants is AvosLocker, a ransomware-as-a-service (RaaS) group that commenced functions in late June by using “push releases” that are branded with a blue beetle logo to recruit new affiliate marketers. The cartel, which also operates a facts leak and extortion internet site, is explained to have breached 6 corporations in the U.S., U.K., U.A.E., Belgium, Spain, and Lebanon, with ransom calls for ranging any place from $50,000 to $75,000.
In contrast, Hive, irrespective of opening store in the exact same month as AvosLocker, has now strike numerous health care suppliers and mid-sizing organizations, like a European airline corporation and three U.S.-centered entities, amid other victims situated in Australia, China, India, Netherlands, Norway, Peru, Portugal, Switzerland, Thailand, and the U.K.
Also detected in the wild is a Linux variant of the HelloKitty ransomware, which singles out Linux servers functioning VMware’s ESXi hypervisor. “The observed variants impacted five corporations in Italy, Australia, Germany, the Netherlands and the U.S.,” Unit 42 scientists Doel Santos and Ruchna Nigam explained. “The maximum ransom need noticed from this group was $10 million, but at the time of producing, the menace actors have only been given 3 transactions that sum up to about $1.48 million.”

Past to be part of the record is LockBit 2., an recognized ransomware group that resurfaced in June with 2. model of their affiliate method touting its “unparalleled rewards” of “encryption pace and self-spread perform.” Not only do the builders assert it can be “the speediest encryption software package all over the earth,” the team presents a stealer named StealBit that enables the attackers to obtain victims’ data.
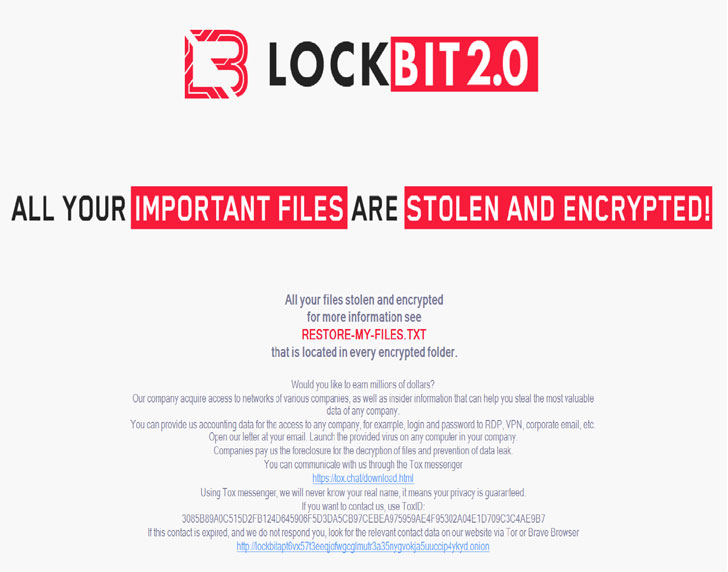
Considering the fact that its June 2021 debut, LockBit 2. has compromised 52 businesses in accounting, automotive, consulting, engineering, finance, higher-tech, hospitality, insurance plan, law enforcement, authorized solutions, manufacturing, non-revenue vitality, retail, transportation, and logistics industries spanning across Argentina, Australia, Austria, Belgium, Brazil, Germany, Italy, Malaysia, Mexico, Romania, Switzerland, the U.K., and the U.S.
If just about anything, the emergence of new ransomware variants show that cybercriminals are doubling down on ransomware attacks, underscoring the extremely financially rewarding nature of the crime.
“With significant ransomware groups this kind of as REvil and DarkSide lying very low or rebranding to evade legislation enforcement warmth and media notice, new teams will emerge to swap the kinds that are no more time actively focusing on victims,” the researchers mentioned. “Whilst LockBit and HelloKitty have been previously lively, their the latest evolution helps make them a fantastic example on how old groups can re-arise and stay persistent threats.”
Identified this short article intriguing? Adhere to THN on Facebook, Twitter and LinkedIn to examine much more unique content we publish.
Some sections of this post are sourced from:
thehackernews.com

 Mass Exploitation of Exchange Server ProxShell Bugs
Mass Exploitation of Exchange Server ProxShell Bugs